Free Converter Apps Infect Your Clean System Fast)
Deceptive advertisements are propagating malicious file converter applications, resulting in thousands of systems becoming infected with persistent remote access trojans (RATs). These seemingly...
Deceptive advertisements are propagating malicious file converter applications, resulting in thousands of systems becoming infected with persistent remote access trojans (RATs).
These seemingly legitimate productivity tools perform their advertised functions while secretly installing backdoors that give attackers continuous access to victim computers.
Nextron Systems found that the infection chain typically begins with malicious Google advertisements placed on legitimate websites, including video game download pages, adult content sites, and productivity tool websites.
When users search for file conversion tools like “Word to PDF converter” or image converters, these ads appear at the top of search results, making them appear trustworthy. Clicking the ad redirects victims through multiple domains before landing on fake converter websites that deliver trojanized software.
The malicious payload delivery websites share distinctive characteristics that make them recognizable once identified. Domains like ez2convertapp[.]com, convertyfileapp[.]com, powerdocapp[.]com, and pdfskillsapp[.]com all present prominent download buttons and similar page structures, including FAQs, feature descriptions, and privacy policies.
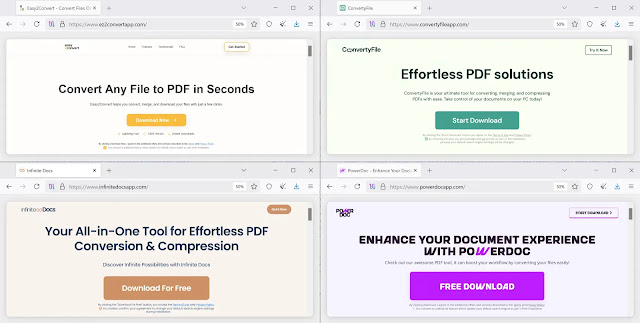
Many of these domains don’t host dropper files directly but instead redirect users to additional domains that provide the actual malicious downloads.
Code Signing Creates False Legitimacy
To evade detection and appear trustworthy, attackers sign their malware with code signing certificates from publishers like BLUE TAKIN LTD, TAU CENTAURI LTD, and SPARROW TIDE LTD.
While many certificates have been revoked after discovery, new campaigns continuously emerge with fresh, valid certificates that bypass basic security checks. This allows the malware to appear as legitimate software to both end users and security tools performing signature verification.
After download, the converter applications written in C# drop additional payloads into the %LocalAppData% directory and create scheduled tasks that execute “updater” binaries every 24 hours.
According to Nextron Systems analysis, the scheduled tasks typically start one day after initial infection, and this “+1 day” offset serves as a useful forensic indicator for pinpointing the initial access timestamp. A system-specific UUID stored in an id.txt file identifies each victim during command-and-control (C2) communications.
The final-stage payload functions as a generic execution engine that contacts attacker-controlled C2 servers to retrieve and execute malicious .NET assemblies. These RATs provide attackers with capabilities including data theft, keylogging, screen capture, file system access, and the ability to download additional malware.
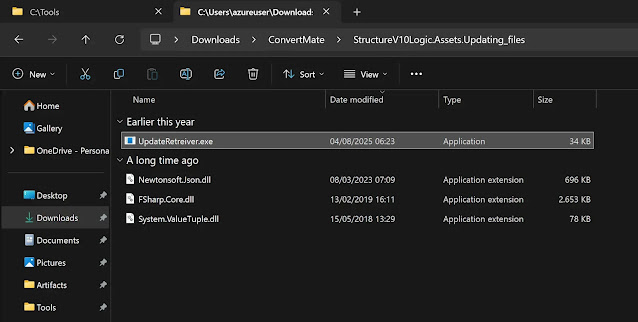
The UpdateRetriever.exe component authenticates with the C2 server, receives executable code, and runs it silently on the victim system while sending results back to attackers.
Organizations can detect these infections by monitoring Windows Event ID 4698 (scheduled task created) in Security.evtx logs, which requires enabling object access auditing.
Suspicious scheduled tasks executing from %LocalAppData% directories serve as excellent detection anchors, especially when combined with Sysmon Event ID 13 registry monitoring and Task Scheduler Operational events.
Additional defenses include implementing application control policies, such as AppLocker, to block execution from user-writable locations, and creating deny rules for identified malicious code-signing certificates.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.