Threat Actors Deploy Ransomware via Employee Monitoring & SimpleHelp
Threat actors are increasingly leveraging legitimate administrative software to initiate attacks, a tactic that significantly complicates the detection of their malicious activity. Instead of relying...
Threat actors are increasingly leveraging legitimate administrative software to initiate attacks, a tactic that significantly complicates the detection of their malicious activity.
Instead of relying solely on custom computer viruses, these actors abuse legitimate workforce monitoring tools to hide inside business networks.
By utilizing software designed for tracking employee productivity, they can control systems and steal sensitive data without triggering standard security alarms.
This strategy allows them to blend in with normal daily traffic, bypassing defenses that usually catch known malicious programs.
The primary tools used in these recent campaigns are “Net Monitor for Employees Professional” and “SimpleHelp.”
Although these applications are built for helpful IT support and staff oversight, hackers have repurposed them for harmful goals.
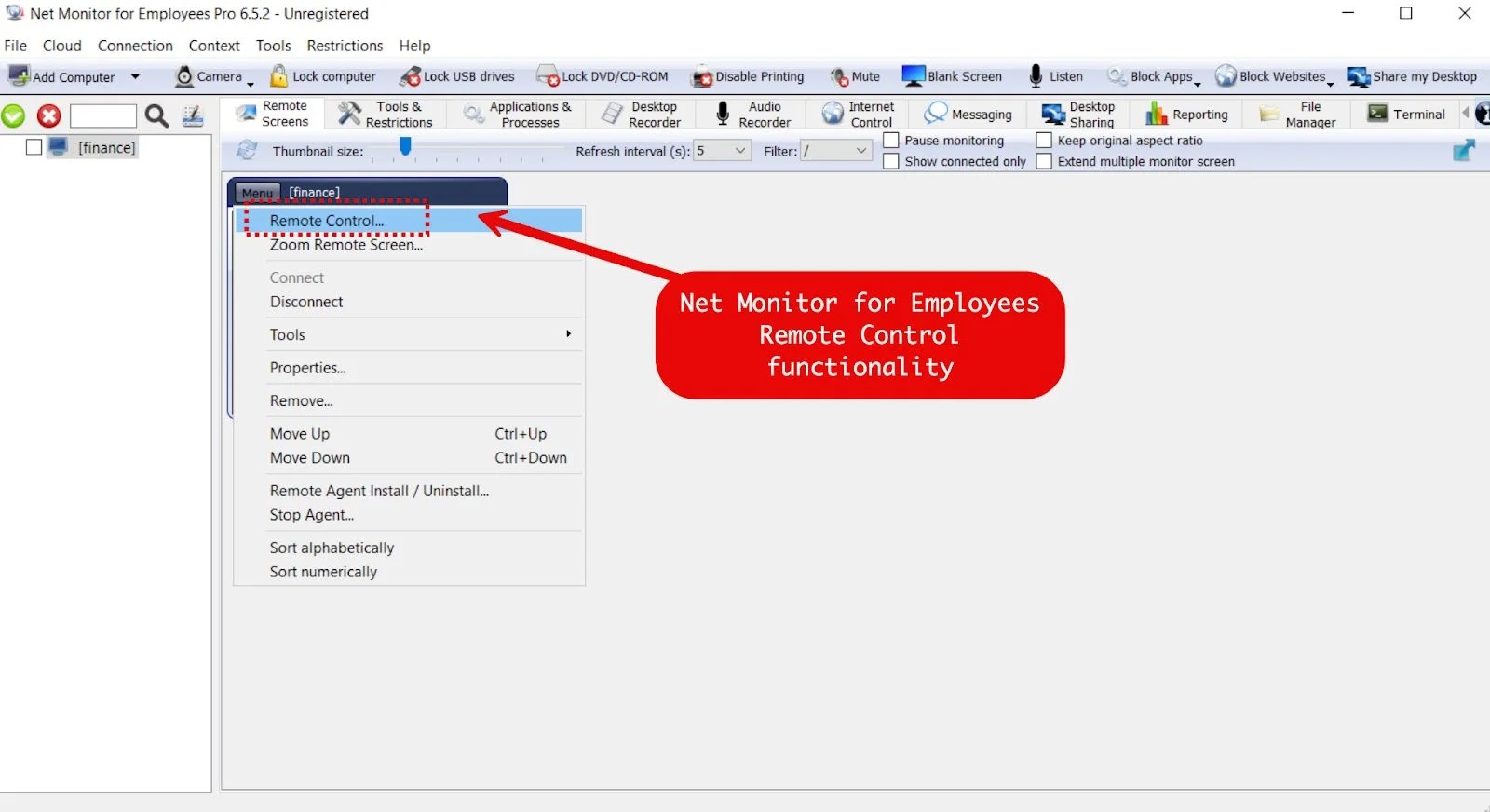
They use the software’s powerful features—such as viewing screens, managing files, and running commands—to take over computers. This effectively turns a standard office tool into a dangerous weapon for controlling a network remotely.
