Fake Call History Apps on Google Play Steal Payments
A recent wave of fraudulent Android applications accumulated millions of downloads on Google Play before their eventual removal. These apps, now tracked under the name CallPhantom, enticed users with...
A recent wave of fraudulent Android applications accumulated millions of downloads on Google Play before their eventual removal. These apps, now tracked under the name CallPhantom, enticed users with the promise of revealing any phone number’s call history. However, they delivered only fabricated data and caused users significant financial losses, as detailed in a recent report.
The scheme worked by exploiting a simple but powerful hook. People are naturally curious about who has called a specific number, and these apps claimed to deliver that information instantly.
Users were shown what looked like partial results and then prompted to pay to unlock the full call history. That history was entirely fabricated right from the start.
Researchers at WeLiveSecurity identified and reported 28 such fraudulent applications on the Google Play Store.
Their analysis found the apps had been cumulatively downloaded over 7.3 million times before Google removed them following ESET’s disclosure in December 2025.
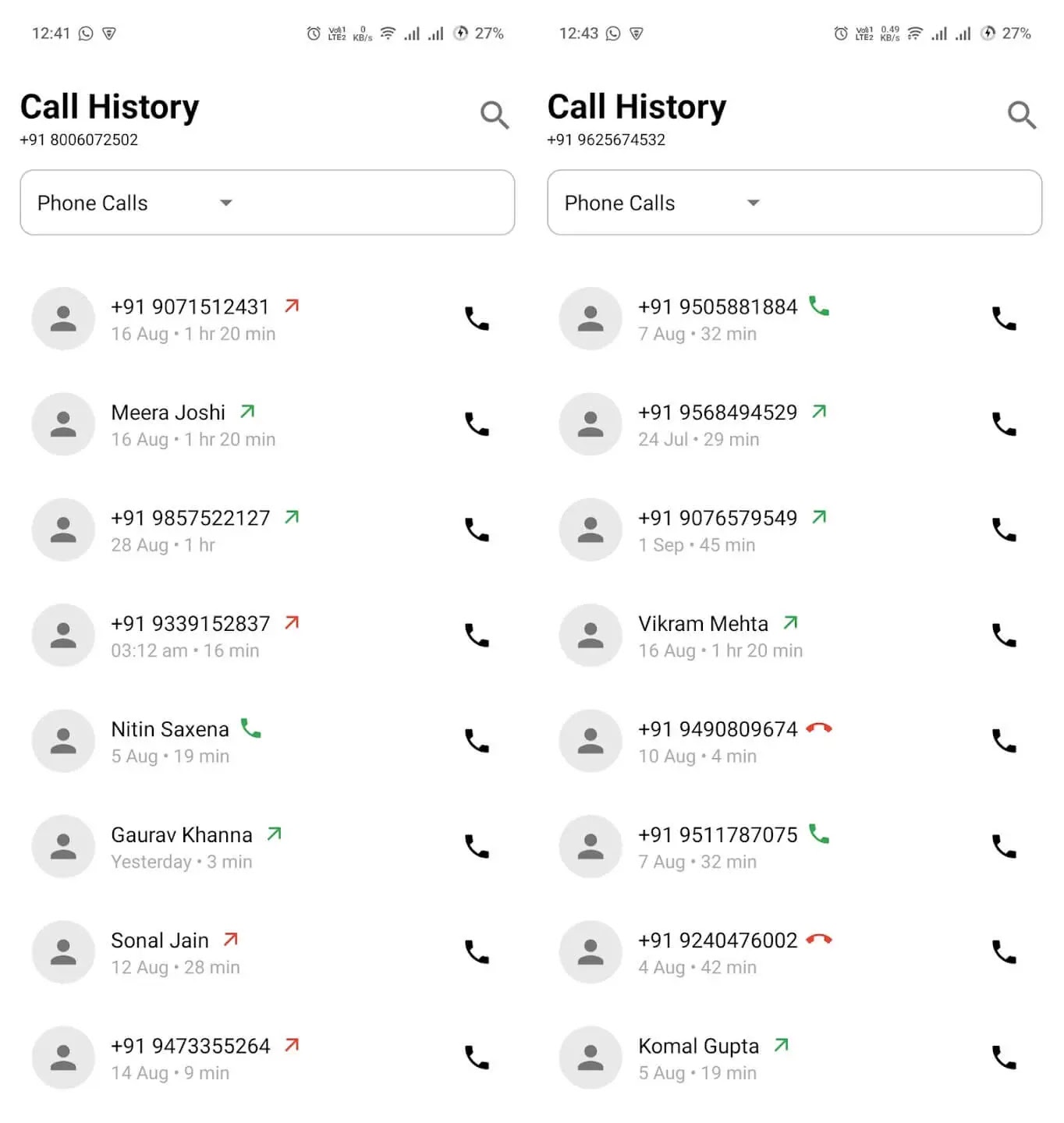
The apps primarily targeted Android users in India and the broader Asia-Pacific region. Many came with India’s country code pre-selected and supported UPI, a payment system widely used across India. A screenshot of the fabricated call history data was even included in the app’s Play Store listing, presented as proof the app actually worked.
