Malicious NuGet Packages Steal Credentials, SSH Target Browser
A new threat has emerged within the NuGet ecosystem, a widely used registry for .NET developers. Malicious actors have deployed five rogue packages, deceptively posing as legitimate Chinese software...
A new threat has emerged within the NuGet ecosystem, a widely used registry for .NET developers. Malicious actors have deployed five rogue packages, deceptively posing as legitimate Chinese software libraries. These packages secretly exfiltrate sensitive data, including browser credentials, SSH private keys, and cryptocurrency wallet information.
The attack takes a clever approach. Instead of creating obviously suspicious packages, the threat actor built each malicious library on top of real, functional code that developers in Chinese enterprise environments would recognize.
By mimicking trusted tools like AntdUI, a popular WinForms component library, the packages appear legitimate enough to pass casual inspection.
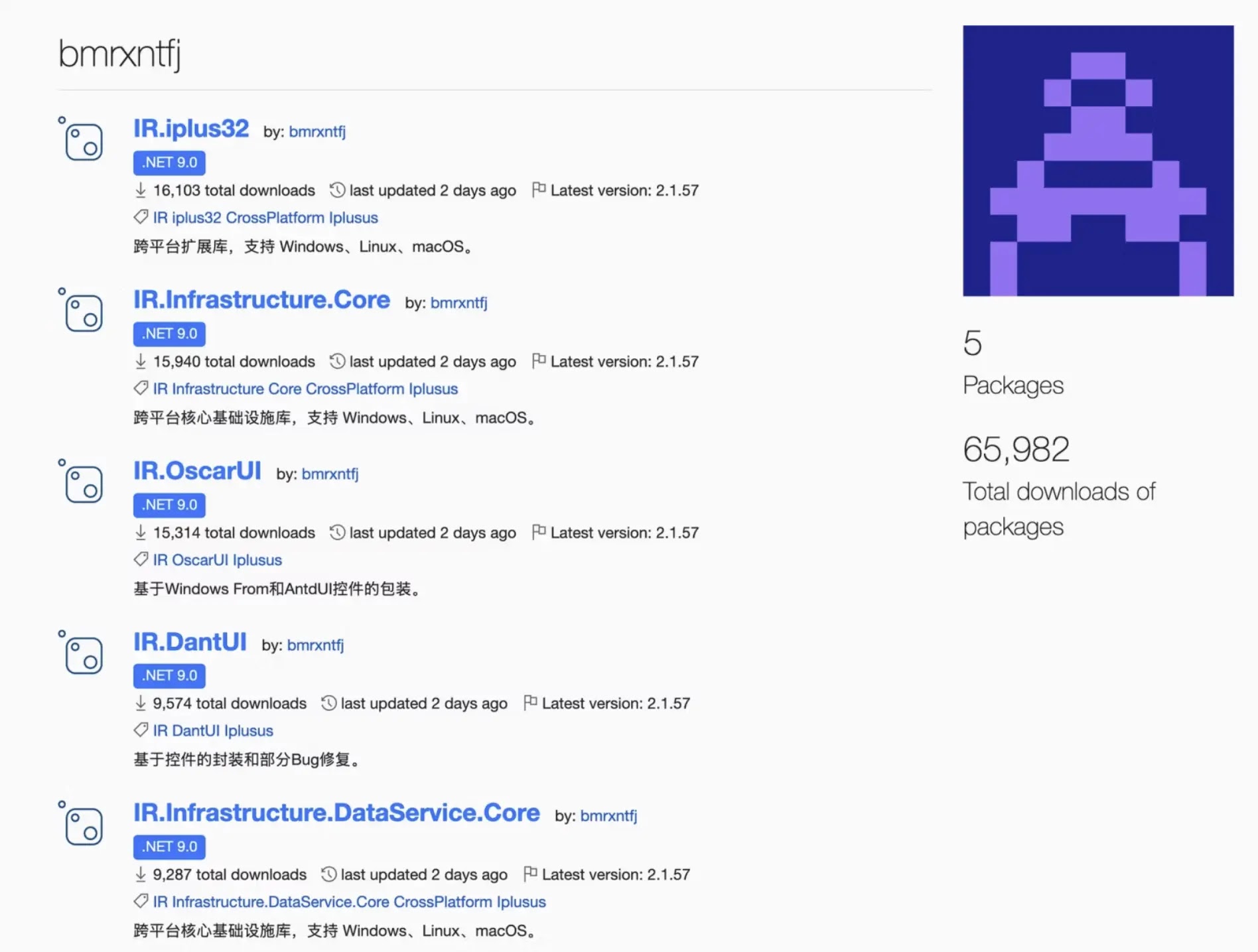
Researchers at Socket.dev identified all five packages, published under a single NuGet account named bmrxntfj. The packages accumulated approximately 64,784 downloads across all versions, placing tens of thousands of developer machines and CI/CD build systems at risk. The campaign traces back to at least September 2025, with all five packages still live at the time of writing.
