Kimwolf Botnet Hacked 2 Million Devices and Turned User’s
Kimwolf, a recently discovered malware, has already compromised over 2 million devices worldwide. It covertly forces these systems to operate as illegal proxy servers, unbeknownst to their owners....
Kimwolf, a recently discovered malware, has already compromised over 2 million devices worldwide. It covertly forces these systems to operate as illegal proxy servers, unbeknownst to their owners.
The botnet has grown at an alarming speed and is currently being used to carry out online fraud, launch powerful cyberattacks, and steal information from millions of users.
Security researchers discovered this alarming trend in late 2025, revealing a sophisticated attack method that exploits a gap in how popular proxy networks protect their systems.
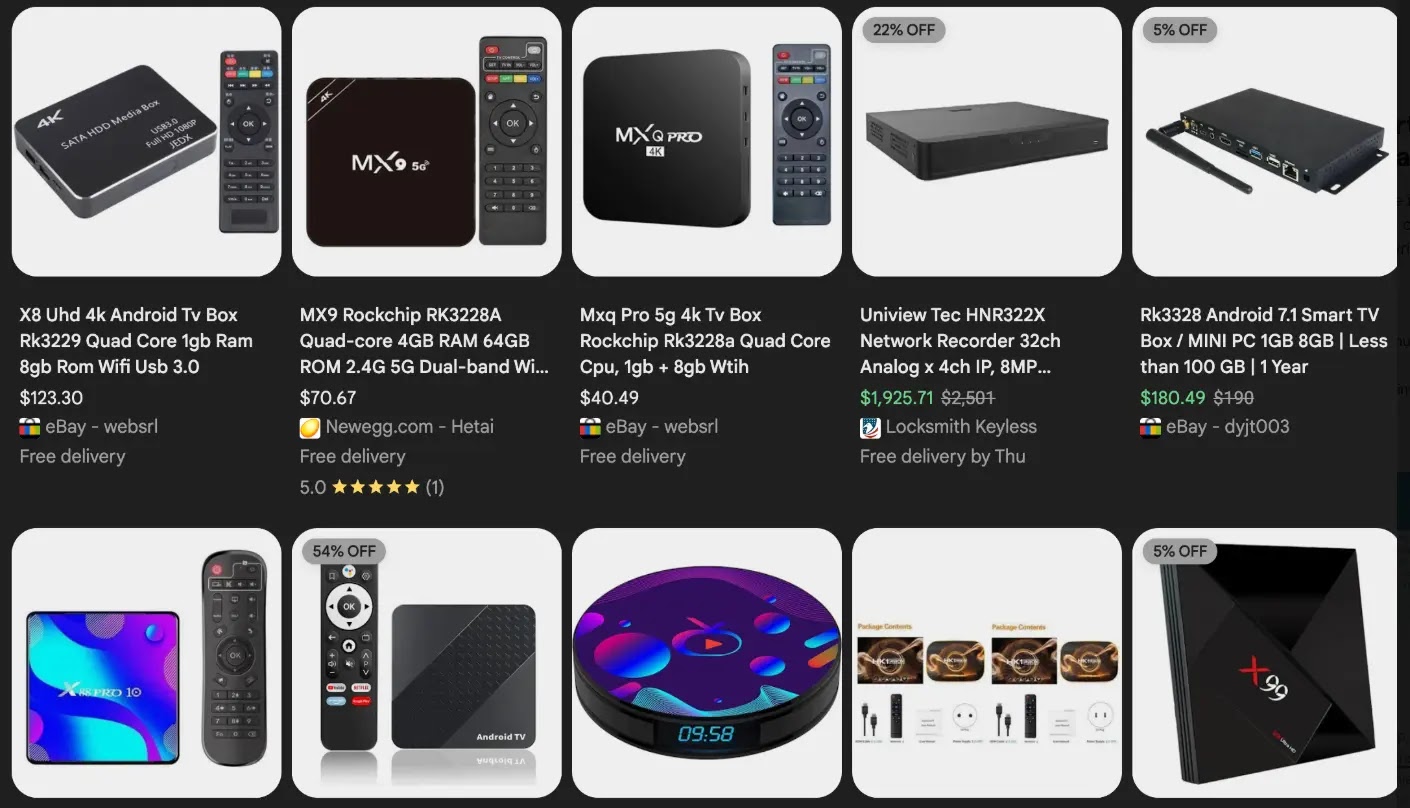
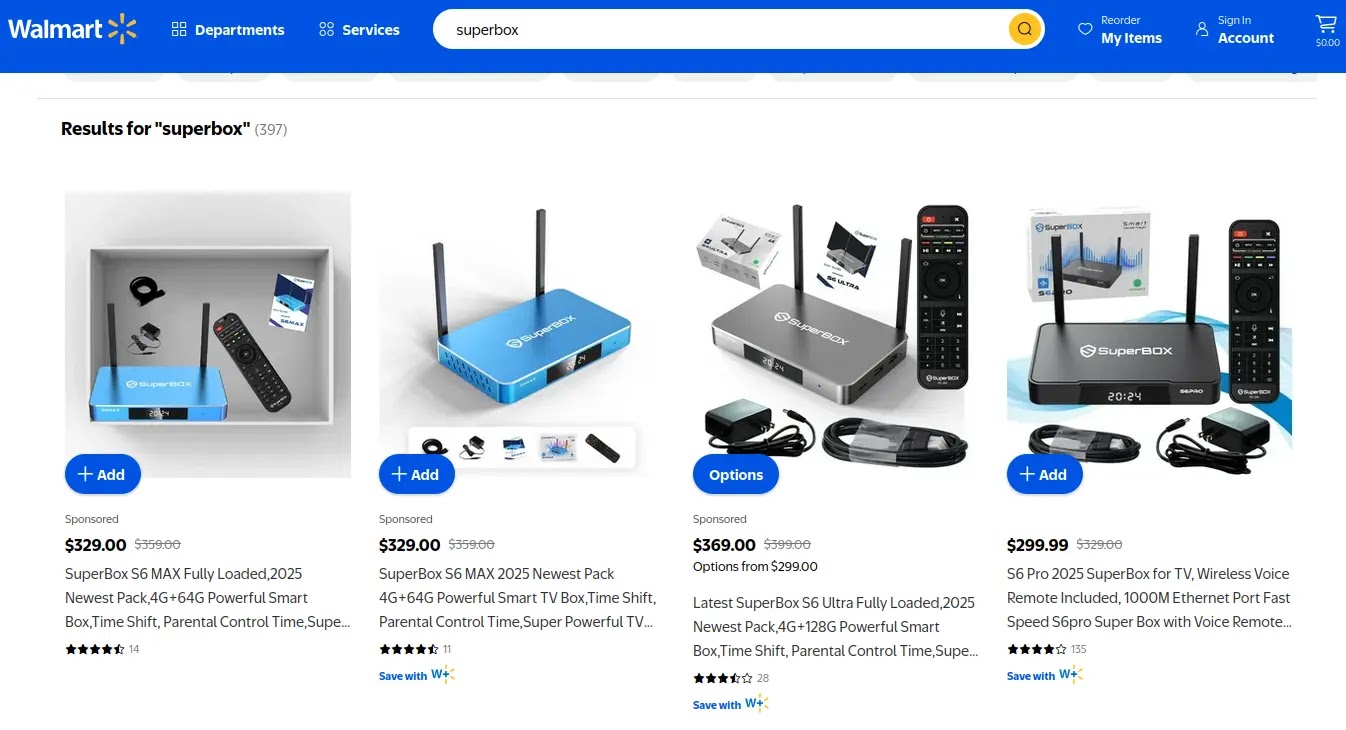
The infection targets cheap Android TV boxes and digital photo frames sold online, many of which arrive from factories with dangerous security settings already turned on.
Benjamin Brundage, a 22-year-old cybersecurity researcher and founder of Synthient, began investigating Kimwolf in October 2025 while studying for final exams at Rochester Institute of Technology.
His research uncovered a troubling pattern: the malware was spreading through a weakness in how the world’s largest residential proxy services work.
Brundage discovered that attackers could bypass safety rules by changing DNS settings to access private home networks through infected proxy devices.
He found that the biggest proxy network, called IPIDEA, had left a serious security hole open that allowed criminals to tunnel into people’s home networks and plant malware on connected devices without any authentication barriers.
KrebsOnSecurity analyst and researcher Brian Krebs noted Brundage’s critical findings after the researcher alerted multiple proxy providers to the vulnerability.
Attack flow
