Threat Actors Deploy 240+ Exploits Before Ransom Attacking Systems
Between December 25 and 28, a single threat actor executed an extensive scanning campaign. This operation involved probing over 240 distinct exploits against internet-facing systems, systematically...
Between December 25 and 28, a single threat actor executed an extensive scanning campaign. This operation involved probing over 240 distinct exploits against internet-facing systems, systematically gathering data on every vulnerable target discovered.
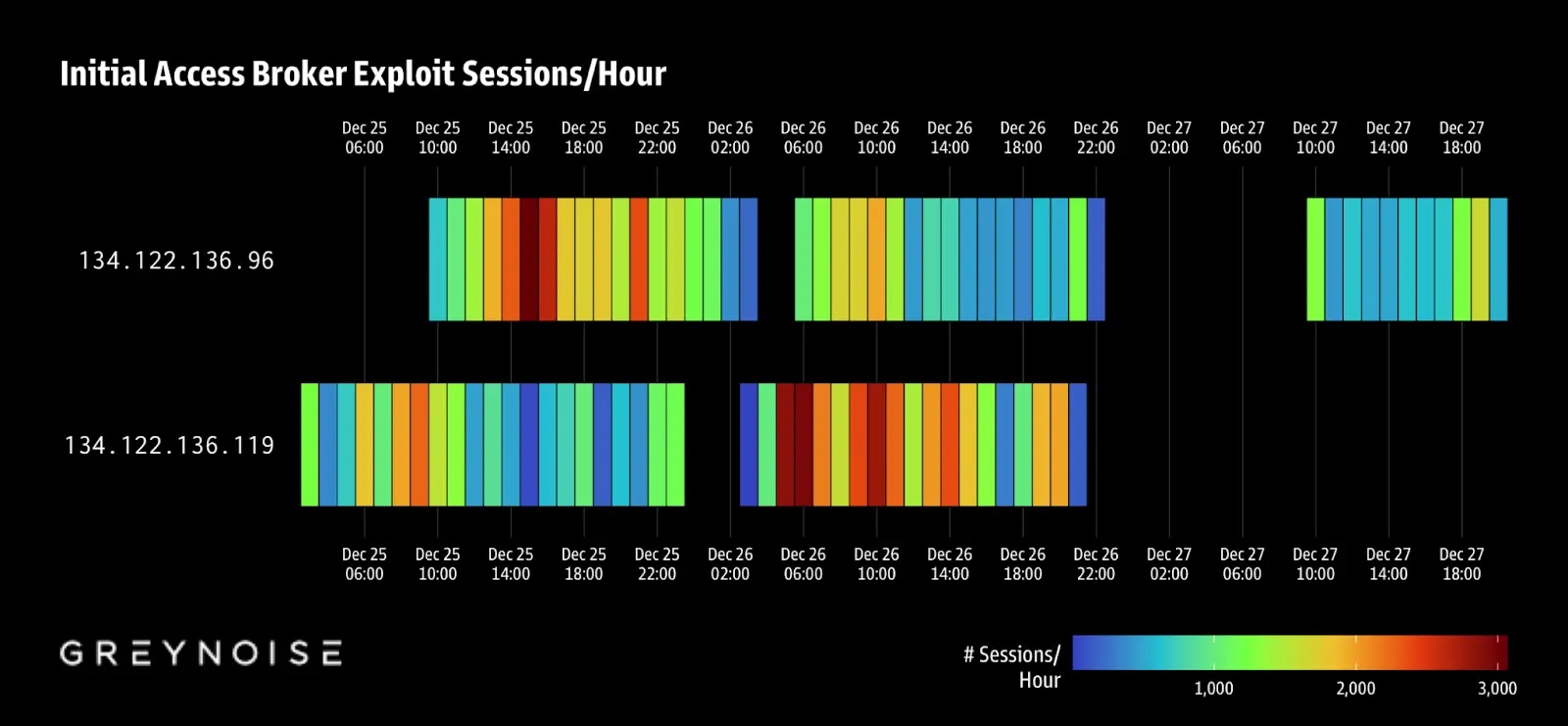
This reconnaissance operation, operating from two IP addresses linked to CTG Server Limited (AS152194), represents a new level of sophistication in how initial access is secured for ransomware operations.
The attacker systematically probed targets at intervals of one to five seconds, with each system receiving 11 different exploit types to identify weaknesses.
The campaign reveals a concerning shift in ransomware operations. Rather than launching direct attacks, these threat actors are acting as Initial Access Brokers (IABs), building catalogs of vulnerable systems to sell to ransomware groups.
The data collected during this four-day window provides a confirmed inventory of exploitable targets that will likely fuel targeted intrusions throughout 2026.
The timing was deliberate, taking advantage of holiday periods when security teams are reduced, and detection systems receive minimal attention.
Greynoise analysts identified the campaign by detecting over 57,000 unique Out-of-Band Application Security Testing (OAST) subdomains tied to ProjectDiscovery’s Interactsh platform.
The researchers noted that the tooling matched Nuclei, an open-source vulnerability scanner, run at industrial scale.
By analyzing JA4 network fingerprints and a shared Machine ID across 98 percent of attempts, Greynoise analysts confirmed this was a single operator conducting the attack, not a coordinated group effort.
Detection Evasion and Infrastructure Analysis
The attacker’s choice of CTG Server Limited raises significant concerns about resilient infrastructure for criminal operations.
This Hong Kong-registered hosting provider controls approximately 201,000 IPv4 addresses across 672 prefixes and operates with minimal abuse enforcement.
The network previously identified as hosting phishing domains within FUNNULL CDN infrastructure and announces bogon routes, indicating poor network hygiene practices that make it attractive for operations requiring infrastructure that can withstand blocking attempts.
Organizations need to examine their logs from the campaign dates for connections to the suspicious IP addresses 134.122.136.119 and 134.122.136.96, as well as DNS queries to OAST domains including oast.pro, oast.site, oast.me, oast.online, oast.fun, and oast.live.
If matches are discovered, organizations should assume attackers have confirmed vulnerabilities in their networks, and that this access information may already be available for purchase in criminal marketplaces.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.