Scammers Evade Blocking Using VoIP and Reused Windows
Phone-based scams are rapidly evolving, outpacing many existing security filters. Attackers increasingly leverage Voice over Internet Protocol (VoIP) numbers, which are discarded before detection...
Phone-based scams are rapidly evolving, outpacing many existing security filters. Attackers increasingly leverage Voice over Internet Protocol (VoIP) numbers, which are discarded before detection systems can flag them. This tactic leaves users vulnerable and security teams struggling to keep pace.
These scam campaigns arrive through email, where attackers embed phone numbers directly into message bodies, subject lines, and file attachments.
The goal is simple: get the recipient to call a fraudulent number and hand over sensitive personal or financial details. By keeping victims on a live call, scammers can manipulate targets far more effectively than a link or attachment alone ever could.
Researchers at Cisco Talos identified that this shift toward phone-oriented attack delivery, known as telephone-oriented attack delivery (TOAD), has become one of the leading tactics in modern email threats.
Their analysis, covering a study window from late February to late March 2025, found that the largest scam campaigns all relied on VoIP infrastructure to operate at scale with minimal cost.
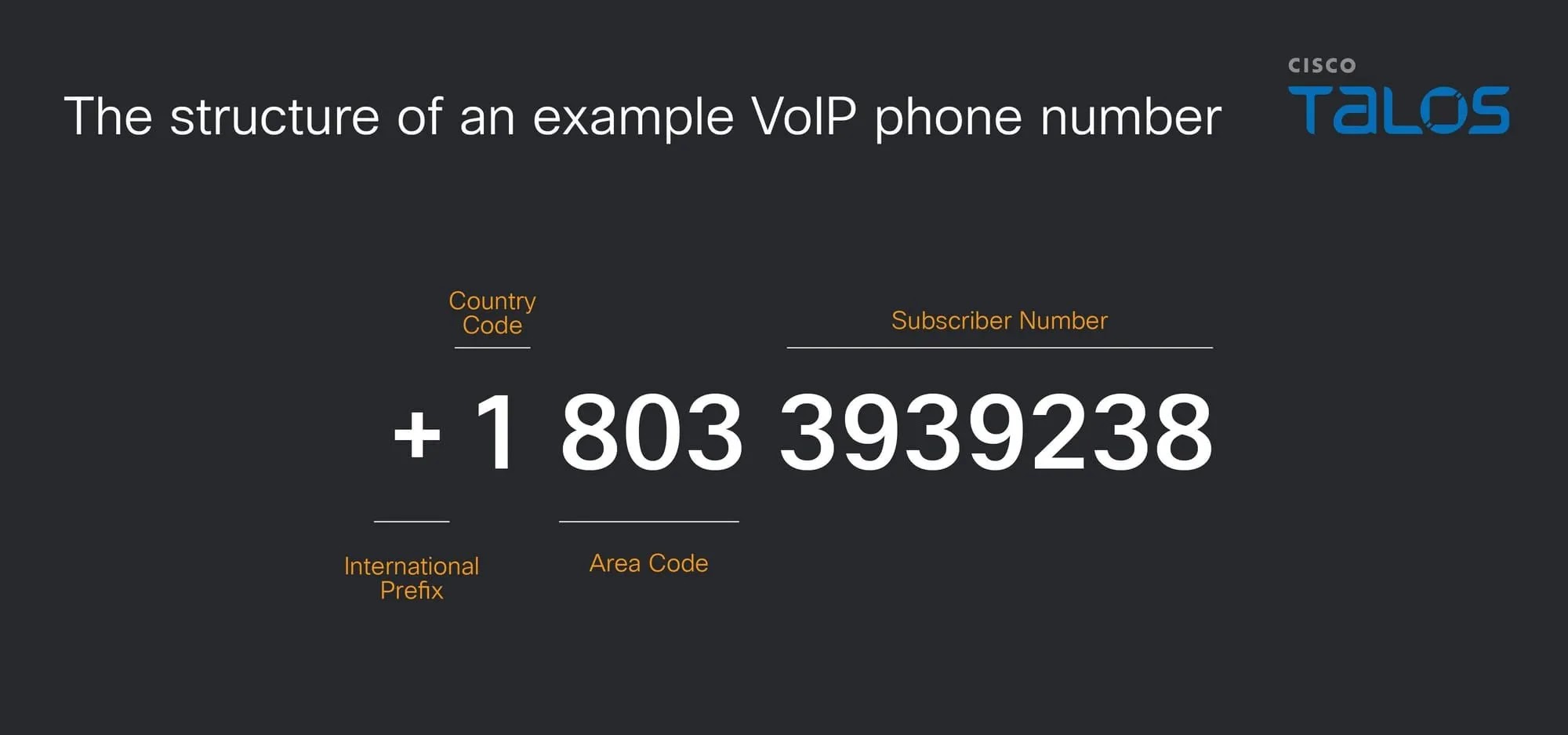
Scammers Game the System With VoIP Numbers
What makes VoIP so appealing to scammers is how easily numbers can be obtained and discarded in bulk. With API-driven provisioning available from a small number of providers, threat actors spin up hundreds of numbers quickly, use them briefly, and abandon them before reputation systems catch on. The median phone number lifespan observed during the study was roughly 14 days.
The impact goes well beyond individual users. Organized scam call centers are running campaigns that impersonate major brands like PayPal, Geek Squad, McAfee, and Norton LifeLock, all while directing victims to the same centralized fraudulent operation.
This infrastructure is deliberately built to resist tracing, blending seamlessly into legitimate telecom networks worldwide.
Scammers are not randomly picking phone numbers. They deliberately acquire large sequential blocks of numbers, often by purchasing Direct Inward Dialing (DID) blocks from providers.
