SmarterMail RCE Vulnerability: PoC Released SmarterTools Enables
A critical pre-authentication remote code execution (RCE) vulnerability has been discovered in SmarterTools’ SmarterMail solution. This flaw is identified as CVE-2025-52691. The flaw received a...
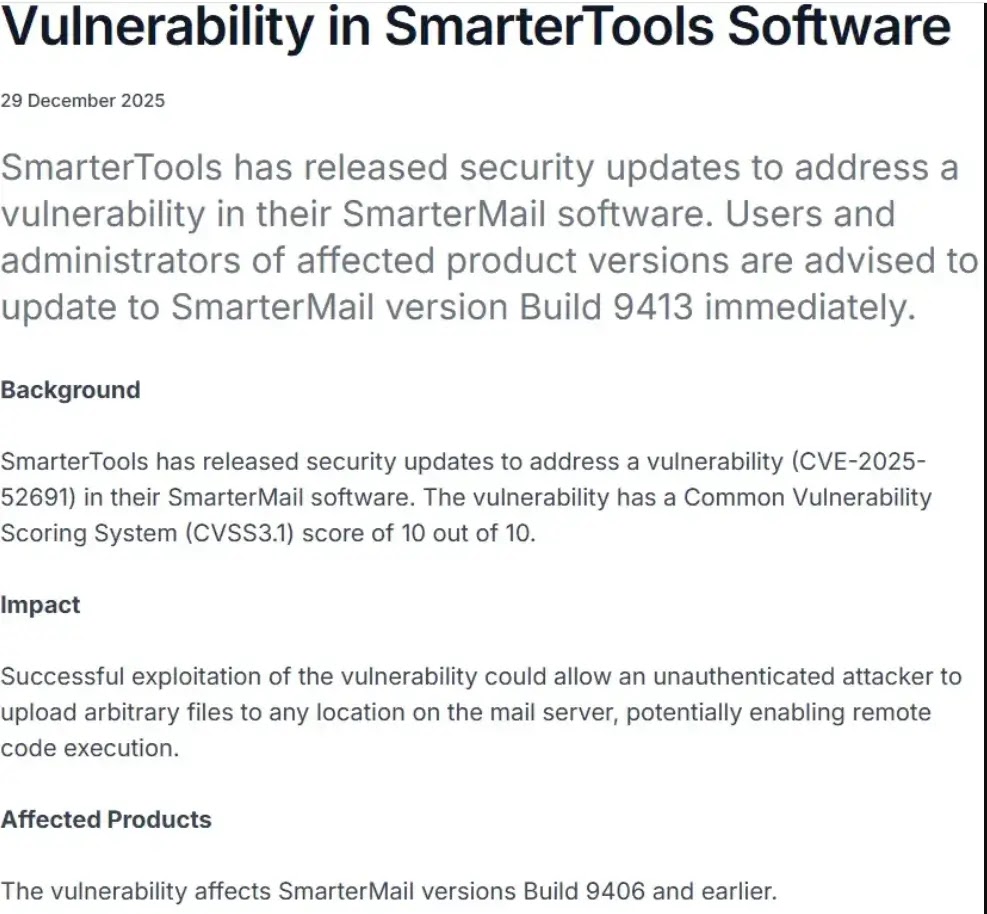
A critical pre-authentication remote code execution (RCE) vulnerability has been discovered in SmarterTools’ SmarterMail solution. This flaw is identified as CVE-2025-52691.
The flaw received a maximum CVSS score of 10.0, indicating its severe nature and potential impact on affected systems.
SmarterTools describes SmarterMail as “a secure, all-in-one business email and collaboration server for Windows and Linux – an affordable Microsoft Exchange alternative.” The platform is widely used by organizations seeking email server solutions.
| CVE ID | CVSS Score | Vulnerability Type | Affected Versions |
|---|---|---|---|
| CVE-2025-52691 | 10.0 (Critical) | Pre-Authentication Remote Code Execution | Build 9406 and earlier |
SmarterMail RCE-vulnerability”>SmarterTools SmarterMail RCE Vulnerability
Security researchers at Singapore’s Centre for Strategic Infocomm Technologies (CSIT) discovered the vulnerability, which exploits an unauthenticated file-upload endpoint in the application.
The flaw exists in the /api/upload route, specifically within the FileUploadController.Upload method that requires no authentication to access.
The vulnerability leverages a path traversal weakness in the GUID parameter validation.
Attackers can manipulate the contextData parameter to include a malicious GUID value, thereby bypassing the restricted upload directory and writing arbitrary files to any location on the system, including web-accessible directories.
By crafting a specially formatted multipart/form-data HTTP request with path traversal sequences.
