Hackers Exploiting AI Deployments: 91, Actively Attack
Security researchers have identified more than 91,000 attack sessions targeting AI infrastructure between October 2025 and January 2026. This activity exposes systematic campaigns against large...
Security researchers have identified more than 91,000 attack sessions targeting AI infrastructure between October 2025 and January 2026. This activity exposes systematic campaigns against large language model deployments.
GreyNoise’s Ollama honeypot infrastructure captured 91,403 attack sessions during this period, revealing two distinct threat campaigns. The findings corroborate and extend previous research from Defused on AI system targeting.
The first campaign exploited server-side request forgery vulnerabilities to force servers into making outbound connections to attacker-controlled infrastructure.
Attackers targeted Ollama’s model pull functionality by injecting malicious registry URLs and manipulating Twilio SMS webhook MediaUrl parameters.
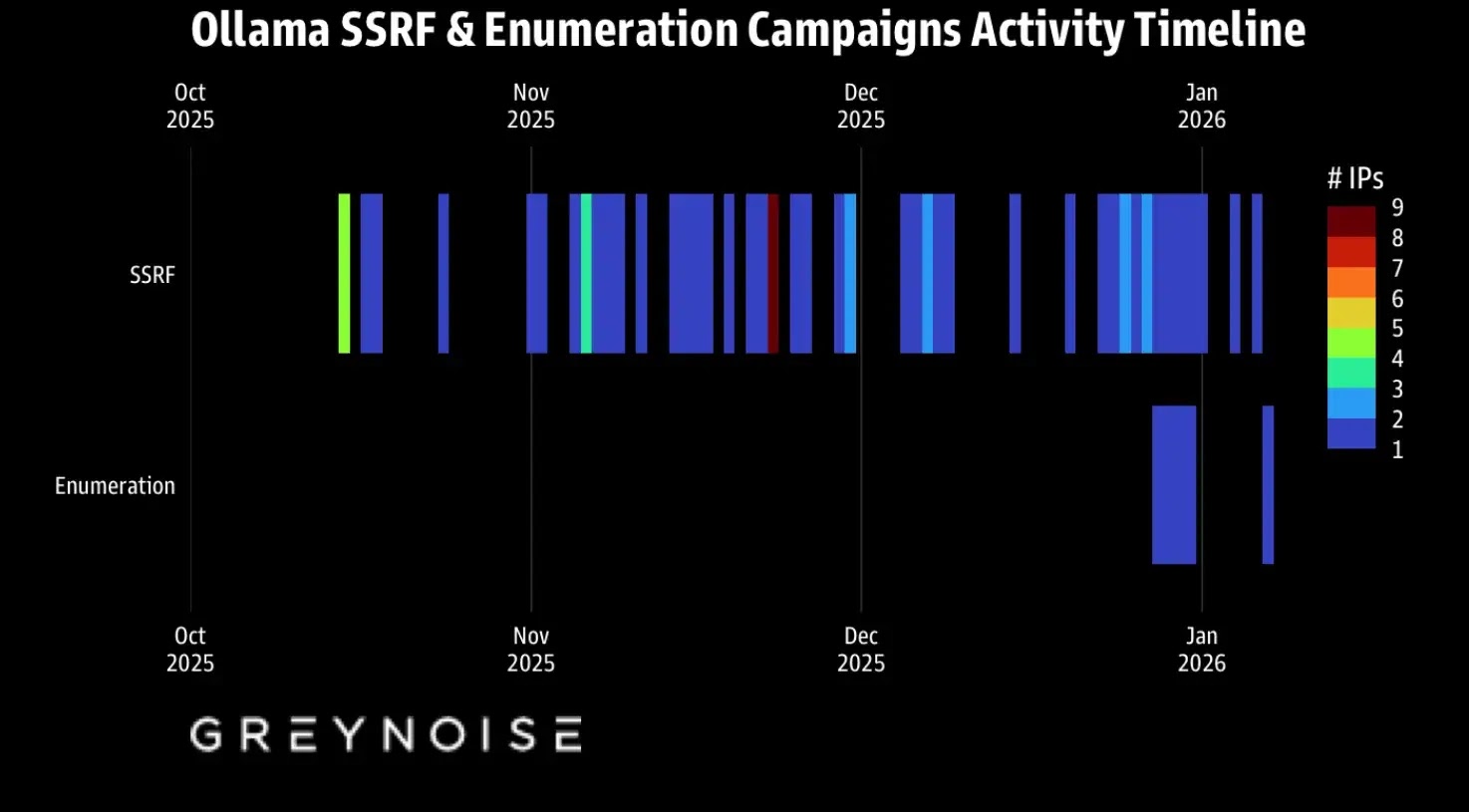
The campaign ran from October 2025 through January 2026, with a dramatic spike over Christmas, 1,688 sessions in just 48 hours.
Attackers used ProjectDiscovery’s OAST infrastructure to confirm successful exploitation via callback validation.
Fingerprinting revealed a single JA4H signature appearing in 99% of attacks, indicating shared automation tooling likely based on Nuclei.
While 62 source IPs spread across 27 countries were observed, consistent fingerprints suggest VPS-based infrastructure rather than a botnet.
GreyNoise assesses this as probable grey-hat operations by bug bounty hunters, though the scale and timing raise ethical concerns.
Enumeration Campaign: Building Target Lists
Starting December 28, 2025, two IPs launched methodical probes of 73+ LLM model endpoints, generating 80,469 sessions in eleven days.
This systematic reconnaissance sought misconfigured proxy servers that might expose access to commercial APIs.
The attacks tested OpenAI-compatible and Google Gemini formats across every major model family: OpenAI GPT-4o, Anthropic Claude, Meta Llama 3.x, DeepSeek-R1, Google Gemini, Mistral, Alibaba Qwen, and xAI Grok.
Test queries remained deliberately innocuous, with “hi” appearing 32,716 times and “How many states are there in the United States?” appearing 27,778 times, likely aiming to fingerprint models without triggering security alerts.
The infrastructure points to professional threat actors: 45.88.186.70 (AS210558, 1337 Services GmbH): 49,955 sessions 204.76.203.125 (AS51396, Pfcloud UG): 30,514 sessions
Both IPs have extensive histories of CVE exploitation, with over 4 million combined sensor hits across more than 200 vulnerabilities, including CVE-2025-55182 and CVE-2023-1389.
Block these network indicators:
| JA4H | Domains | IPs |
|---|---|---|
po11nn060000... |
*.oast.live, *.oast.me, *.oast.online, *.oast.pro, *.oast.fun, *.oast.site, *.oast.today |
45.88.186.70, 204.76.203.125, 134.122.136.119, 134.122.136.96, 112.134.208.214, 146.70.124.188, 146.70.124.165 |
Allow Ollama to make outbound connections only to approved addresses. Block all other outgoing traffic so attackers can’t use it for SSRF callbacks.
Eighty thousand enumeration requests represent a significant investment. Threat actors don’t map infrastructure at this scale without plans to exploit it.
If you’re running exposed LLM endpoints, you’re likely already on someone’s target list.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.