Sophisticated Phishing Steals Fortinet VPN Credentials
A Sophisticated Phishing campaign targets remote workers and IT administrators, impersonating the official Fortinet VPN Credentials and distributing malware. Security researcher with Alias G0njxa has...
A Sophisticated Phishing campaign targets remote workers and IT administrators, impersonating the official Fortinet VPN Credentials and distributing malware.
Security researcher with Alias G0njxa has observed that modern search engines, which now feature AI-generated “quick answers” or summaries, are inadvertently boosting this campaign.
When users search for “How to download Fortinet VPN,” some AI summaries are scraping content from the attacker’s malicious GitHub repository (vpn-fortinet[.]github[.]io) and presenting it as a legitimate step-by-step guide.
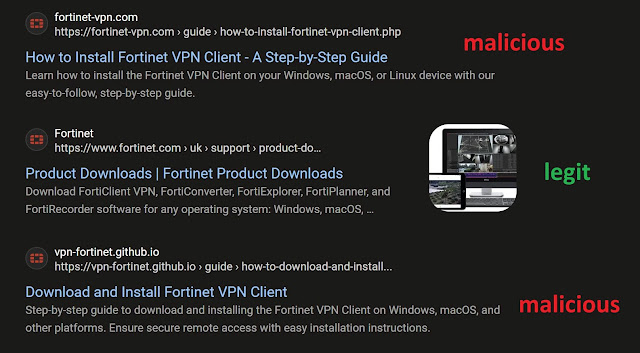
Because the initial link is hosted on GitHub, a reputable platform, AI models and users alike are more likely to trust the source. This “hallucinated” trust leads users to click the link, initiating the attack chain.
How the Attack Works
The attack follows a clever, segmented flow designed to filter out security bots and target only real human users coming from specific search engines.
- The Decoy Landing: The user clicks a link pointing to vpn-fortinet[.]github[.]io. This page hosts a script that checks the “referrer” (the website the user came from).
- Selective Redirects: If the user is visiting from a major search engine like Google, Bing, Yahoo, or DuckDuckGo, the script automatically redirects them to the actual phishing site: fortinet-vpn[.]com. If a security crawler or direct visitor accesses the page without these referrers, the redirect may not trigger, hiding the malicious intent.
- Credential Harvesting: The destination site perfectly mimics the legitimate Fortinet design. Before allowing a download, it creates a fake modal popup asking the user to enter their “Remote Gateway,” “Login,” and “Password” to “configure” the installer.
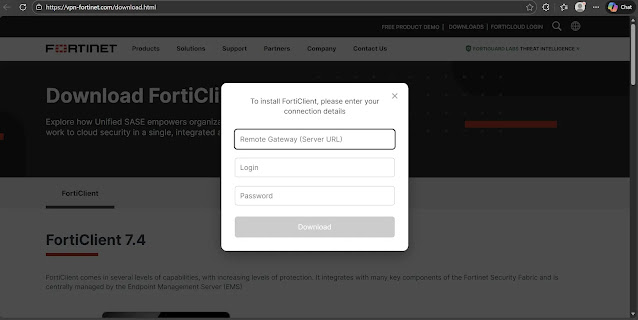
- The Bait: Once the victim submits their credentials, sending them directly to the attackers, the site initiates a download from myfiles2[.]download. To avoid suspicion, this payload often installs a legitimate version of FortiClient, leaving the victim unaware that their access credentials have been compromised.
Indicators of Compromise (IoCs)
IT administrators should immediately block the following domains and investigate any internal traffic that has communicated with them.
| IoC Type | Value | Description |
|---|---|---|
| Redirect Domain | vpn-fortinet[.]github[.]io | Initial landing page hosted on GitHub Pages to evade reputation filters. |
| Phishing URL | fortinet-vpn[.]com | The destination site where credential harvesting occurs. |
| Payload Host | myfiles2[.]download | Hosting domain for the decoy or malware payload. |
Organizations must remind employees that legitimate software downloads rarely require pre-authentication credentials just to get the installer. Authenticity should always be verified by checking the URL bar for the official fortinet.com domain.
Furthermore, this campaign highlights a critical new risk: Do not blindly trust AI search summaries. While convenient, these tools ingest data from the open web and can easily be manipulated by threat actors using basic SEO tactics. Always verify the source link before clicking.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.