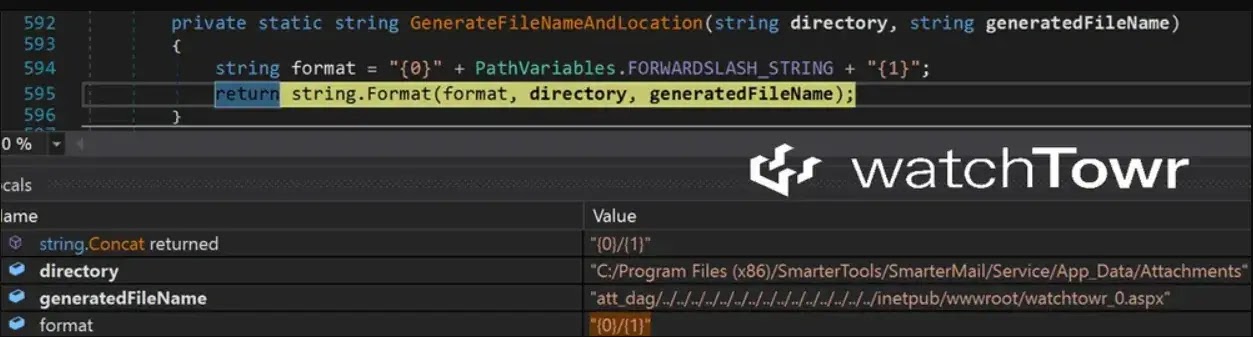
Threat actors can upload malicious ASPX webshells to the server’s root directory, achieving complete remote code execution without authentication.
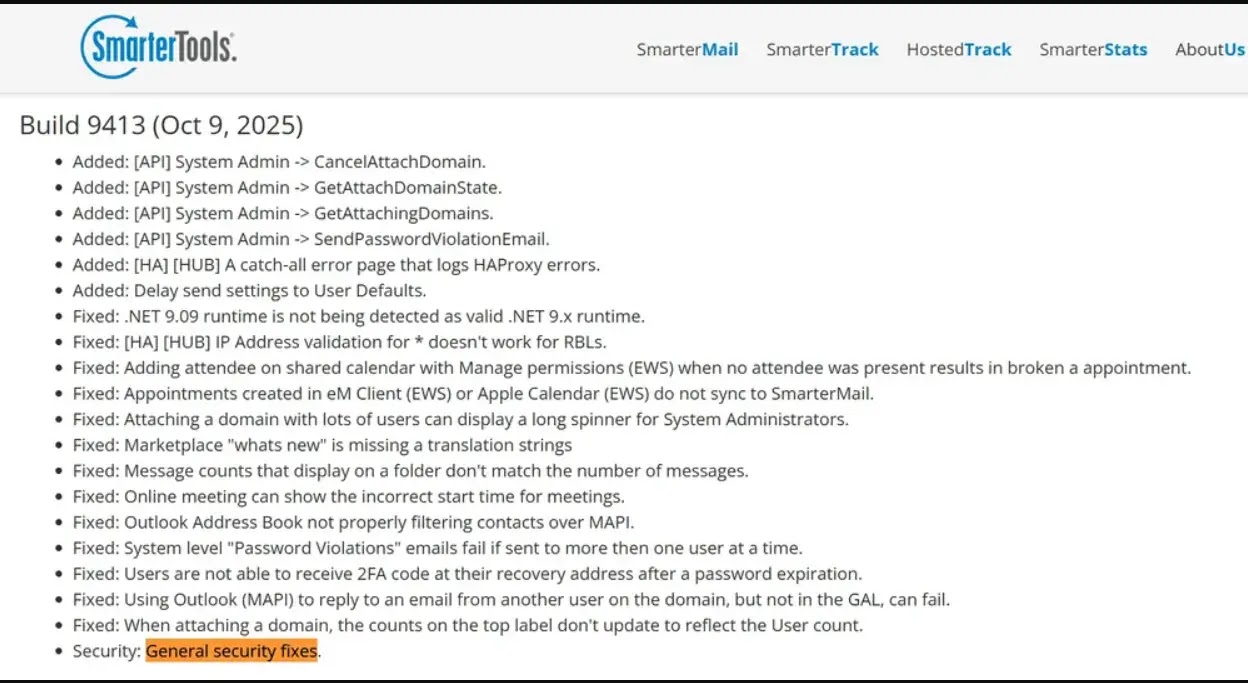
The vulnerability was silently fixed in build 9413, released on October 10, 2025. However, the official advisory from Singapore’s Cyber Security Agency (CSA) wasn’t published until late December 2025.
This three-month gap raised concerns about silent patching practices, as customers remained unaware of the critical vulnerability for approximately 2.5 months after the fix was deployed.
WatchTowr Labs has released a Detection Artifact Generator on GitHub to help organizations identify their exposure and build detection rulesets.
The tool has been verified on both Windows installations with newer builds and older versions.
Organizations running SmarterMail should immediately update to build 9413 or later to protect against potential exploitation of this critical vulnerability.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.