Open WebUI File Upload Vulnerability Allows 1 Leads Attack
Exploiting a critical, unpatched flaw in Open WebUI, attackers need only a single click to seize control of AI workspaces. This vulnerability allows for remote code execution, account hijacking, and...
Exploiting a critical, unpatched flaw in Open WebUI, attackers need only a single click to seize control of AI workspaces. This vulnerability allows for remote code execution, account hijacking, and the theft of sensitive chat histories.
Discovered by security researcher Metin Yunus Kandemir, the vulnerability stems from a Stored Cross-Site Scripting (XSS) flaw in the platform’s profile image upload feature.
Because the developers refused to acknowledge the finding, the exploit code is now public, leaving users exposed.
The flaw exists in how Open WebUI processes user profile pictures. When a user uploads an image, the application relies on the /backend/open_webui/routers/users.py file to handle the data.
Unfortunately, the code fails to restrict the types of media users can upload.
Instead of uploading a standard JPEG or PNG, an attacker can upload a malicious SVG file containing a Base64-encoded JavaScript payload.
Because the application uses an “inline” content disposition, it does not force the browser to download the file.
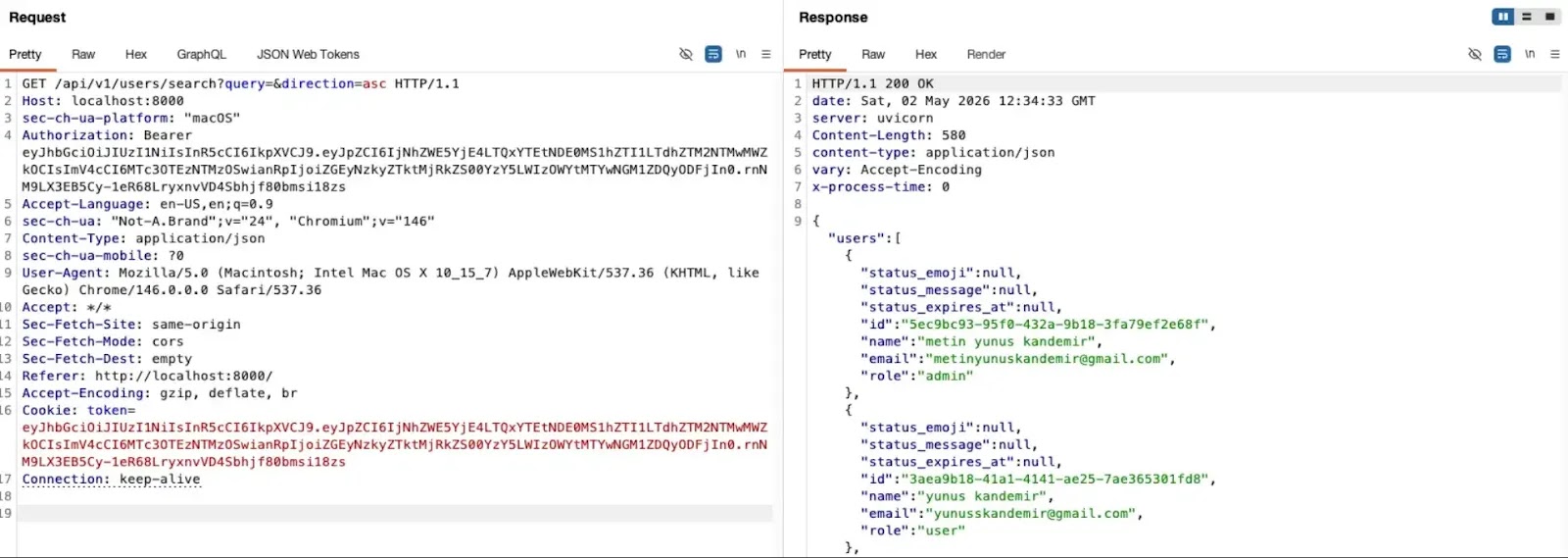
Instead, when a victim visits the image link, their browser immediately executes the hidden JavaScript.
Open WebUI File Upload RCE
The severity of the attack depends entirely on the victim’s permission level within the Open WebUI environment:
- Administrators: If an admin or a user with workspace privileges clicks the malicious image link, the attacker achieves 1-Click Remote Code Execution (RCE). The JavaScript quietly creates a malicious tool via the application’s API, opening a permanent backdoor.
- Standard Users: If a regular user clicks the link, the script triggers an Account Takeover (ATO). It silently scrapes the user’s browser storage to steal their authentication tokens and entirely copies their chat history, sending the private data to an external server.
If the victim is already logged in, no further authentication is required. The attack happens instantly in the background.
This zero-day vulnerability remains unpatched in Open WebUI version 0.7.2. Kandemir originally reported the issue to the vendor on March 10, 2026.
However, on May 6, 2026, the Open WebUI team closed the report as a duplicate.
They referenced an undisclosed security advisory and informed researcher UseHacker that his vulnerability report would not receive official recognition.
According to UseHacker, Kandemir published the full Proof of Concept (PoC) on May 8, 2026, believing the response violated responsible disclosure policies.
Because no official patch has been released, organizations using Open WebUI must implement manual defenses to protect their environments.
- Restrict File Types: Administrators should modify the backend code to enforce a strict allowlist for the
media_typevariable.Only safe formats like
image/png, image/jpeg, image/gif, and image/webpshould be accepted. Ensureimage/svg+xmlis entirely blocked. - Avoid Suspicious Links: Until a patch is deployed, users must exercise extreme caution.
Do not click on unexpected links that redirect to the Open WebUI application, especially URLs containing
/profile/image or /auth?redirect=.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.