New Phishing Kit Attacks Google, Microsoft, As-a-service Attacking
A dangerous new generation of phishing kits, specifically designed for voice-based attacks, now poses a significant and growing threat. These sophisticated tools are increasingly targeting enterprise...
A dangerous new generation of phishing kits, specifically designed for voice-based attacks, now poses a significant and growing threat. These sophisticated tools are increasingly targeting enterprise users across major technology platforms.
Okta Threat Intelligence discovered multiple custom phishing kits available on an as-a-service basis that criminals are using in coordinated campaigns.
These sophisticated tools target employees at Google, Microsoft, Okta, and cryptocurrency platforms with alarming precision.
The kits represent a significant evolution in phishing attacks, combining technical deception with real-time social engineering tactics to overcome modern security defenses.
The emergence of these phishing-as-a-service kits signals a troubling shift in how attackers operate. Rather than deploying generic phishing pages, threat actors now use specialized tools that adapt in real-time to match specific victim environments.
The kits intercept user credentials while simultaneously displaying information that convinces targets to approve multi-factor authentication requests.
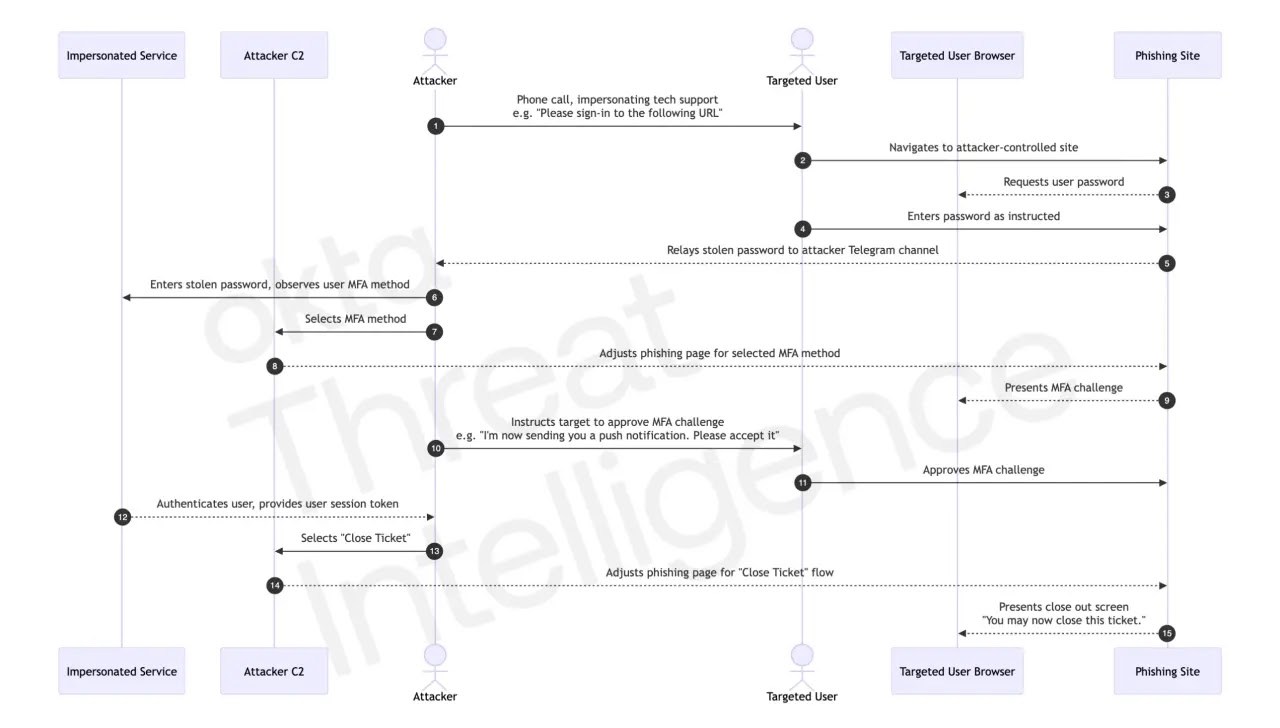
What makes these tools particularly dangerous is their ability to synchronize perfectly with a caller’s verbal instructions, creating a seamless deception that exploits the trust users place in perceived authority figures.
Okta analysts noted that these phishing kits possess client-side scripts allowing attackers to control authentication flows directly within a target’s browser.
This real-time manipulation capability represents the defining feature that separates these attacks from traditional phishing campaigns.
When a victim enters their password on a fake login page, the stolen credentials are immediately relayed to the attacker through Telegram channels.
Simultaneously, the attacker uses legitimate credentials to probe the actual service and determine which multi-factor authentication method the victim uses.
The phishing page then dynamically updates to display pages matching the specific MFA challenge type the victim will encounter.
Real-Time Session Orchestration and MFA Bypass
The infection mechanism operates through meticulous orchestration beginning with reconnaissance. Threat actors gather employee names, commonly used applications, and company IT support phone numbers before initiating contact.
They deploy customized phishing pages and call targets while spoofing official company numbers.
When victims navigate to the fake login page and enter credentials, attackers relay instructions telling victims to expect security notifications.
The phishing page instantly shifts to display fake MFA challenge screens that perfectly mirror what the victim anticipates seeing.
Attackers leveraging this approach can defeat push notification challenges by simply instructing victims over the phone to approve a notification the victim never actually received.
However, phishing-resistant authentication methods like Okta FastPass and FIDO passkeys provide genuine protection against these attacks because they cannot be fooled through social engineering alone, regardless of how sophisticated the technical deception becomes.
The rapid expansion of these phishing-as-a-service operations demonstrates a troubling professionalization of cybercriminal infrastructure.
A new generation of threat actors now sells access to specialized control panels customized for individual services rather than generic toolkit solutions.
This specialization indicates that voice-based phishing will likely intensify, with expertise increasingly sold as a service just like the tools themselves.
Organizations must immediately enforce phishing-resistant authentication methods for all critical resources and implement network restrictions that block access from known anonymizing services favored by these threat actors.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.