Sicarii RaaS Attacks Exposed RDP & Fortinet Devices
December 2025 marked the emergence of Sicarii, a previously unknown ransomware-as-a-service (RaaS) operation. Appearing across underground platforms, the group identified itself as Israeli or...
December 2025 marked the emergence of Sicarii, a previously unknown ransomware-as-a-service (RaaS) operation. Appearing across underground platforms, the group identified itself as Israeli or Jewish-affiliated.
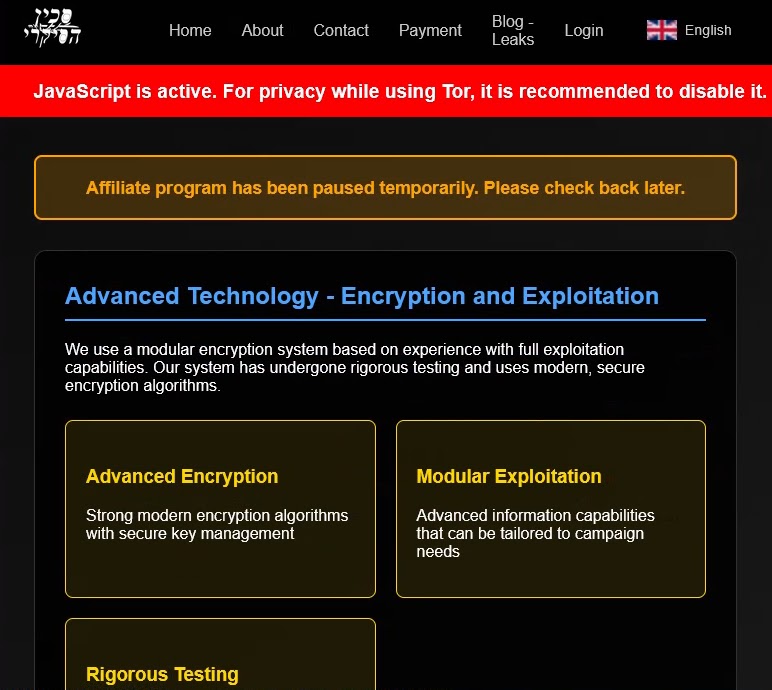
The operation stands apart from typical financially motivated ransomware due to its explicit use of Hebrew language, Israeli symbols, and references to historical Jewish groups in its branding.
Unlike established ransomware operations that maintain operational secrecy, Sicarii openly incorporates the Haganah symbol alongside Hebrew text in its visual identity, creating an unusual presence in the cybercriminal landscape.
The group claims to focus on targeting organizations in Arab and Muslim countries while explicitly avoiding Israeli systems.
The malware employs a geo-fencing mechanism that prevents execution on systems identified as Israeli, checking time zones, keyboard layouts, and network adapter IP addresses to identify local targets.

This selective targeting approach, combined with ideological messaging, distinguishes Sicarii from conventional ransomware groups operating from Eastern Europe or Russia.
Check Point analysts identified a sophisticated technical infrastructure underlying the Sicarii operation.
The ransomware begins execution through an anti-virtualization phase that detects sandbox environments and displays a deceptive error message to avoid analysis.

It then copies itself to the temporary directory as svchost_{random}.exe and tests internet connectivity by contacting google.com/generate_204 multiple times to ensure operational readiness.
Lateral Movement Through Network Reconnaissance
After establishing execution context, the malware performs aggressive network reconnaissance to map the victim’s environment.
The malware enumerates local network configurations through ARP requests and scans for exposed RDP services across discovered systems.
More significantly, it actively attempts to exploit Fortinet devices using CVE-2025-64446, a vulnerability that provides lateral movement pathways within compromised networks.
This reconnaissance phase supports both network penetration and data collection objectives, making it particularly dangerous for organizations with mixed security infrastructure.
The malware collects extensive data including system credentials, browser information, and application data from platforms like Discord, Slack, Telegram, and cryptocurrency wallets.
All harvested data gets packaged into a ZIP archive named collected_data.zip and exfiltrated through file.io. Following data exfiltration, the ransomware establishes persistence through multiple mechanisms including registry modifications, service creation, and new user accounts with hardcoded credentials.
The encryption phase uses AES-GCM with 256-bit keys, appending the .sicarii extension to encrypted files.
The operation concludes with a destructive component that deploys a batch script at startup, corrupting bootloader files and forcing immediate system shutdown.
Organizations should prioritize patching Fortinet devices and implementing network segmentation to contain this emerging threat.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.