AWS Console Supply Chain Attack Hijacks GitHub Repos
Unauthenticated attackers exploited a critical misconfiguration in AWS CodeBuild, gaining control of key AWS-owned GitHub repositories. This compromise notably included the AWS JavaScript SDK, a...
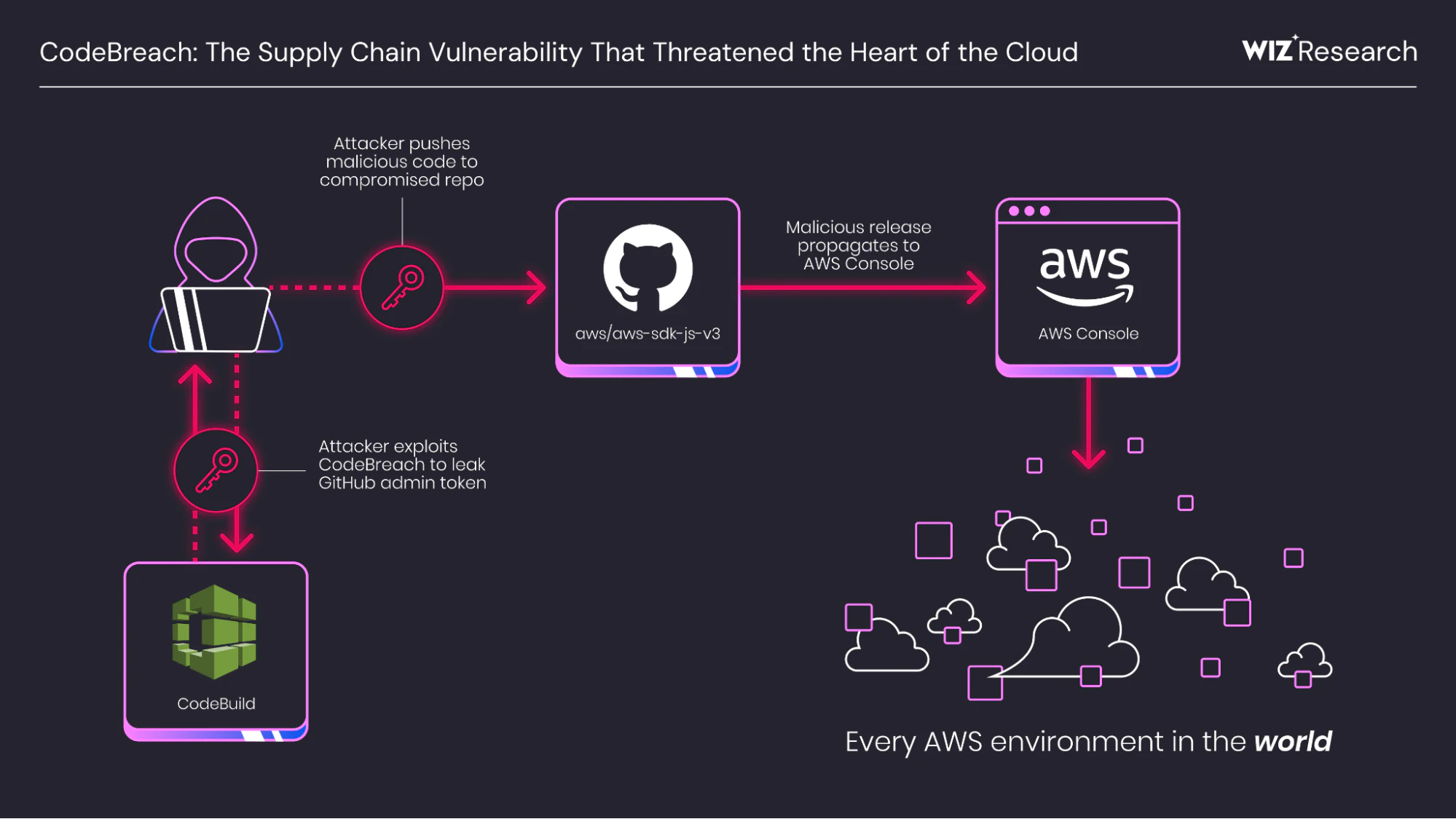
Unauthenticated attackers exploited a critical misconfiguration in AWS CodeBuild, gaining control of key AWS-owned GitHub repositories. This compromise notably included the AWS JavaScript SDK, a widely used component that powers the AWS Console itself.
This supply chain vulnerability threatened platform-wide compromise, potentially injecting malicious code into applications and the Console across countless AWS environments.
AWS Console Supply Chain Attack
Security firm Wiz Research has exposed that CodeBreach originated from unanchored regular expression patterns in CodeBuild webhook filters for the ACTOR_ID parameter, which should restrict builds to trusted GitHub user IDs.
Without ^ and $ anchors, the filter matched any user ID containing an approved substring, allowing bypass via “eclipse” events where new, longer GitHub IDs incorporate older maintainer IDs.
GitHub’s sequential ID assignment, creating about 200,000 daily, made such overlaps frequent for the targeted 6-7 digit IDs in four AWS repos: aws/aws-sdk-js-v3, aws/aws-lc, corretto/amazon-corretto-crypto-provider, and awslabs/open-data-registry.
Attackers exploit this by mass-creating GitHub Apps via the manifest flow to race for eclipse IDs, then submitting pull requests that trigger privileged builds.
In a proof-of-concept against aws/aws-sdk-js-v3 (PR #7280), hidden payload code dumped memory to extract a GitHub Personal Access Token (PAT) from the aws-sdk-js-automation account, despite prior mitigations from the 2025 Amazon Q incident.
The PAT granted repo and admin:repo_hook scopes, enabling collaborator invites for admin escalation and direct main branch pushes.
Compromising the JavaScript SDK risked infecting its weekly NPM releases, affecting 66% of scanned cloud environments and the AWS Console, which bundles recent SDK versions with user credentials, Wiz said to CybersecurityNews.
The stolen PAT also controlled related private repos, amplifying supply chain risks akin to Nx S1ngularity or the Amazon Q attack (AWS-2025-015). Wiz halted escalation post-PoC, responsibly disclosing on August 25, 2025.
| Affected Repositories | Maintainer ID Example | Eclipse Frequency |
|---|---|---|
| aws/aws-sdk-js-v3 | Short 6-7 digits | Every ~5 days |
| aws/aws-lc | Short 6-7 digits | Every ~5 days |
| corretto/amazon-corretto-crypto-provider | Short 6-7 digits | Every ~5 days |
| awslabs/open-data-registry | Short 6-7 digits | Every ~5 days |
AWS fixed the regex flaw within 48 hours, revoked tokens, hardened memory protections, audited public builds, and confirmed no exploitation via logs.
No customer data was impacted. New features like Pull Request Comment Approval and CodeBuild-hosted runners now block untrusted builds.
Users should anchor webhook regexes, use fine-grained PATs with minimal scopes, enable PR approval gates, and scan for vulnerable setups via Wiz queries.
AWS urged disabling auto-PR builds from untrusted sources. The attack flow diagram highlights the path from malicious PR to Console risk.
This underscores CI/CD as prime targets: complex, privilege-rich, and untrusted-input exposed. Public disclosure followed on January 15, 2026.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.