Microsoft Defender RedSun 0-Day Grants Full SYSTEM Access
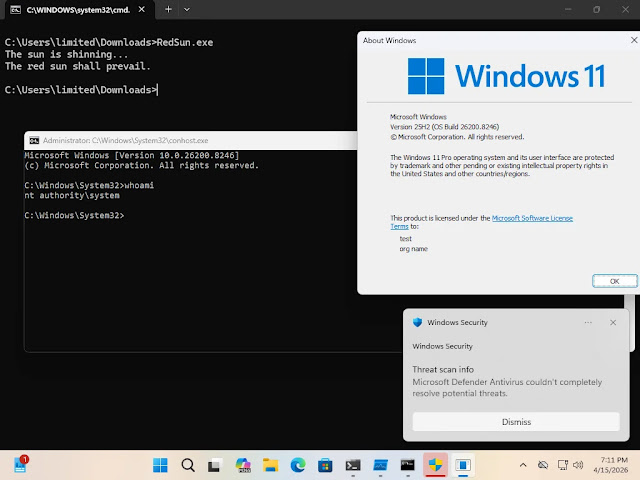
A newly disclosed zero-day vulnerability has been found in Microsoft Defender. Dubbed “RedSun,” this flaw allows an unprivileged user to escalate privileges to full SYSTEM-level access....
A newly disclosed zero-day vulnerability has been found in Microsoft Defender. Dubbed “RedSun,” this flaw allows an unprivileged user to escalate privileges to full SYSTEM-level access. It affects fully patched Windows 10, Windows 11, and Windows Server 2019 and later systems. As of now, the vulnerability remains unpatched.
RedSun is the second zero-day exploit published within a two-week span in April 2026 by the security researcher known as “Chaotic Eclipse” (also referred to as Nightmare-Eclipse on GitHub).
The first exploit, BlueHammer, targeted a different Microsoft Defender local privilege escalation (LPE) flaw and was tracked as CVE-2026-33825, which Microsoft patched as part of April 2026’s Patch Tuesday updates.
RedSun follows the same exploit tradition but introduces an entirely new and independent attack vector, suggesting that Defender’s architectural weaknesses run far deeper than a single isolated flaw.
RedSun Exploit for Microsoft Defender
At the heart of RedSun is a deeply ironic logic flaw inside Windows Defender’s cloud file handling mechanism. When Defender detects a malicious file bearing a cloud tag, rather than simply quarantining or deleting the file, it inexplicably rewrites the file back to its original location. RedSun weaponizes this behavior through the following attack chain:
- The attacker writes an EICAR test file to the filesystem using the Windows Cloud Files API (cldapi.dll)
- An opportunistic lock (oplock) is used to pause Defender’s file restoration process mid-operation
- NTFS directory junctions and reparse points redirect the write target path to
C:WindowsSystem32 - When Defender resumes, it follows the redirected path and overwrites a critical system binary — such as
TieringEngineService.exe— with SYSTEM-level privileges - The attacker then executes the overwritten binary to obtain full SYSTEM-level code execution
Independent security researcher Will Dormann, principal vulnerability analyst at Tharros, confirmed that the exploit works reliably on fully patched Windows 10, Windows 11, and Windows Server 2019 and later.
Any Windows system with Windows Defender enabled and the cldapi.dll component present is potentially vulnerable. Affected platforms include:
- Windows 10 (all supported versions)
- Windows 11 (all supported versions)
- Windows Server 2019, 2022, and 2025
The exploit functions with approximately 100% reliability even against systems with the latest April 2026 updates applied, making it particularly dangerous in enterprise environments.
The associated CVE identifier is CVE-2026-33825, carrying a CVSS score of 7.8 (High). The vulnerability is classified under CWE: Insufficient Granularity of Access Control, and its MITRE ATT&CK mapping falls under Privilege Escalation (TA0004).
The full PoC code has not been publicly released by the researcher, though the exploit methodology has been publicly documented on GitHub.
Unlike BlueHammer, which Microsoft addressed in its April 2026 Patch Tuesday cycle, RedSun currently has no available patch. Security teams are advised to monitor for anomalous Defender file write activity, particularly involving cldapi.dll operations targeting C:WindowsSystem32, and to implement endpoint detection rules to flag oplock-assisted file redirection behaviors until Microsoft issues a formal fix.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.