Cloudflare Zero-Day Allows Any Host Access Byp Vulnerability Enables
A critical zero-day vulnerability has been identified within Cloudflare’s Web Application Firewall (WAF). This flaw permitted attackers to bypass security controls, enabling direct access to...
A critical zero-day vulnerability has been identified within Cloudflare’s Web Application Firewall (WAF). This flaw permitted attackers to bypass security controls, enabling direct access to protected origin servers by exploiting a certificate validation path.
Security researchers from FearsOff discovered that requests targeting the /.well-known/acme-challenge/ directory could reach origins even when customer-configured WAF rules explicitly blocked all other traffic.
The Automatic Certificate Management Environment (ACME) protocol automates SSL/TLS certificate validation by requiring Certificate Authorities (CAs) to verify domain ownership.
In the HTTP-01 validation method, CAs expect websites to serve a one-time token at /.well-known/acme-challenge/{token}. This path exists on nearly every modern website as a silent maintenance route for automated certificate issuance.
The design intention limits this access to a single validation bot checking one specific file, not as an open gateway to the origin server.
Cloudflare Zero-Day Vulnerability
FearsOff researchers detected the vulnerability while reviewing applications where WAF configurations blocked global access and permitted only specific sources.
Testing revealed that requests directed at the ACME challenge path bypassed WAF rules entirely, allowing the origin server to respond directly instead of returning Cloudflare’s block page.
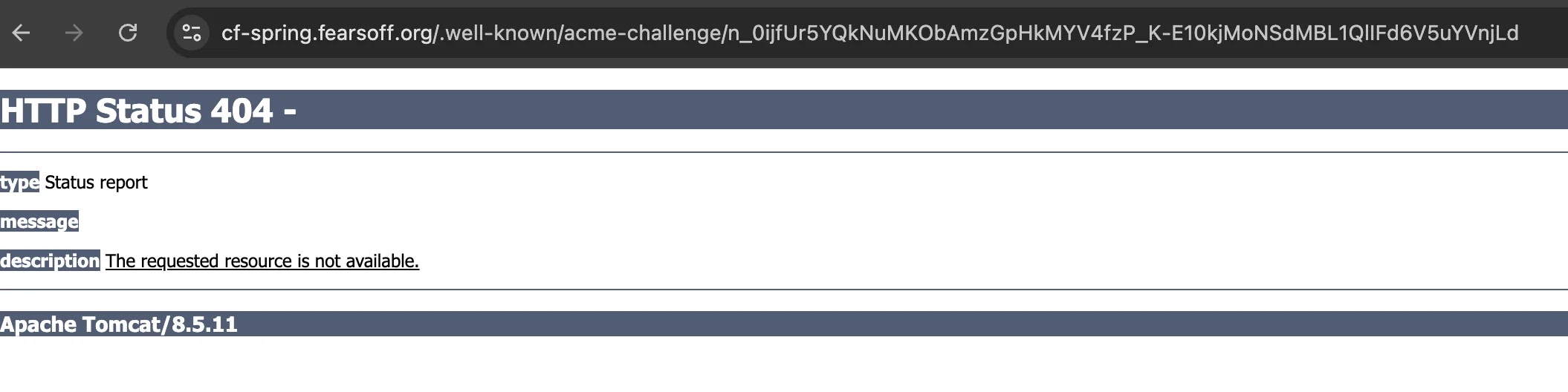
To confirm this wasn’t a tenant-specific misconfiguration, researchers created controlled demonstration hosts at cf-php.fearsoff.org, cf-spring.fearsoff.org, and cf-nextjs.fearsoff.org.
Normal requests to these hosts encountered block pages as expected, but ACME path requests returned origin-generated responses, typically framework 404 errors.
The vulnerability stemmed from Cloudflare’s edge network processing logic for ACME HTTP-01 challenge paths. When Cloudflare served challenge tokens for its own managed certificate orders, the system disabled WAF features to prevent interference with CA validation.
However, a critical flaw emerged: if the requested token didn’t match a Cloudflare-managed certificate order, the request bypassed WAF evaluation entirely and proceeded directly to the customer origin.
This logic error transformed a narrow certificate validation exception into a broad security bypass affecting all hosts behind Cloudflare protection.
The bypass allowed researchers to demonstrate multiple attack vectors against common web frameworks. On Spring/Tomcat applications, servlet path traversal techniques using ..;/ accessed sensitive actuator endpoints that exposed process environments, database credentials, API tokens, and cloud keys.
Next.js server-side rendering applications leaked operational data through direct origin responses that were never intended for public internet access.
PHP applications with local file inclusion vulnerabilities became exploitable, allowing attackers to access the file system via malicious path parameters. Beyond framework-specific attacks, account-level WAF rules configured to block requests based on custom headers were completely ignored for ACME path traffic.
FearsOff reported the vulnerability through Cloudflare’s HackerOne bug bounty program on October 9, 2025. Cloudflare initiated validation on October 13, 2025, and HackerOne triaged the issue on October 14, 2025.
The company deployed a permanent fix on October 27, 2025, modifying the code to disable security features only when requests match valid ACME HTTP-01 challenge tokens for the specific hostname.
Post-fix testing confirmed WAF rules now apply uniformly across all paths, including the previously vulnerable ACME challenge route. Cloudflare stated that no customer action is required and confirmed that no evidence of malicious exploitation has been found.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.