Microsoft Exposes Kazuar Malware’s Modular P Details Malware’s
Kazuar, a nation-state malware, has resurfaced. Its design now appears far more dangerous than initially expected. What once started as a relatively standard backdoor has now grown into a fully...
Kazuar, a nation-state malware, has resurfaced. Its design now appears far more dangerous than initially expected.
What once started as a relatively standard backdoor has now grown into a fully modular, peer-to-peer botnet specifically engineered for long-term, covert espionage against high-value government and diplomatic targets.
The group behind it, known as Secret Blizzard, has been quietly upgrading this powerful tool for years while flying well under the radar of most security teams operating around the world.
Kazuar has been linked to some of the most sensitive targets on the planet. The malware has been actively used to go after government ministries, embassies, defense departments, and diplomatic organizations across Europe and Central Asia.
Secret Blizzard is also known for piggybacking on systems in Ukraine that were previously compromised by another threat actor called Aqua Blizzard, a tactic that reflects just how calculated and patient this threat group truly is.
Analysts at Microsoft identified the malware and shared their findings in a detailed technical report, noting how Kazuar is no longer the simple tool it once was.
Microsoft said in a report shared with Cyber Security News (CSN) that the malware has expanded well beyond its origins, now operating as a structured ecosystem of three distinct modules that each play a specific and clearly defined role inside a compromised network.
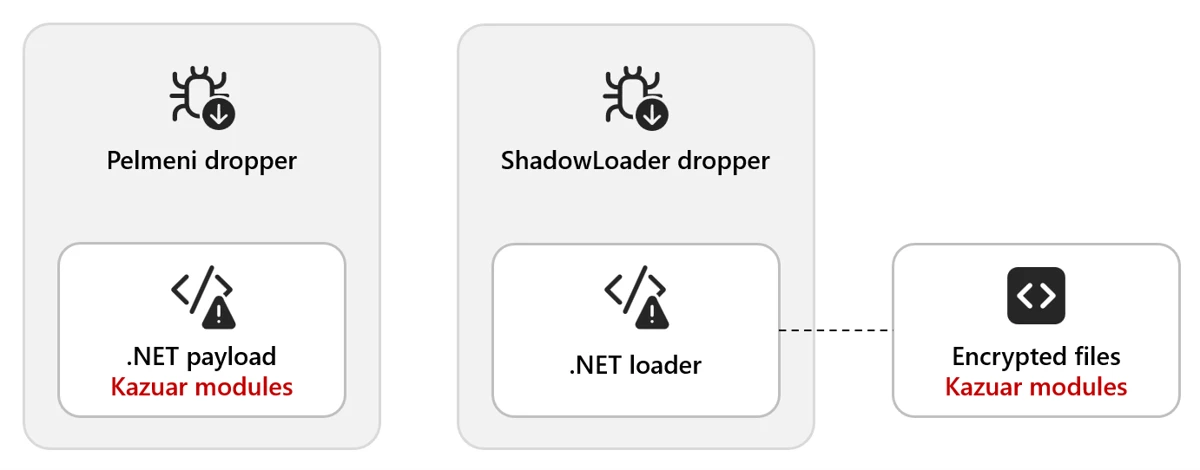
The delivery mechanism itself is already a strong sign of how advanced this malware has become. Kazuar typically arrives through a dropper called Pelmeni, which embeds an encrypted second-stage payload directly inside it.
In some cases, that payload is even bound to the target’s specific device, meaning it will only decrypt and run on the exact machine it was designed for, making early detection significantly harder for any defender.
The scope of what Kazuar collects is deeply alarming. From keystrokes and screenshots to email content, browser data, running processes, and USB devices, the malware gathers nearly everything about a compromised system.
All of this data gets encrypted, staged locally, and eventually sent back to the attackers through carefully timed communication windows designed to blend seamlessly in with normal-looking business network traffic.
Kazuar’s Modular Architecture Explained
Kazuar is built around three core modules: Kernel, Bridge, and Worker. Each has its own clearly defined responsibility. The Kernel module acts as the command center, managing tasks and maintaining operational logs.
