Threat Actors Exploit Vercel AI Tools for Leverage Vercel’s
A new wave of phishing attacks is leveraging Vercel, an AI-powered web development platform, to streamline credential theft. Threat actors are exploiting Vercel’s capabilities to rapidly...
A new wave of phishing attacks is leveraging Vercel, an AI-powered web development platform, to streamline credential theft. Threat actors are exploiting Vercel’s capabilities to rapidly construct highly convincing fake login pages that closely mirror legitimate websites, as detailed in a recent report:
Vercel offers a GenAI tool called v0.dev that generates fully functional web pages from simple text prompts. An attacker can type something as basic as “create a Microsoft sign-in page with official logos and colors,” and the tool will produce a working replica within seconds.
This means someone with little technical background can now launch a phishing campaign that looks nearly identical to a real corporate login page.
Researchers at Cofense, a cybersecurity firm specializing in phishing defense, tracked a sharp rise in Vercel-based phishing campaigns since 2022. Analysts noted the platform has been used across attacks of varying skill levels and complexity. The data shows that Vercel abuse continued climbing well into 2025 and shows no signs of slowing down.
What makes this threat particularly dangerous is how effortlessly it replaces traditional phishing infrastructure. In the past, threat actors had to set up their own hosting servers, buy phishing kits from dark web marketplaces, and manage technical back-end systems. Vercel eliminates all of that by handling hosting, deployment, and page generation in one place.
The implications extend beyond individual users. Organizations of all sizes are at risk because attackers are spoofing brands that employees interact with daily, including Microsoft, Spotify, and popular job platforms.
Vercel Enables Mass Phishing
Vercel’s GenAI tool introduces a dangerous level of automation for phishing. With each prompt submitted, the AI produces a slightly different output, meaning threat actors can continuously generate new page versions without writing new prompts every time. If a site gets taken down, they simply generate a fresh one.
The platform also integrates with Telegram through its Bot API, which allows attackers to receive real-time alerts whenever a victim submits credentials. The Telegram bot monitors the Vercel-hosted page and sends stolen login details directly to the attacker’s account. This combination turns what used to require multiple tools and technical expertise into a near fully automated operation.
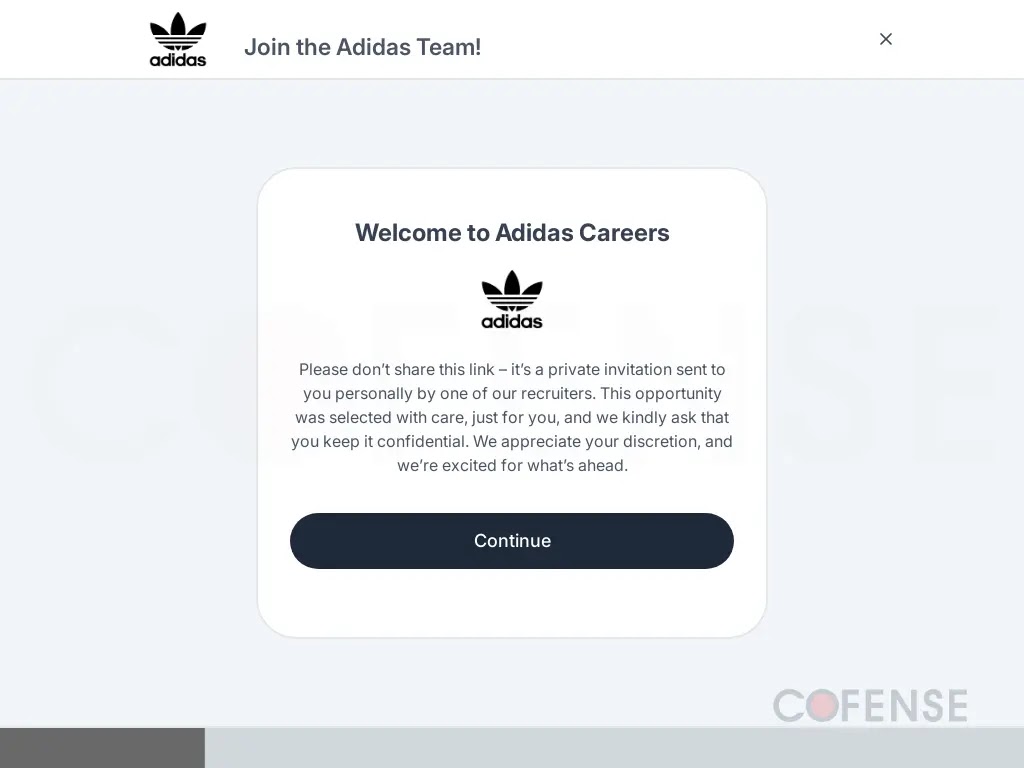
Cofense analysts documented specific campaigns where attackers posed as hiring managers for brands including Adidas, Nike, Ferrari, and Louis Vuitton. These phishing emails mimicked job offers and interview invitations, leading victims to fake career pages and then to fraudulent Facebook or Google login portals. All of these pages were built using Vercel’s GenAI product.