Fake Call History Apps on Google Play
Despite looking different on the surface, all 28 apps shared the same core purpose: generate fake communication data and charge victims for access. Subscription packages ranged from weekly to yearly, with the highest price reaching up to $80.
The CallPhantom apps fell into two main clusters. The first group had hardcoded names, country codes, and call log templates embedded directly in their code. These were combined with randomly generated phone numbers and shown to users as partial results, pushing them to pay to see more.
The second cluster asked users to enter an email address, claiming the retrieved call history would be delivered there. No data was generated until after payment, and even then, nothing real was ever sent. The apps had no actual capability to access call logs, SMS records, or WhatsApp data from any device.
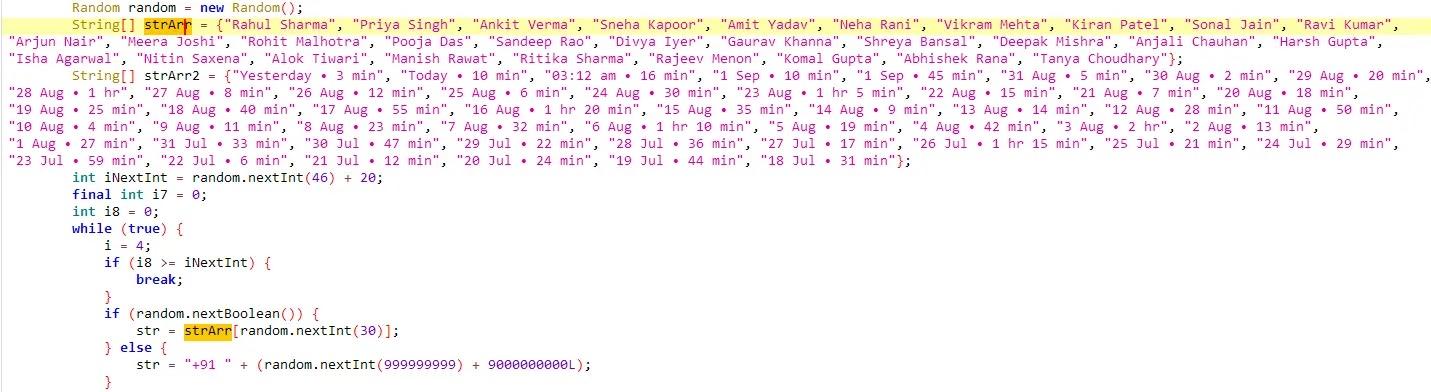
This shows how deeply the deception was built into the code, with fixed names and timestamps baked in before the app ever reached a user’s phone.
Three payment methods appeared across the apps. Some used Google Play’s official billing system. Others redirected users to third-party UPI apps, with payment details either hardcoded or fetched dynamically from a Firebase real-time database, letting operators swap receiving accounts at will.
A third method embedded payment card checkout forms directly inside the app, violating Google Play’s payments policy and making refunds significantly harder.
Bypassing Refunds and Staying Under the Radar
One of the most deliberate tactics used by CallPhantom was steering users toward payment channels Google could not reverse. When payments went through third-party UPI apps or direct card entry inside the app, Google had no ability to cancel transactions or issue refunds. Victims were left fully dependent on external payment providers or the scam developers themselves.
In at least one case, the app sent deceptive notifications styled as email alerts, falsely claiming call history results had arrived. Tapping the notification led straight to a subscription screen, keeping the pressure on even after users had exited without paying.
Anyone who subscribed through Google Play’s official billing system may be eligible for a refund, as existing subscriptions were canceled when the apps were removed. Requests must fall within Google’s allowed refund window. For purchases made outside Google Play, contacting the payment provider or card issuer directly to dispute the charge is the recommended step.
The most practical protection is verification before downloading. Checking developer credibility, reading user reviews carefully, and staying skeptical of apps claiming to access private data belonging to other people are all steps that help avoid traps like these.
