ProFTPD SQL Injection Flaw Allows Remote Code Execution
A critical SQL injection vulnerability has been identified in ProFTPD, one of the internet’s most widely deployed FTP servers. This flaw, tracked as CVE-2026-42167, carries a CVSS severity...
A critical SQL injection vulnerability has been identified in ProFTPD, one of the internet’s most widely deployed FTP servers. This flaw, tracked as CVE-2026-42167, carries a CVSS severity score of 8.1 and specifically impacts the mod_sql extension.
Depending on how the server is configured, attackers can exploit this bug to bypass authentication, elevate their privileges, or achieve remote code execution (RCE).
ProFTPD uses the mod_sql module to allow administrators to authenticate users via a database or to log server activity.
Administrators often use the SQLNamedQuery directive to store logs, relying on special variables like %U to insert the requested username.
The vulnerability stems from a logical flaw in the is_escaped_text() function used to process these logging variables.
When an attacker enters text that begins and ends with a single quote, with no quotes in between, the system incorrectly assumes the input is already safe.
ProFTPD’s SQL Injection Vulnerability
This bypasses standard sanitization processes and allows a malicious user to craft a specific username that tricks the database into executing unauthorized SQL commands.
Because many modern Linux distributions and web hosting platforms bundle ProFTPD, the attack surface is significant.
Web hosting administration packages frequently use this database-backed architecture to easily manage thousands of FTP users without creating individual local Linux accounts.
The exact impact of this vulnerability depends heavily on the server’s logging and database configuration.
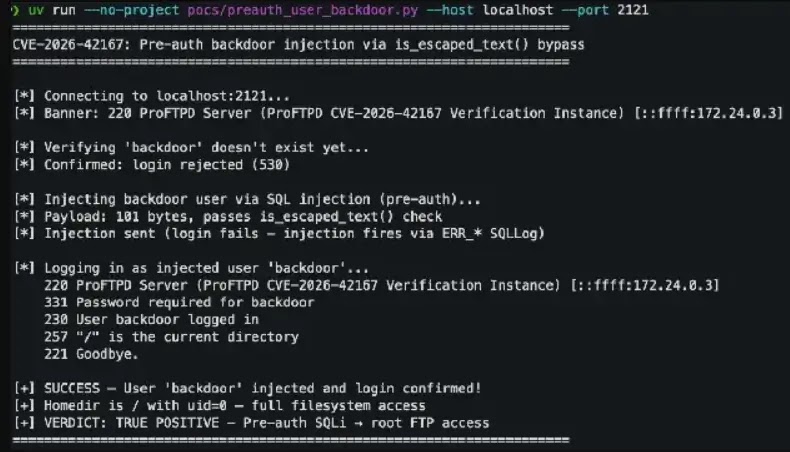
- Authentication bypass: If the server logs pre-authentication commands, attackers can use SQL injection to insert a backdoor user with full system privileges into the database.
- Remote code execution: If ProFTPD connects to a PostgreSQL database with superuser privileges, attackers can leverage the SQL injection alongside PostgreSQL’s COPY TO PROGRAM feature to run arbitrary code directly on the host server.
- Data theft: Attackers can utilize blind SQL injection techniques to slowly extract sensitive information from the database, including stored plaintext passwords or password hashes.
According to ZeroPath Research, security teams and system administrators should act immediately to protect their infrastructure from potential exploitation.
- Apply security patches: Upgrade all ProFTPD installations to version 1.3.9a or newer immediately.
- Disable SQL logging: If applying the patch is not immediately possible, administrators should disable logging via the
mod_sqlmodule to remove the attack vector. - Monitor systems: Security teams should actively monitor their FTP logs and database activity for suspicious behavior, such as unexpected user creation or unusual SQL queries.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.