KarstoRAT RAT: Remote Webcam Monitoring & Audio Recording
KarstoRAT, a newly identified remote access trojan (RAT), has emerged in sandbox analyses and malware repositories since early 2026. This novel RAT’s capabilities are detailed in a recent technical...
KarstoRAT, a newly identified remote access trojan (RAT), has emerged in sandbox analyses and malware repositories since early 2026. This novel RAT’s capabilities are detailed in a recent technical report.
The malware gives attackers a broad set of remote-control capabilities over compromised Windows machines, including webcam capture, audio recording, keylogging, screenshot theft, and the ability to fetch and run additional payloads on demand.
KarstoRAT is built to give its operators full control over an infected system from the moment it first runs.
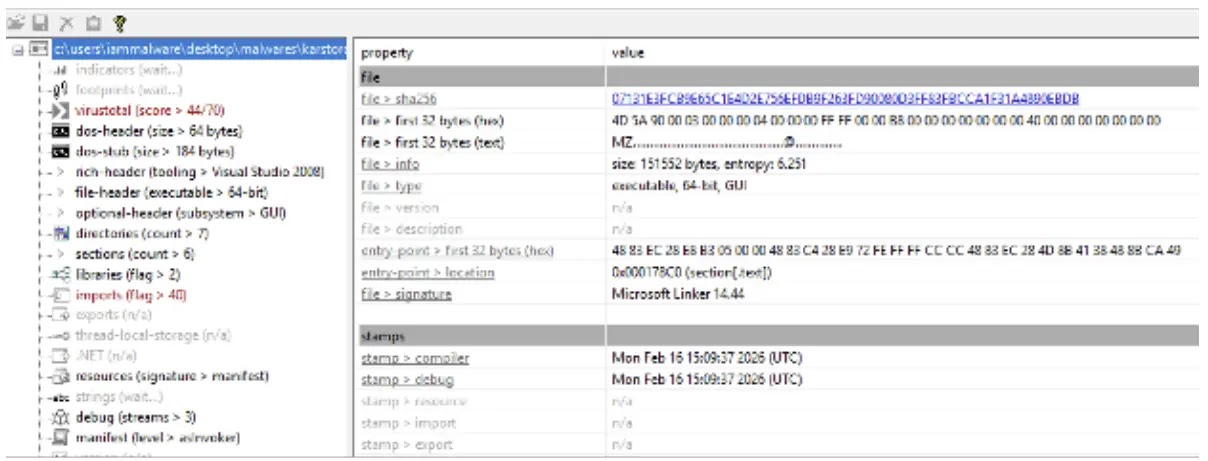
The analyzed sample is a 64-bit Windows executable compiled with Microsoft Visual Studio 2022, with a debug build timestamp of February 16, 2026.
It communicates with a hardcoded command-and-control (C2) server at 212.227.65[.]132 over port 15144, using the Windows Internet API (WinINet) for all outbound traffic.
Once running, it sends heartbeat notifications every two seconds, maintaining a constant link to the attacker’s server.
LevelBlue analysts identified KarstoRAT during a threat investigation and noted that the malware has not been publicly listed or sold on underground forums or cybercrime marketplaces.
This suggests it may be a privately developed tool used by a small group of operators, rather than a widely circulated commodity RAT.
The presence of multiple samples in public analysis environments gives researchers a rare window into a private threat that has only recently surfaced in real-world activity.
What makes KarstoRAT especially concerning is its social engineering approach to distribution. Researchers found that the C2 infrastructure hosts a fake Roblox trading website called “Blox Stocks” and a cheat download panel called “Venom Files.