In one documented case, attackers created a Spotify login page so convincing it replicated the exact logos, color scheme, and layout of the real site.
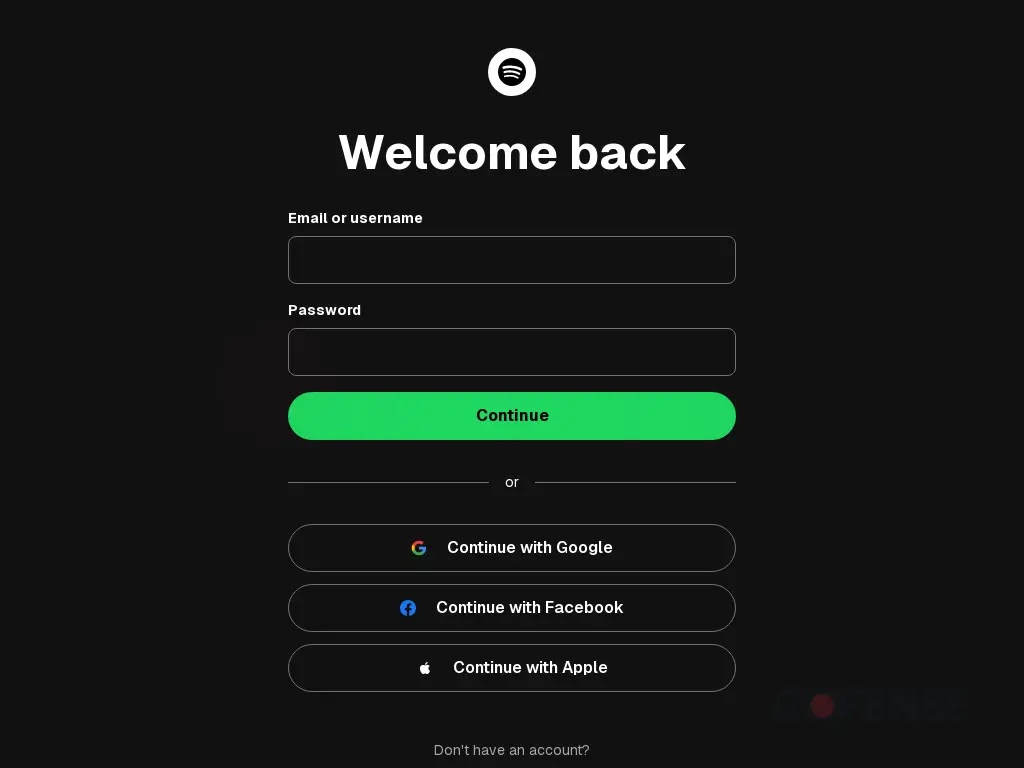
Once victims submitted their credentials, the page forwarded the stolen information to the attacker and redirected users to a second page requesting credit card details.
Protecting Against AI-Generated Phishing
Security awareness training must evolve alongside this threat. Because AI tools like v0.dev rarely produce the typos and formatting errors users have traditionally been taught to watch for, old advice about spotting “obvious mistakes” in phishing emails no longer holds up.
Users and organizations should now focus on verifying the actual URL in the browser bar before entering any login credentials. Even a pixel-perfect replica of a legitimate website cannot change the web address it operates from.
Checking for subtle variations in domain names remains one of the most reliable ways to catch a fake site.
Organizations can also report malicious Vercel-hosted sites directly to Vercel for takedowns. Security teams should monitor for vercel.app subdomains in inbound email links, as this is a common indicator of a hosted phishing page.
Staying current with updated threat intelligence and keeping staff trained on emerging attack patterns is now essential.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.