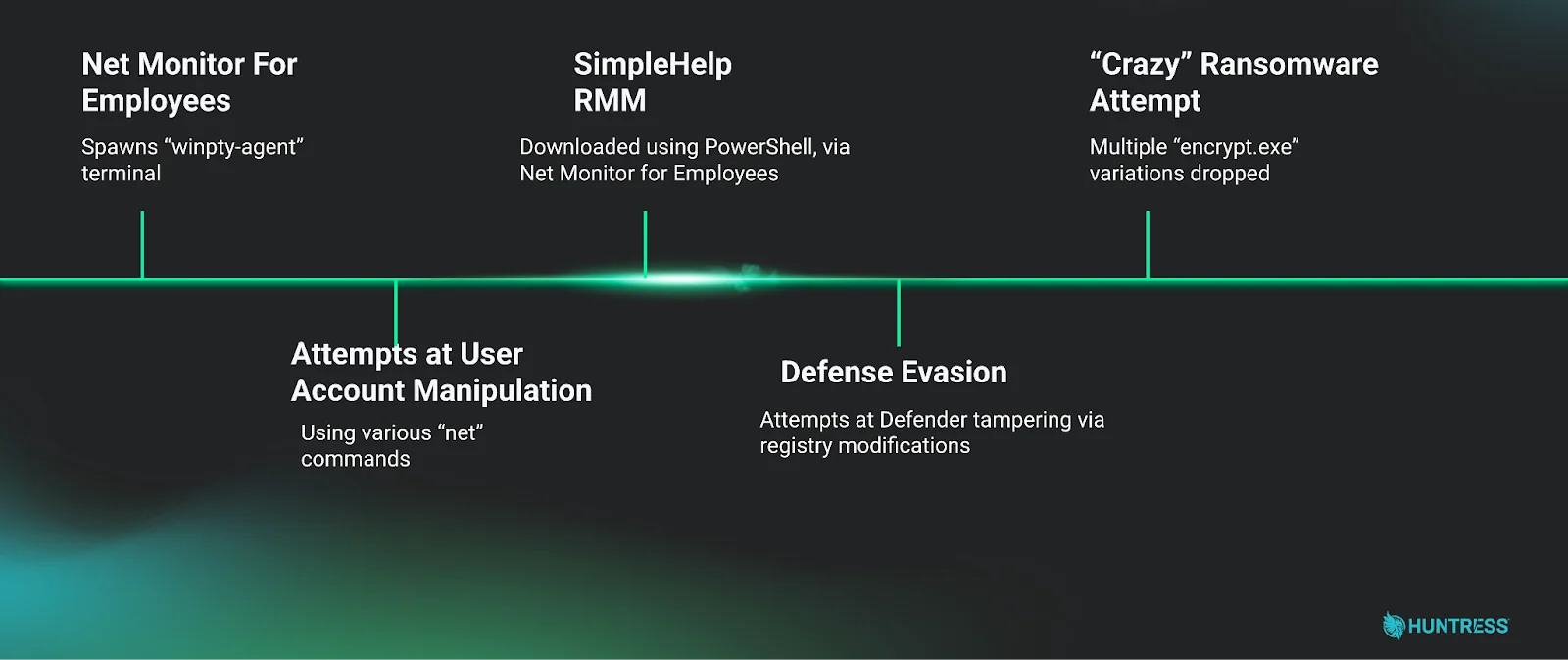
Huntress analysts identified this specific activity in early 2026, noting that the attackers used these tools to maintain long-term access.
The researchers observed that the intruders did not just watch users; they actively prepared the systems for a more damaging strike.
By establishing this hidden foothold, the threat actors could execute technical commands and disable safety measures without being noticed by the IT team.
This silent access often led to attempts to deploy “Crazy” ransomware, a file-locking virus, and to steal cryptocurrency.
Evasion Techniques and Persistence
The attackers worked hard to disguise their presence on the infected machines to avoid removal. They frequently renamed the malicious files to look like essential Microsoft services.
For instance, the monitoring agent was often registered with names like “OneDriveSvc” and “OneDriver.exe,” attempting to trick users into thinking it was a harmless cloud storage process.
This simple trick helped the malicious software stay active without raising suspicion.
To further ensure they could stay in the network, the attackers installed SimpleHelp as a backup entry point. This redundancy meant that if one tool was discovered and removed, the other would allow them to return.
They also configured the software to watch for specific words on the screen, such as “wallet” or “Binance.” This allowed them to receive instant alerts when a user opened a banking app, ensuring they could steal funds at the perfect moment.
To prevent these attacks, organizations must strictly limit which users can install software and should enforce Multi-Factor Authentication (MFA) on all remote accounts.
Security teams should also regularly audit systems for unauthorized remote management tools and monitor for attempts to disable antivirus programs.
Finally, checking for unusual program names that mimic legitimate services is essential for detecting these intrusions early.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.