Promptware Kill Chain: Five Steps to Analyze Cyberthreat
Large language models are now deeply integrated into business operations, powering everything from customer service chatbots to autonomous agents that manage calendars, execute code, and handle...
Large language models are now deeply integrated into business operations, powering everything from customer service chatbots to autonomous agents that manage calendars, execute code, and handle financial transactions.
This rapid expansion has created a critical security blind spot. Researchers have identified that attacks targeting these systems are not simple prompt injections as commonly believed, but rather sophisticated, multi-stage campaigns that mirror traditional malware operations.
This emerging threat class has been termed “promptware”—a new category of malware specifically designed to exploit vulnerabilities in LLM-based applications.
The distinction matters significantly. While the security industry has focused narrowly on prompt injection as a catch-all term, the reality is far more complex.
Attacks now follow systematic, sequential patterns: initial access through malicious prompts, privilege escalation by bypassing safety constraints, establishing persistence in system memory, moving laterally across connected services, and finally executing their objectives.
This mirrors how traditional malware campaigns unfold, suggesting that conventional cybersecurity knowledge can inform AI security strategies.
Ben Nassi, Bruce Schneier, and Oleg Brodt from Tel Aviv University, Harvard Kennedy School, and Ben-Gurion University, have proposed a comprehensive five-step kill chain model to analyze these threats.
Their framework demonstrates that contemporary LLM attacks are increasingly multistep operations with distinct intervention points, not merely surface-level injection attempts.
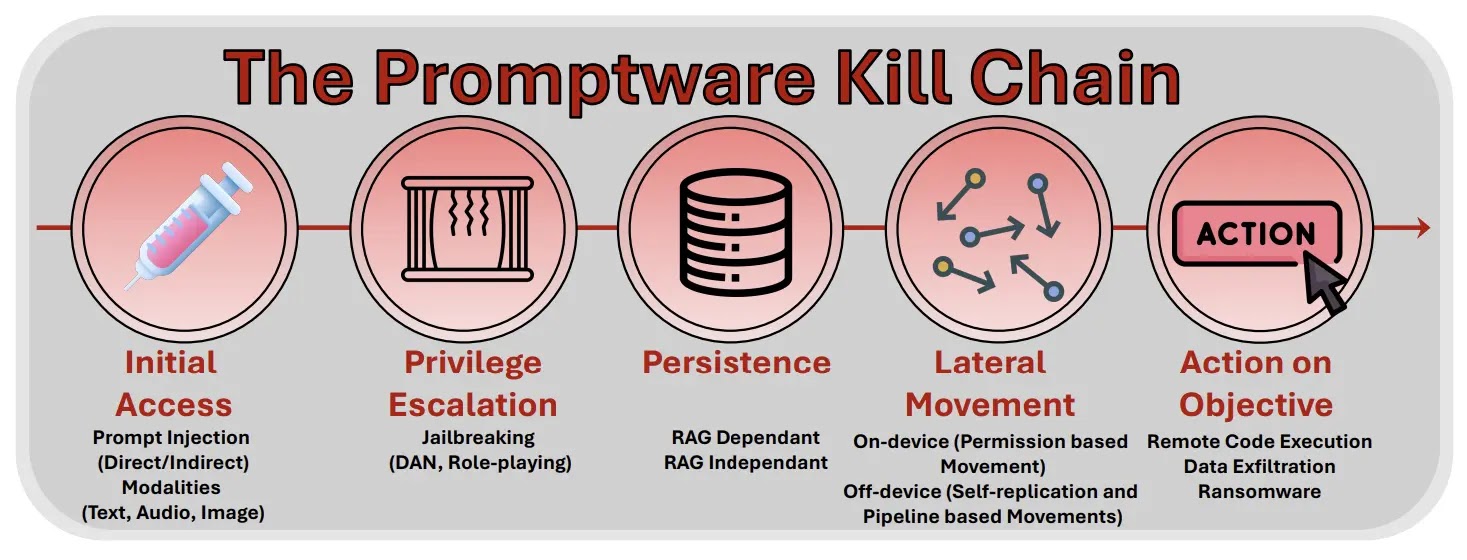
The promptware kill chain begins with Initial Access, where attackers insert malicious instructions through prompt injection—either directly from users or indirectly through poisoned documents retrieved by the system.
The second phase, Privilege Escalation, involves jailbreaking techniques that bypass safety training designed to refuse harmful requests.
Modern LLMs undergo alignment training to prevent certain activities, and sophisticated attackers have developed obfuscation methods, role-playing techniques, and even universal adversarial suffixes that work across multiple models simultaneously.
Persistence Mechanisms and Real-World Impact
Once initial access is established and safety constraints are bypassed, attackers focus on persistence. This is where promptware becomes particularly dangerous.
Traditional malware achieves persistence through registry modifications or scheduled tasks. Promptware exploits the data stores that LLM applications depend on.
Retrieval-dependent persistence embeds payloads in data repositories like email systems or knowledge bases, reactivating when the system retrieves similar content.
Even more potent is retrieval-independent persistence, which targets the agent’s memory directly, ensuring the malicious instructions execute on every interaction regardless of user input.
The Morris II worm exemplifies this threat. This self-replicating attack propagated through LLM-powered email assistants by forcing the system to include copies of the malicious payload in outgoing messages.
Recipients whose assistants processed the infected content became compromised, creating exponential infection potential.
Command-and-control channels add another layer of sophistication, allowing attackers to dynamically update payloads and modify agent behavior in real time by embedding instructions that fetch commands from attacker-controlled sources.
The evolution from theoretical vulnerability to practical exploitation has accelerated rapidly. Early attacks merely outputted refuse information.
Today’s promptware orchestrates data exfiltration, triggers phishing campaigns through compromised email systems, manipulates smart home devices, and executes unauthorized financial transactions.
Recent incidents demonstrate the full kill chain in action, transforming isolated security concerns into systemic organizational risks that demand immediate attention and revised defensive frameworks.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.