What makes this campaign persistent is the version rotation technique the operator used. Out of 224 total versions published, 219 were deliberately hidden from public search. By keeping only one version visible while regularly swapping in fresh ones, the attacker invalidated hash-based detection and forced security teams to constantly update their blocklists.
Any developer workstation or build server that ran a package restore referencing these five IDs has potentially been exposed since late 2025. That long lifespan and high download count make this one of the more quietly damaging supply chain threats discovered this year.
Malicious NuGet Packages
The payload fires through a .NET module initializer, which the runtime calls automatically when a matching assembly loads. No user interaction is needed beyond a routine package restore. Once triggered, the malware uses JIT hooking to replace the compiler’s dispatch pointer, gaining control over every method compiled afterward.
A second-stage infostealer named we4ftg.exe then executes. It targets saved credentials across 12 Chromium-based browsers including Chrome, Edge, Brave, Firefox, and Opera, collecting passwords, autofill data, session cookies, and payment cards. It handles both legacy and AppBound Chrome encryption formats, confirming the payload has been recently maintained.
Cryptocurrency assets are a major focus. Browser extension wallets including MetaMask, TronLink, Phantom, Trust Wallet, and Coinbase Wallet are targeted, along with desktop applications like Exodus, Electrum, Atomic, Guarda, Ledger, and Binance. SSH private keys, Outlook profiles, Steam credentials, and files from Documents, Desktop, and Downloads are also collected.
All harvested data is staged under a folder path mimicking a legitimate Microsoft OneDrive directory. Legitimate OneDrive never creates a file by that specific name, making its presence a clear detection signal. Data is then sent to a command-and-control server registered 33 days before the NuGet publishing burst began.
C2 Infrastructure and Attribution
The primary C2 domain resolves to a server in Amsterdam operated through a virtual hosting provider. Its nameservers run through Njalla, a privacy registrar frequently used by threat actors to obstruct takedown requests. The domain was engineered to resemble a legitimate DNS provider so it would blend into routine firewall logs.
A secondary domain linked to an Alibaba Cloud server in Shanghai appears to host the attacker’s development environment. It produced no hits in public malware databases and was not observed receiving stolen data.
Attribution was confirmed through a unique RSA-1024 key embedded in every .NET Reactor-protected package. That same key appeared in four other malicious files on VirusTotal, including memory dumps predating the NuGet campaign by weeks. Labels on those files point to known malware families including Lumma, Quantum, AgentRacoon, and ArrowRAT.
Developers should immediately check project and lock files for any reference to IR.DantUI, IR.Infrastructure.Core, IR.Infrastructure.DataService.Core, IR.iplus32, or IR.OscarUI. Any machine that restored these packages should be treated as compromised, with all credentials, API keys, SSH keys, and wallet seeds rotated. Security teams should configure alerts for connections to the known C2 domain and watch for unexpected file creation at the OneDrive staging path.
