New Spear-Phishing Abuses Google Ads to Deliver End
A new spear-phishing campaign, dubbed Operation Poseidon, has emerged, leveraging Google’s advertising infrastructure to deliver EndRAT malware. This sophisticated tactic allows the campaign to...
A new spear-phishing campaign, dubbed Operation Poseidon, has emerged, leveraging Google’s advertising infrastructure to deliver EndRAT malware. This sophisticated tactic allows the campaign to bypass traditional security defenses.
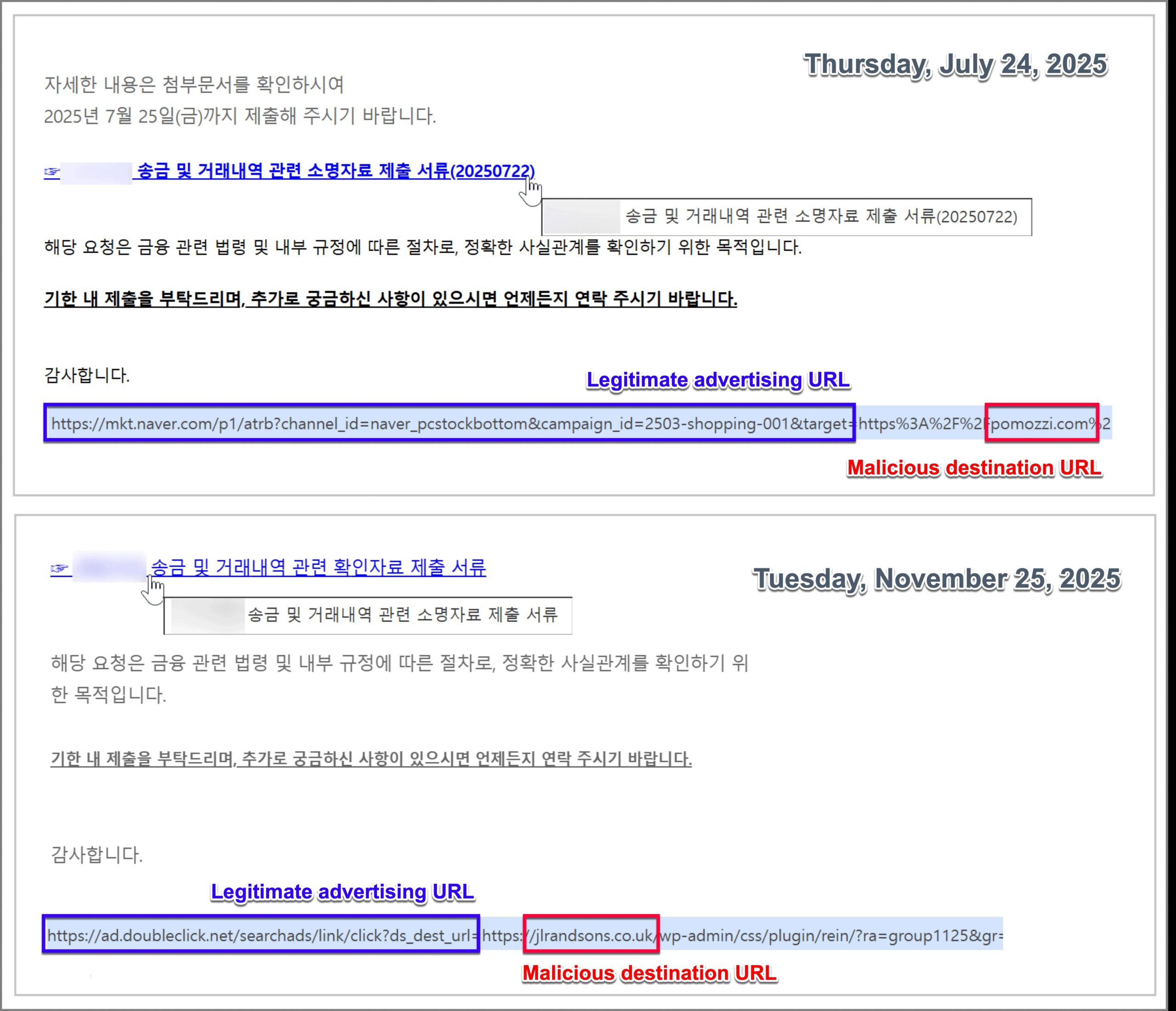
he attack leverages legitimate ad click tracking domains to disguise malicious URLs, making them appear as trustworthy advertising traffic. This technique effectively bypasses email security filters and reduces user suspicion during the initial infection stage.
