MuddyWater APT Delivers RustyWater via Word, Ev Weaponizing Documents
The Iran-linked MuddyWater Advanced Persistent Threat group has launched a sophisticated spear-phishing campaign targeting diplomatic, maritime, financial, and telecom sectors across the Middle East....
The Iran-linked MuddyWater Advanced Persistent Threat group has launched a sophisticated spear-phishing campaign targeting diplomatic, maritime, financial, and telecom sectors across the Middle East.
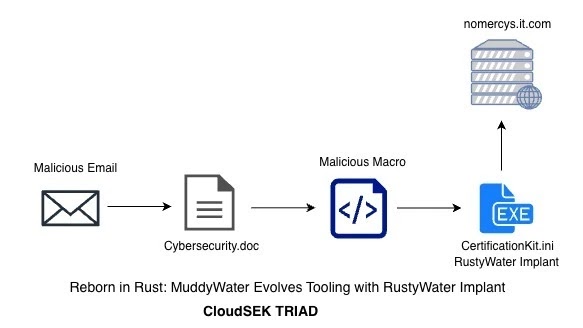
The threat actors are using weaponized Word documents to deliver a new Rust-based malware called RustyWater, which represents a major change from their traditional PowerShell and VBS tooling.
This upgraded implant can bypass antivirus and endpoint detection and response tools through multiple evasion techniques.
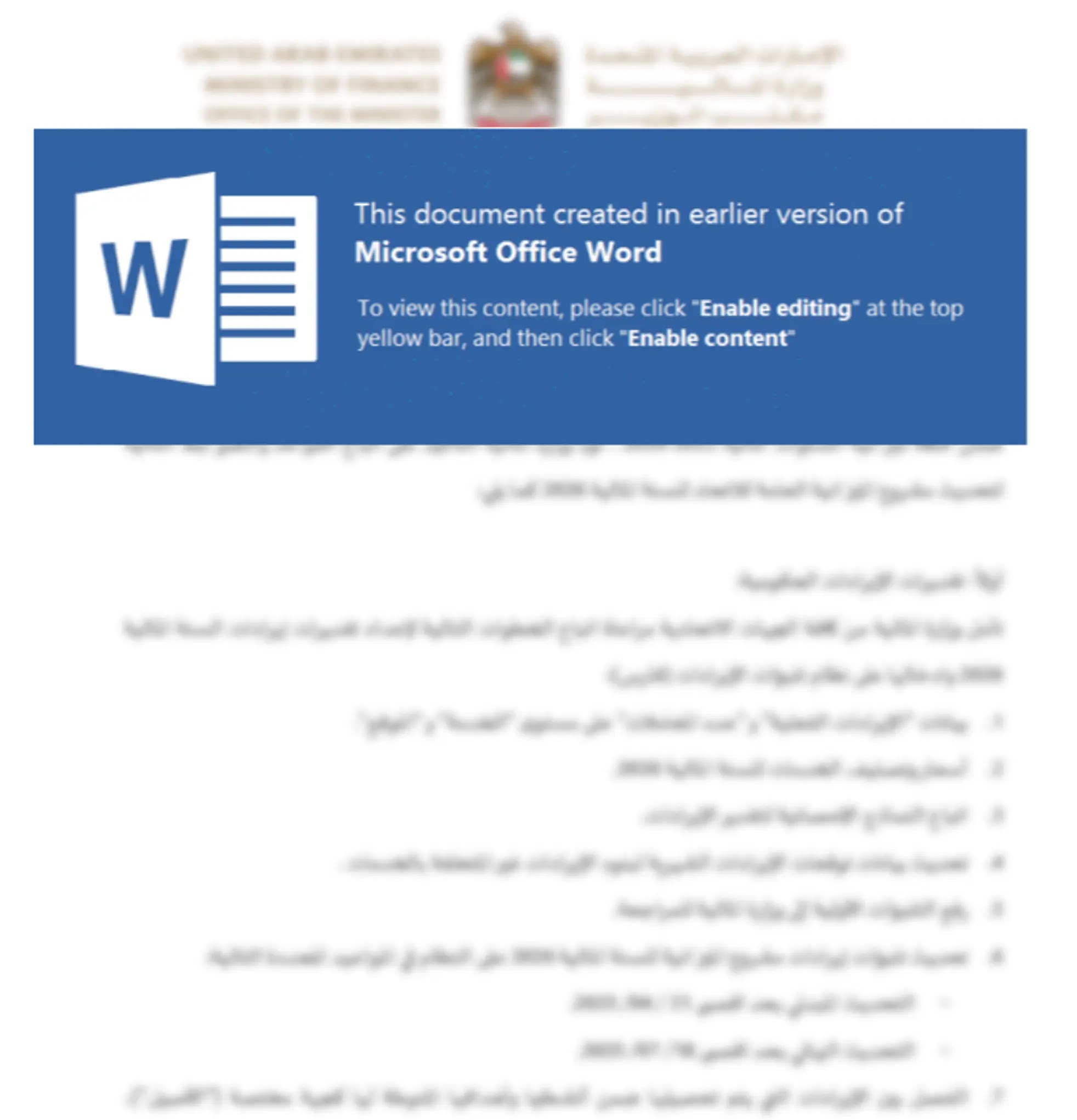
The attack begins with emails pretending to be official communications from legitimate organizations.
These emails contain malicious Word documents disguised as cybersecurity guidelines or policy documents. When victims enable macros, the hidden VBA code activates and starts the infection process.
CloudSEK researchers identified this campaign after detecting unusual patterns in threat activity across Middle Eastern organizations.
The malicious document contains two VBA macro functions that work together to deploy the payload. The WriteHexToFile function extracts hex-encoded data hidden inside a UserForm control, converts it to binary format, and saves it as CertificationKit.ini in the ProgramData folder.
The second function, called love_me_, uses ASCII value obfuscation to build command strings dynamically.
It reconstructs WScript.Shell through character codes and executes the dropped payload using cmd.exe. This approach helps the malware avoid static signature detection by security tools.
Multi-Layer Evasion and Persistence Mechanisms
RustyWater establishes persistence by adding itself to the Windows Registry startup key. The malware first checks the current user’s Run registry location and creates an entry pointing to CertificationKit.ini so it automatically runs when the system starts.
The implant uses position-independent XOR encryption to hide all its strings, making analysis more difficult.
Before executing its main functions, RustyWater scans the system for more than 25 antivirus and EDR products by checking service names, agent files, and installation paths. When it detects security tools, it changes its behavior to stay hidden.
The malware collects victim information including username, computer name, and domain details.
It packages this data in JSON format, then applies base64 encoding and XOR encryption in three layers before sending it to command and control servers.
RustyWater uses the Rust reqwest library for HTTP communication with built-in timeouts, connection pooling, and retry logic. The implant creates random sleep intervals between communications to make network traffic patterns harder to analyze.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.