New Malware Attacks Windows via WhatsApp Web, Spreading to
A new campaign employing the Astaroth banking malware is actively targeting Windows systems, leveraging WhatsApp Web for automated propagation. The campaign, called Boto Cor-de-Rosa, represents a...
A new campaign employing the Astaroth banking malware is actively targeting Windows systems, leveraging WhatsApp Web for automated propagation.
The campaign, called Boto Cor-de-Rosa, represents a significant evolution in how malware spreads through messaging platforms.
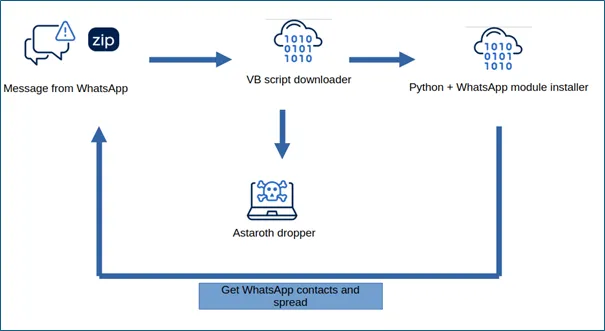
The threat specifically targets users in Brazil by exploiting WhatsApp Web to harvest contact lists and automatically send malicious messages to every contact, creating a self-sustaining infection loop.
The malware operates through a two-pronged approach that combines aggressive propagation with credential theft.
When victims receive a ZIP file through WhatsApp and extract it, they encounter a Visual Basic script disguised as a legitimate file.
Once executed, this script downloads two components: the core Astaroth banking payload written in Delphi and a Python-based WhatsApp spreader module.
The infection process begins innocuously, with file names following patterns like “552516107-a9af16a8-552.zip” to appear less suspicious.
Acronis researchers identified that the malware uses sophisticated social engineering techniques to increase its success rate.
The Python module automatically detects the time of day and sends appropriate greetings in Portuguese before delivering the malicious payload.
The message template reads “Segue o arquivo solicitado. Qualquer dvida estou disposio!” which translates to “Here is the requested file.
If you have any questions, I’m available!” This casual, familiar phrasing makes recipients more likely to trust the attachment.
Technical Breakdown of the Attack Mechanism
The propagation module includes built-in tracking mechanisms that monitor delivery metrics in real time.
The code calculates statistics such as successful deliveries, failed attempts, and sending rate measured in messages per minute.
After every 50 messages, it generates progress updates showing the percentage of contacts processed and current throughput.
The VBS downloader embedded in the ZIP archive is typically 50 to 100 KB and heavily obfuscated to avoid detection.
Once deobfuscated, it executes PowerShell commands to download components from compromised domains like coffe-estilo.com.
The downloaded MSI package deploys files into “C:MicrosoftEdgeCache6.60.2.9313” directory, including electron.exe and various DLL files that form the complete Astaroth payload.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.