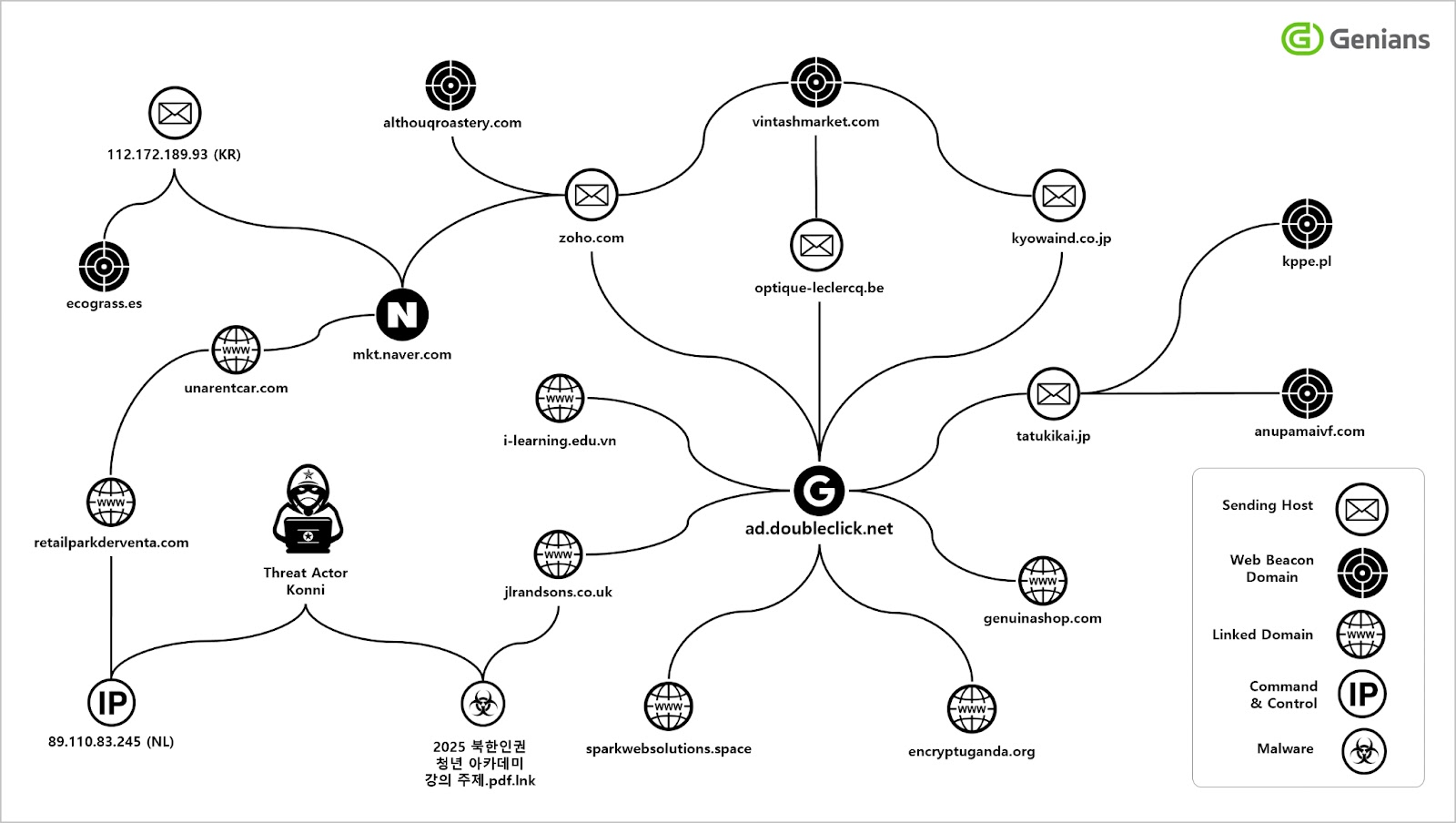
The threat actors behind this campaign belong to the Konni APT group, which has been targeting South Korean organizations through sophisticated social engineering tactics.
The attackers impersonate North Korean human rights organizations and financial institutions to lure victims into downloading malicious files.
These files are typically disguised as financial documents, transaction confirmations, or official notices that blend seamlessly into normal business communications.