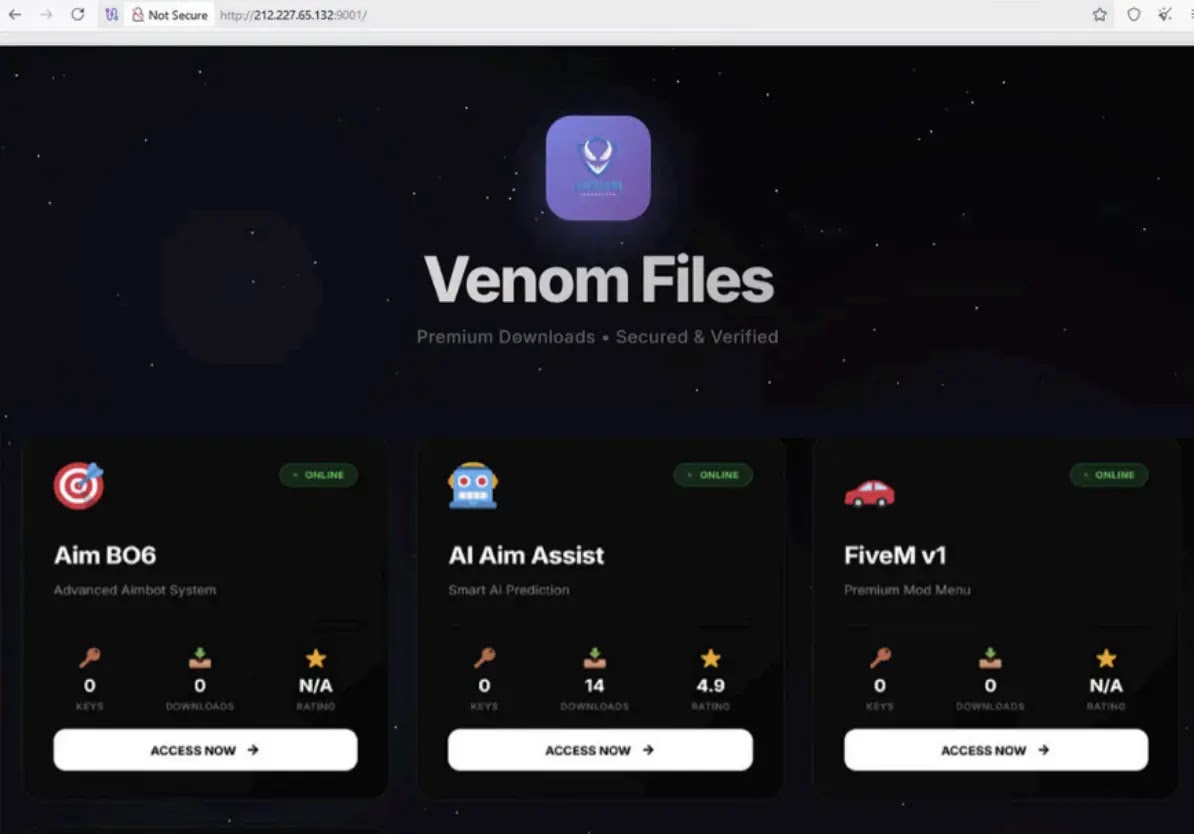
The Blox Stocks page targets younger Roblox players with promises of cheap in-game items, while the Venom Files panel lures FPS and GTA modders with so-called premium game cheats. Both pages are designed to trick users into downloading and running the malware.

The C2 server runs a layered infrastructure across multiple open ports and services, including SSH tunnels, Node.js APIs, and a VMess proxy routed through Cloudflare Argo WebSocket on port 443 with TLS fingerprinting set to Firefox.

This obfuscated setup helps the malware blend into normal traffic and maintain access inside restricted network environments.
Surveillance and Payload Execution Capabilities
Once KarstoRAT is running on a victim’s machine, it enters an infinite two-second polling loop and waits for commands from the C2 server.
The sample overview in PEStudio shows the executable has moderate entropy with no packing applied.
The webcam module, triggered by the WEBCAM command, creates an invisible capture window, connects to the default webcam driver, grabs a single still frame, saves it as a temporary BMP file (webcap.bmp), and uploads it to the /upload-webcam endpoint before removing the file from disk.
No window appears on screen and no visible alert is shown to the victim throughout the process.
The audio recording feature uses the Windows Multimedia Command Interface (MCI) to silently open the victim’s microphone, record for a duration set by the attacker, save the result as a temporary WAV file, and upload it to the /upload-audio endpoint.
The recording process runs in a dedicated background thread, keeping the main process fully responsive.
The keylogger installs a low-level keyboard hook using SetWindowsHookExA and captures every keystroke across all active applications, sending the data to the /upload-keylog endpoint via HTTP POST.
For persistence, KarstoRAT uses three distinct methods: a Windows Registry Run key named “SecurityService”, a Scheduled Task called “SystemCheck”, and a copy of itself placed in the Windows Startup folder.
A UAC bypass using fodhelper.exe allows the malware to gain elevated privileges without showing the victim any security prompt.
Organizations should immediately block the C2 IP address 212.227.65[.]132 and monitor for connections on ports 15144 and 13614.
Security teams should scan network logs for the user agent string “SecurityNotifier” and check for registry entries under HKCUSoftwareMicrosoftWindowsCurrentVersionRunSecurityService and Scheduled Tasks named “SystemCheck”.
Endpoint detection tools should be configured to flag any instance of fodhelper.exe combined with HKCU registry modifications.
All users should avoid downloading game cheats or trading tools from unverified third-party sources.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.