Indicators of Compromise (IoCs):-
| Type | Indicator | Description |
|---|---|---|
| SHA-1 Hash | 799AA5127CA54239D3D4A14367DB3B712012CF14 | all.callhistory.detail.apk — Android/CallPhantom |
| SHA-1 Hash | 56A4FD71D1E4BBA2C5C240BE0D794DCFF709D9EB | calldetaila.ndcallhisto.rytogetan.ynumber.apk — Android/CallPhantom |
| SHA-1 Hash | EC5E470753E76614CD28ECF6A3591F08770B7215 | callhistoryeditor.callhistory.numberdetails.calleridlocator.apk — Android/CallPhantom |
| SHA-1 Hash | 77C8B7BEC79E7D9AE0D0C02DEC4E9AC510429AD8 | com.all_historydownload.anynumber.callhistorybackup.apk — Android/CallPhantom |
| SHA-1 Hash | 9484EFD4C19969F57AFB0C21E6E1A4249C209305 | com.any.numbers.calls.history.apk — Android/CallPhantom |
| SHA-1 Hash | CE97CA7FEECDCAFC6B8E9BD83A370DFA5C336C0A | com.anycallinformation.datadetailswho.callinfo.numberfinder.xapk — Android/CallPhantom |
| SHA-1 Hash | FC3BA2EDAC0BB9801F8535E36F0BCC49ADA5FA5A | com.app.call.detail.history.apk — Android/CallPhantom |
| SHA-1 Hash | B7B80FA34A41E3259E377C0D843643FF736803B8 | com.basehistory.historydownloading.xapk — Android/CallPhantom |
| SHA-1 Hash | F0A8EBD7C4179636BE752ECCFC6BD9E4CD5C7F2C | com.call.detail.caller.history.xapk — Android/CallPhantom |
| SHA-1 Hash | D021E7A0CF45EECC7EE8F57149138725DC77DC9A | com.call.of.any.number.apk — Android/CallPhantom |
| SHA-1 Hash | 04D2221967FFC4312AFDC9B06A0B923BF3579E93 | com.callapp.historyero.apk — Android/CallPhantom |
| SHA-1 Hash | CB31ED027FADBFA3BFFDBC8A84EE1A48A0B7C11D | com.calldetails.smshistory.callhistoryofanynumber.apk — Android/CallPhantom |
| SHA-1 Hash | C840A85B5FBAF1ED3E0F18A10A6520B337A94D4C | com.callhistory.anynumber.chapfvor.history.xapk — Android/CallPhantom |
| SHA-1 Hash | BB6260CA856C37885BF9E952CA3D7E95398DDABF | com.callhistory.calldetails.callerids…callhistorymanager.apk — Android/CallPhantom |
| SHA-1 Hash | 55D46813047E98879901FD2416A23ACF8D8828F5 | com.callhistory.callhistoryany.call.apk — Android/CallPhantom |
| SHA-1 Hash | E23D3905443CDBF4F1B9CA84A6FF250B6D89E093 | com.callhistory.callhistoryyourgf.apk — Android/CallPhantom |
| SHA-1 Hash | 89ECEC01CCB15FCDD2F64E07D0E876A9E79DD3CE | com.callinformative.instantcallhistory…callinfo.xapk — Android/CallPhantom |
| SHA-1 Hash | 8EC557302145B40FE0898105752FFF5E357D7AC9 | com.cddhaduk.callerid.block.contact.xapk — Android/CallPhantom |
| SHA-1 Hash | 6F72FF58A67EF7AAA79CE2342012326C7B46429D | com.easyranktools.callhistoryforanynumber.apk — Android/CallPhantom |
| SHA-1 Hash | 28D3F36BD43D48F02C5058EDD1509E4488112154 | com.getanynumberofcallhistory…findcalldetailsofanynumber.xapk — Android/CallPhantom |
| SHA-1 Hash | 47CEE9DED41B953A84FC9F6ED556EC3AF5BD9345 | com.chdev.callhistory.xapk — Android/CallPhantom |
| SHA-1 Hash | 9199A376B433F888AFE962C9BBD991622E8D39F9 | com.name.factor.apk — Android/CallPhantom |
| SHA-1 Hash | 053A6A723FA2BFDA8A1B113E8A98DD04C6EEF72A | com.pdf.maker.pdfreader.pdfscanner.apk — Android/CallPhantom |
| SHA-1 Hash | 4B537A7152179BBA19D63C9EF287F1AC366AB5CB | com.phone.call.history.tracker.apk — Android/CallPhantom |
| SHA-1 Hash | 87F6B2DB155192692BAD1F26F6AEBB04DBF23AAD | com.pixelxinnovation.manager.apk — Android/CallPhantom |
| SHA-1 Hash | 583D0E7113795C7D68686D37CE7A41535CF56960 | com.rajni.callhistory.apk — Android/CallPhantom |
| SHA-1 Hash | 45D04E06D8B329A01E680539D798DD3AE68904DA | com.sbpinfotech.findlocationofanynumber.xapk — Android/CallPhantom |
| SHA-1 Hash | 34393950A950F5651F3F7811B815B5A21F84A84B | sc.call.ofany.mobiledetail.apk — Android/CallPhantom |
| IP Address | 34.120.160[.]131 | Firebase-hosted C2 IP, Google LLC, first seen 2025 |
| IP Address | 34.120.206[.]254 | Firebase-hosted C2 IP, Google LLC, first seen 2025 |
| Domain | call-history-7cda4-default-rtdb.firebaseio[.]com | Firebase real-time database used for C2 communication |
| Domain | call-history-ecc1e-default-rtdb.firebaseio[.]com | Firebase real-time database used for C2 communication |
| Domain | ch-ap-4-default-rtdb.firebaseio[.]com | Firebase real-time database used for payment URL delivery |
| Domain | chh1-ac0a3-default-rtdb.firebaseio[.]com | Firebase real-time database used for payment URL delivery |
Note: IP addresses and domains are intentionally defanged (e.g., [.]) to prevent accidental resolution or hyperlinking. Re-fang only within controlled threat intelligence platforms such as MISP, VirusTotal, or your SIEM.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.