Krebs’ coverage highlighted how the research uncovered the two-pronged security nightmare: first, many unofficial TV boxes come with malware preinstalled from the factory, and second, these devices have a powerful feature called Android Debug Bridge that remains turned on, allowing anyone on the same network to take complete control of them with a simple command.
The attack spreads through a combination of weak security in inexpensive streaming devices and vulnerable proxy networks.
Attackers identify infected proxy endpoints by scanning for devices with Android Debug Bridge mode enabled, then use a straightforward technique: they issue a command that reads “adb connect [device-ip]:5555” to gain superuser access.
Once inside, they drop the malware payload by directing systems to visit a specific web address and use a pass phrase “krebsfiveheadindustries” to unlock the malicious download.
Synthient data shows that two-thirds of infected devices are Android TV boxes, with remaining infections spread across digital photo frames and mobile phones running hidden proxy applications.
The malware forces these devices to relay spam messages, commit advertising fraud, attempt account takeovers, and participate in distributed denial-of-service attacks that can bring major websites offline for extended periods.
The discovery of Kimwolf’s persistence methods reveals how the botnet rebuilds itself after disruptions.
Brundage observed the network recovering from a takedown effort by bouncing back from nearly zero infected systems to 2 million compromised devices within just a few days by tunneling through IPIDEA’s supply of fresh proxy endpoints.
This rapid recovery ability comes from IPIDEA’s enormous pool of over 100 million available residential proxy addresses. The malware operators monetize their botnet through multiple channels: selling app installation services, renting out proxy bandwidth, and offering DDoS attack capabilities to other criminals.
Security researchers expect this attack pattern to spread as more criminal groups discover these weaknesses, turning residential proxy networks into prime targets for large-scale device compromise and network breach attempts.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.