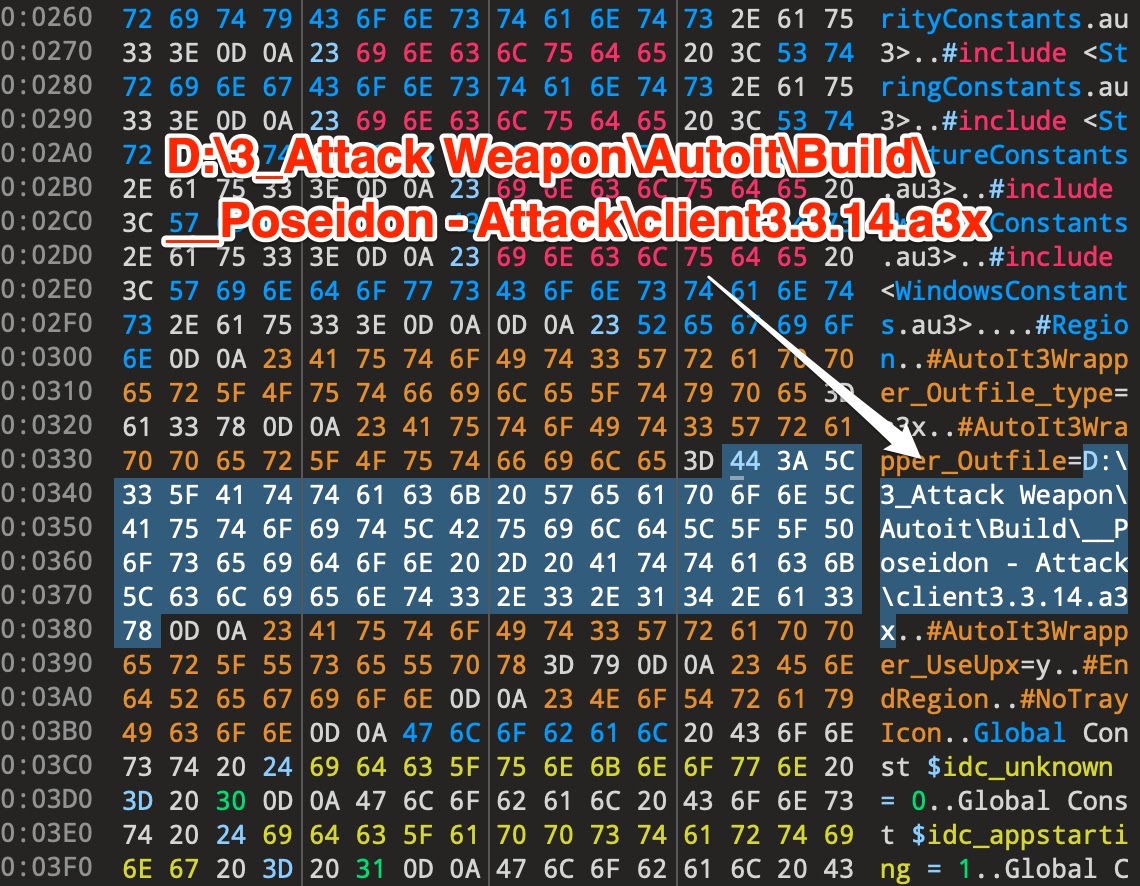
Genians analysts identified the campaign through detailed forensic analysis of malicious scripts containing internal artifacts.