Indicators of Compromise (IoCs):-
| Type | Indicator | Description |
|---|---|---|
| NuGet Package | IR.DantUI | Malicious package impersonating AntdUI |
| NuGet Package | IR.Infrastructure.Core | Malicious package impersonating Chinese enterprise library |
| NuGet Package | IR.Infrastructure.DataService.Core | Malicious package impersonating Chinese enterprise library |
| NuGet Package | IR.iplus32 | Malicious package impersonating iplus32 library |
| NuGet Package | IR.OscarUI | Malicious package impersonating Chinese UI library |
| NuGet Account | bmrxntfj | Threat actor publisher account |
| Domain | dns-providersa2[.]com | Primary C2 domain (registered 2026-03-12) |
| URL | https://dns-providersa2[.]com/check | C2 beacon and operator validation endpoint |
| URL | https://dns-providersa2[.]com/upload | Exfiltration upload endpoint |
| IP Address | 62[.]84[.]102[.]85 | VDSINA VPS, ASN 216071, Amsterdam |
| Domain | git[.]justdotrip[.]com | Operator development infrastructure (Alibaba Cloud Shanghai) |
| IP Address | 47[.]100[.]60[.]237 | Alibaba Cloud Shanghai, operator dev server |
| Nameserver | 1-you.njalla[.]no | Njalla nameserver for C2 domain |
| Nameserver | 2-can.njalla[.]in | Njalla nameserver for C2 domain |
| Nameserver | 3-get.njalla[.]fo | Njalla nameserver for C2 domain |
| File Path | C:ProgramDataMicrosoft OneDrivekeys.dat | Malware staging path for harvested data |
| File Name | we4ftg.exe | Second-stage infostealer binary |
| File Name | s4.exe | Rip-scraper memory dump (live stealer capture) |
| SHA-256 | e1869d6571894f058dd4ab2b66f060628dc364ee8e29afbd2323c95e5002fb8e | s4.exe hash |
| SHA-256 | 8f7aa15c77bde94087bb74dfc072e25212797b313731b4cad0ded3e152268dcf | we4ftg.exe hash |
| SHA-256 | 34e2d63b5db7e24c808711c2ca0c0a42afde97a0086d7d81609110c002d18d7c | IR.DantUI v2.1.55 encrypted stage-2 resource |
| SHA-256 | b8543b2a1ad8862ebfef18924cf5444d2adfee996939963f4fc2748c582cf9a9 | IR.Infrastructure.Core v2.1.55 encrypted stage-2 resource |
| SHA-256 | b8fa1b2fade45304c003909e375d2519ea447b498b7d93fe7c50db014d30f4fa | IR.Infrastructure.DataService.Core v2.1.55 encrypted stage-2 resource |
| SHA-256 | 019e6c2cf58386039133981f3377b085fbd70c98ae8613c7c6a4f10a9f2d9824 | IR.iplus32 v2.1.55 encrypted stage-2 resource |
| SHA-256 | 596c453c9dbb7240f1ce05cc025496524ce7c538c23a9b2171174bf32b5691a1 | IR.OscarUI v2.1.55 encrypted stage-2 resource |
| Chrome Extension ID | nkbihfbeogaeaoehlefnkodbefgpgknn | MetaMask wallet extension |
| Chrome Extension ID | ibnejdfjmmkpcnlpebklmnkoeoihofec | TronLink wallet extension |
| Chrome Extension ID | bfnaelmomeimhlpmgjnjophhpkkoljpa | Phantom wallet extension |
| Chrome Extension ID | egjidjbpglichdcondbcbdnbeeppgdph | Trust Wallet extension |
| Chrome Extension ID | hnfanknocfeofbddgcijnmhnfnkdnaad | Coinbase Wallet extension |
| Git Commit Hash | efb675de4b3af3dac3c9cae91075fd7cc2f4f98e | Shared commit hash across campaign packages |
| NuGet Tag | Iplusus | Shared package tag used across campaign |
Note: IP addresses and domains are intentionally defanged (e.g., [.]) to prevent accidental resolution or hyperlinking. Re-fang only within controlled threat intelligence platforms such as MISP, VirusTotal, or your SIEM.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.