When one number gets flagged, they simply rotate to the next in the sequence, a tactic known as sequential number grouping that keeps operations running without interruption.
Cisco Talos found that six of the ten largest campaigns detected during the study period relied entirely on VoIP infrastructure. Sinch was identified as the most commonly abused CPaaS provider, referring to communications-platform-as-a-service companies offering programmable APIs for voice and messaging. These platforms are built for automation and high call volumes, which makes them attractive and widely exploited tools for large-scale scam operations.
The reuse patterns are equally calculated. Of 1,962 unique phone numbers analyzed, 68 were reused across multiple consecutive days. Scammers often apply a cool-down period, pausing a number for several days before bringing it back into a new campaign. This timing is designed to outlast update cycles of third-party reputation services, which can take days to distribute fresh intelligence.
Recycling Lures to Stay Under the Radar
One of the most telling tactics Cisco Talos documented is the recycling of the same phone number across completely unrelated lures. A single number might appear in emails posing as an order confirmation, a subscription renewal, and a financial alert all within a short span. This deliberate variation in lure type helps attackers avoid patterns that automated filters would otherwise quickly detect.
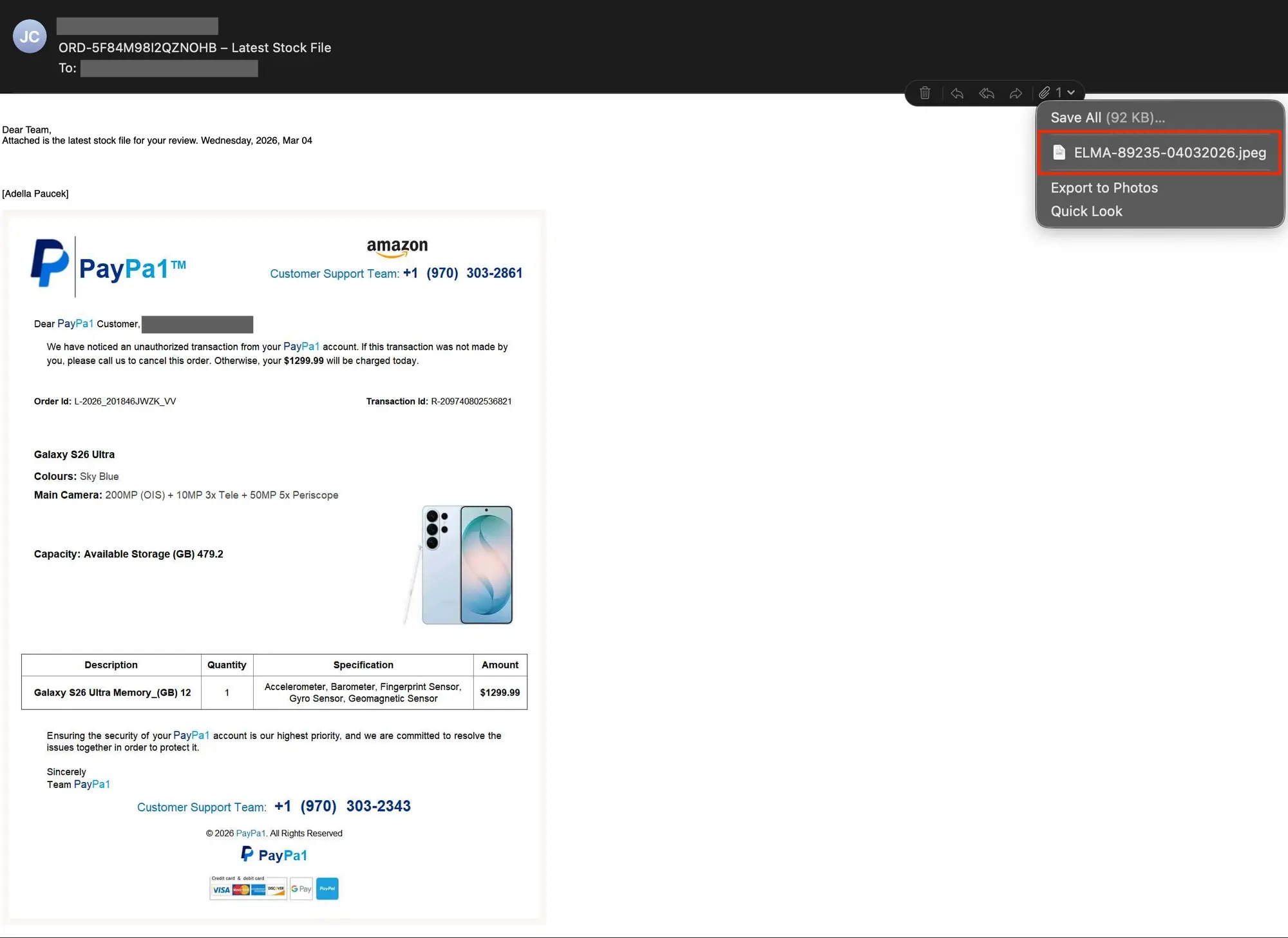
In one campaign, the same number was embedded in both HEIC and PDF attachment formats, showing how attackers avoid relying on a single delivery method. HEIC files, commonly associated with iPhone photos, were used to bypass traditional file-type detection while maintaining high image quality. Talos confirmed seeing campaigns with even broader attachment variety, underscoring just how adaptable these threat actors have become.
Security and telecom teams are advised to move beyond email sender filtering, which grows less effective as senders cycle rapidly through disposable domains. Talos recommends treating phone numbers as primary indicators of compromise and applying clustering techniques to connect seemingly unrelated campaigns that share the same phone infrastructure. Real-time reputation monitoring across communication channels and active collaboration between telecom providers are among the most effective steps toward stopping these organized scam networks.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.