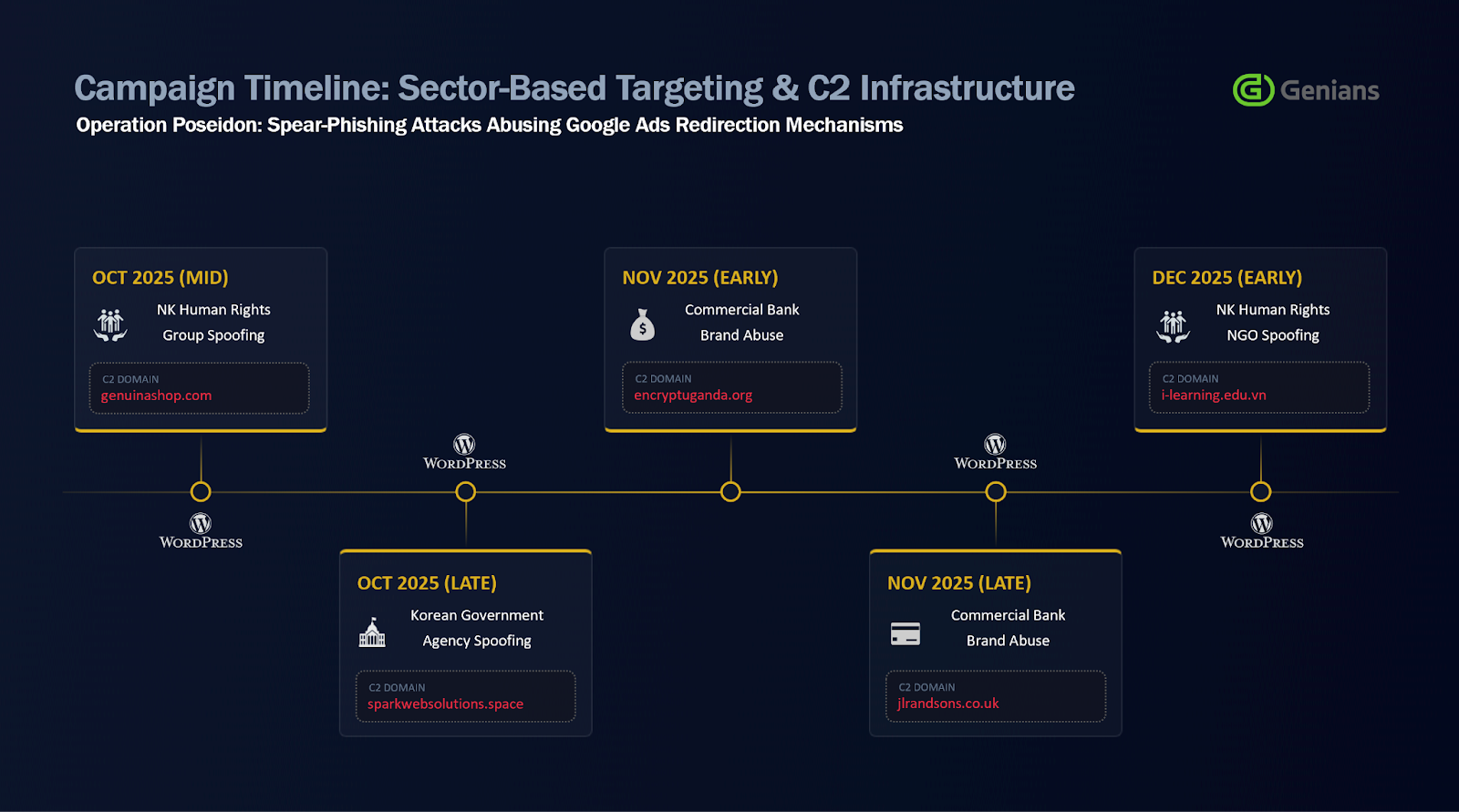
The researchers discovered that the attackers use compromised WordPress websites as malware distribution points and command-and-control infrastructure.
This approach allows rapid turnover of attack infrastructure, undermining the effectiveness of traditional URL and domain blocking policies.
The malware execution chain begins when victims click on disguised advertising URLs embedded in spear-phishing emails, which redirect them through Google’s ad.doubleclick.net domain to compromised servers hosting malicious ZIP archives.
Inside these archives are LNK shortcut files that trigger the download and execution of AutoIt scripts masquerading as PDF documents. These scripts load EndRAT-variant remote access trojans directly into memory without requiring further user interaction.
The malware includes unique identifier strings such as “endServer9688” and “endClient9688” for command-and-control communications.
Internal build paths revealed the operation’s codename “Poseidon,” suggesting organized management as a distinct operational unit within the Konni APT framework.
Attack Execution and Evasion Techniques
The attack employs multiple layers of detection evasion starting from the email delivery stage. Phishing emails contain large volumes of meaningless English text inserted into invisible HTML areas using the display:none attribute.
This content padding technique confuses AI-based phishing detection systems and spam filters by artificially lengthening email content and disrupting keyword analysis logic.
The emails also include transparent 1×1 pixel web beacons that send HTTP requests to attacker-controlled servers when opened, allowing threat actors to track recipient engagement and confirm active email addresses.
The malware delivery URLs exploit the structure of legitimate advertising platforms by embedding command-and-control addresses within URL parameters.
This makes the redirection appear as normal advertising traffic, significantly lowering detection probability.
The LNK files themselves mask file extensions and icons to appear as legitimate documents, completing a sophisticated attack chain designed to evade both signature-based and behavior-based security frameworks.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.