Azure AD Conditional Access Bypass: Phantom Device PR
At the heart of cloud identity security lies Microsoft Entra ID (formerly Azure AD) Conditional Access. This critical component functions as the primary digital gatekeeper, meticulously checking user...
At the heart of cloud identity security lies Microsoft Entra ID (formerly Azure AD) Conditional Access. This critical component functions as the primary digital gatekeeper, meticulously checking user locations, calculating risk scores, and verifying device health before granting access.
However, an authorized red team engagement by Howler Cell recently revealed a critical attack path that entirely bypasses these vital protections.
Starting with a single set of valid credentials, often purchased for just a few hundred dollars on cybercriminal markets, researchers successfully compromised a production tenant containing over 16,000 users.
This attack required no interaction with corporate endpoints. It deployed no malware, highlighting severe gaps in default device registration and compliance validation.
The engagement by Howler Cell closely mirrored real-world tactics used by Storm-2372, a suspected Russian state-aligned threat actor.
Both the researchers and threat actors exploited unprotected Device Registration Service (DRS) endpoints to establish initial footholds, proving that blocked credentials are not a dead end for sophisticated attackers.
Azure AD Conditional Access Bypassed
According to Howler Cell’s comprehensive research, the operation began with valid credentials explicitly blocked by a CA policy, resulting in an AADSTS53003 error.
To bypass this, researchers targeted the DRS endpoint using the device code authentication flow, an avenue left open by unenforced security policies.
This allowed them to authenticate successfully and proceed to the next phase of the attack.
Using a single command, the Howler Cell team registered a phantom device with a signed Azure AD certificate and private key.
The DRS API does not validate if the caller is a physical Windows machine, allowing a Linux laptop to masquerade as a legitimate endpoint.
This step leveraged the MITRE ATT&CK technique for Account Manipulation (T1098.005).
With the phantom device registered, researchers minted a Primary Refresh Token (PRT) containing false device claims.
When this PRT was exchanged for an access token, Azure AD determined that the session was device-authenticated.
This completely bypassed CA policies that required a compliant or joined device, granting access to the broader tenant environment for directory enumeration.
To bypass policies strictly requiring an Intune-compliant device, the researchers exploited a known gap in Intune enrollment restrictions.
By claiming hybrid domain-join status, the phantom device bypassed pre-registration requirements.
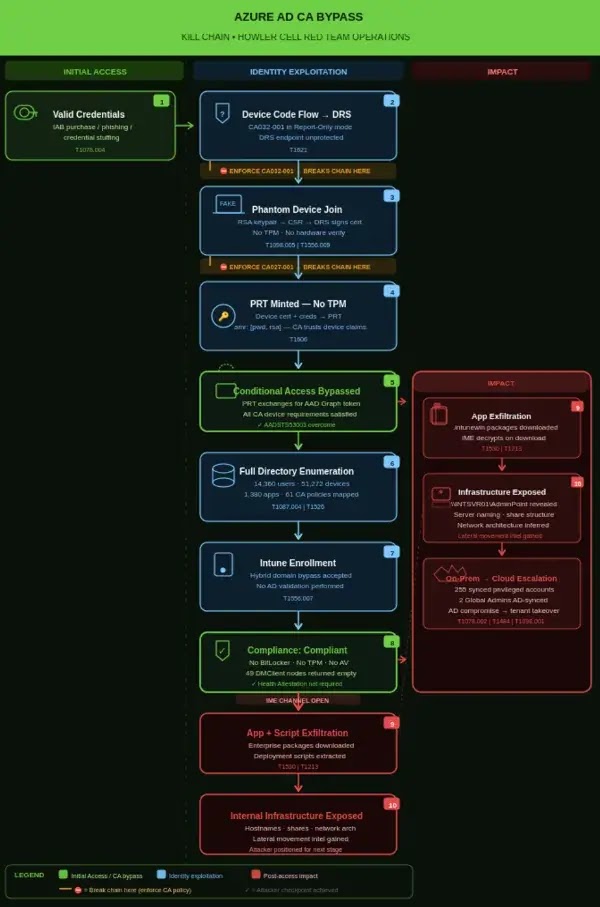
Intune trusted the client’s self-declared domain membership without verifying it against on-premises Active Directory.
Once enrolled, the device achieved compliance despite lacking BitLocker, Secure Boot, or antivirus software.
Intune’s evaluation logic treated missing health attestation responses as “not applicable” rather than non-compliant.
This permissive default posture allowed the researchers to download internal enterprise applications, and extracting a single package revealed critical internal server naming conventions and network architecture.
Escalation and Mitigation
Independent of device spoofing, researcher Howler Cell from Cyderes identified a structural risk in hybrid identity environments.
They discovered 255 highly privileged directory roles, including multiple Global Administrators, synced directly from on-premises Active Directory.
Compromising these on-premises accounts provides attackers with a direct path to complete cloud tenant takeover without needing any cloud-specific exploits.
To defend against these complex attack chains, organizations must harden their device trust models.
Crucial mitigations include:
- Enforcing report-only CA policies that block device code flows and require MFA for device registration.
- Mandating TPM 2.0 attestation as a strict prerequisite for all PRT issuance.
- Requiring external validation of device health through the Microsoft Health Attestation Service rather than relying on self-reported data.
- Scoping user-level Graph API access to prevent unauthorized bulk directory enumeration.
- Restricting privileged directory roles exclusively to cloud-only accounts managed through Privileged Identity Management.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.







No Comment! Be the first one.