Speagle Malware Hijacks Cobra DocGuard to Steal Sensitive Data
A newly identified infostealer malware, dubbed Speagle, poses a significant threat to organizations utilizing Cobra DocGuard. This document security and encryption platform, developed by Chinese...
A newly identified infostealer malware, dubbed Speagle, poses a significant threat to organizations utilizing Cobra DocGuard. This document security and encryption platform, developed by Chinese company EsafeNet, is now targeted by the new threat, as detailed in
Cobra DocGuard has a troubled security history. In September 2022, attackers used it in a supply chain attack targeting a gambling company in Hong Kong.
Then in August 2023, a threat actor known as Carderbee exploited the same platform to deliver the Korplug backdoor — also known as PlugX — against organizations across Hong Kong and parts of Asia.
This repeated pattern has made Cobra DocGuard a consistent target for attackers seeking to exploit trusted, widely deployed software as an entry point into victim environments.
Symantec analysts identified Speagle as a 32-bit .NET executable that only operates fully on machines where Cobra DocGuard is installed.
The threat actor behind it has been assigned the name Runningcrab, though no confirmed link to any previously known threat group exists.
Researchers believe the most plausible scenarios point to either a state-sponsored actor or a skilled private contractor — a conclusion drawn from the malware’s deliberate targeting of Cobra DocGuard users and its focus on defense-related documents.
The infection vector remains unconfirmed, but early indicators suggest a possible supply chain attack.
The malware uses a legitimate Cobra DocGuard driver — the FileLock driver — to remove itself after completing its operations, behavior consistent with Trojanized software updates.
This self-delete technique leverages the SetFileInformationByHandle() API to rename and dispose of the running executable, a method originally discovered by security researcher Jonas Lykkegaard.
Using the platform’s own driver for self-deletion strongly suggests an attacker familiar with its internal components.
Runningcrab also hijacked a legitimate Cobra DocGuard server belonging to the targeted organization and used it as command-and-control infrastructure.
By routing stolen data through a server the victim already communicates with daily, the attacker made exfiltration traffic appear completely normal. This level of planning reveals a well-resourced actor with prior knowledge of the victim’s environment.
How Speagle Collects and Exfiltrates Stolen Data
Once Speagle confirms that Cobra DocGuard is installed by checking specific Windows registry keys under the Esafenet CDG System path, it begins a structured, multi-phase data collection process.
In the first phase, it gathers the machine’s username, hostname, and unique Cobra DocGuard client identifiers stored in local configuration files. If no valid client ID is found, the malware immediately triggers its self-delete routine and exits without stealing any data.
In the second phase, Speagle runs Windows Management Instrumentation queries, pulling details about running processes, network connections, installed services, scheduled tasks, and firewall rules.
It also maps files and folders across connected drives to build a picture of the compromised machine’s contents.
The third phase targets browser data — including browsing history, autofill entries, downloaded files, bookmarks, and search shortcuts — from directories used by Chromium-based browsers.
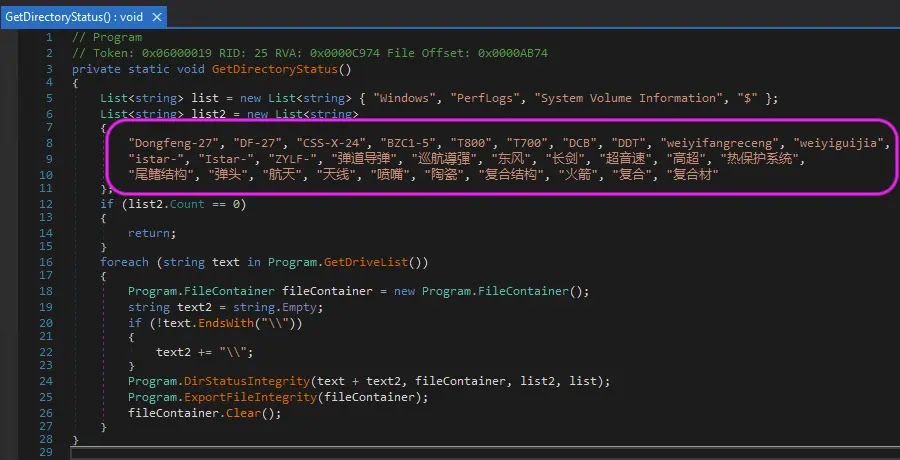
One variant carries additional capability, specifically searching for documents using Chinese-language keywords tied to defense technology.
These terms translate to “ballistic missile,” “hypersonic,” “warhead,” “Dongfeng,” and “Changjian,” referencing specific Chinese missile systems including the Dongfeng-27.
After each collection phase, Speagle compresses data using the Deflate algorithm, encrypts it with AES-128 in CBC mode, and transmits it via HTTP POST requests to a hardcoded compromised Cobra DocGuard server.
Organizations running Cobra DocGuard should immediately audit outbound network traffic for unexpected connections to IP addresses 60.30.147[.]18 and 222.222.254[.]165.
Endpoint detection tools should be updated to flag Speagle’s four known SHA-256 file hashes. Administrators should verify the integrity of their Cobra DocGuard server installations, review software update channels for unauthorized modifications, and apply the latest endpoint protection signatures promptly.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.