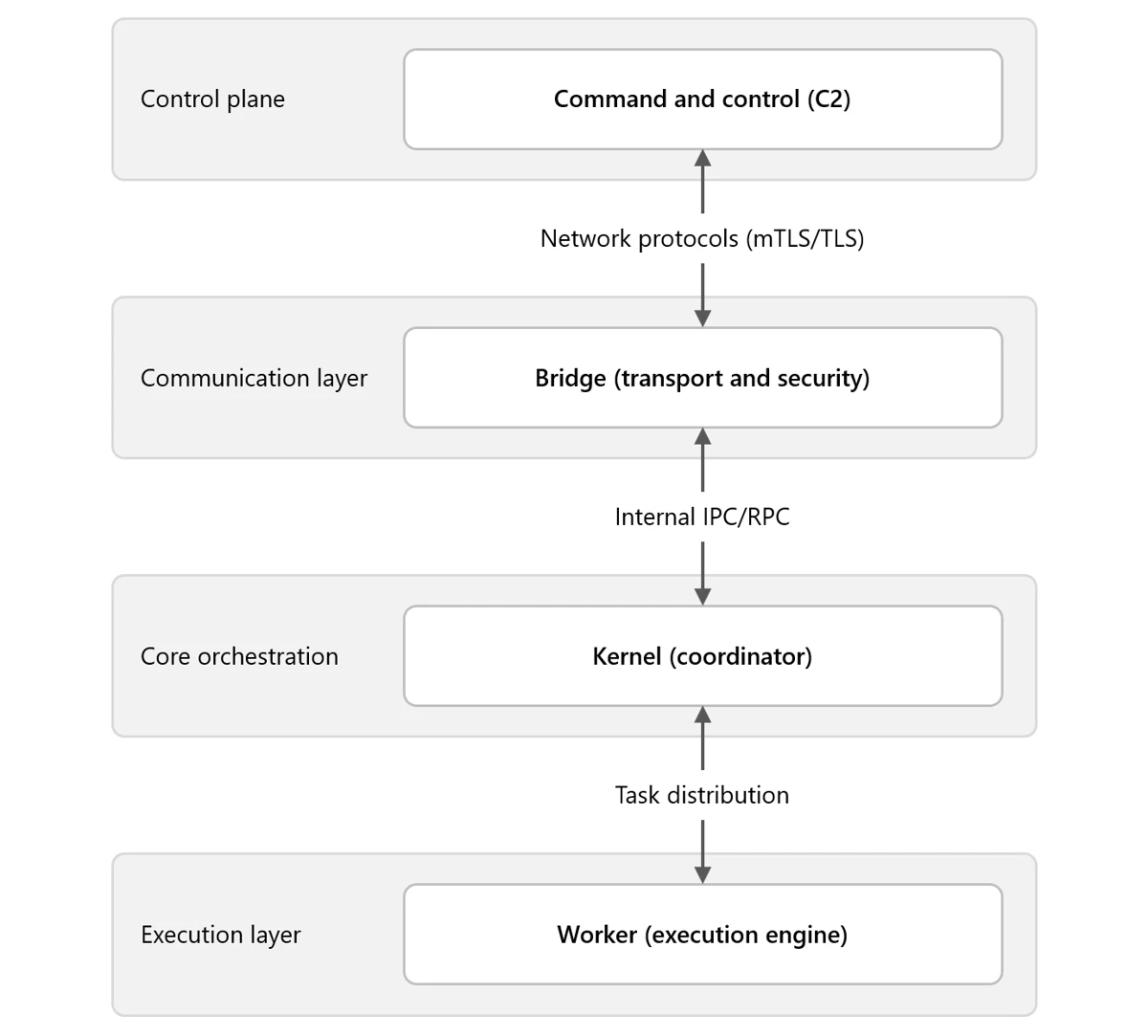
The Bridge module handles all outside communication, acting as a relay between the Kernel and the remote attacker server.
The Worker module does the actual collection work, quietly gathering files, screenshots, keystrokes, and detailed system information directly from the infected host environment.
What makes this design so effective is the leadership election system built directly into the Kernel module. Among all infected machines, only one is elected as the leader at any given time, and only that elected leader is permitted to communicate with the outside world.
This means the entire botnet produces very little suspicious external network traffic. If the leader goes offline, a new one is elected automatically, keeping operations running without any manual intervention from the attackers themselves.
P2P Botnet Operations and Stealth Tactics
The peer-to-peer structure of Kazuar is what truly sets it apart from most malware seen in the wild today. Rather than every infected machine independently reaching out to an attacker server, Kazuar routes all communication through a single elected node.
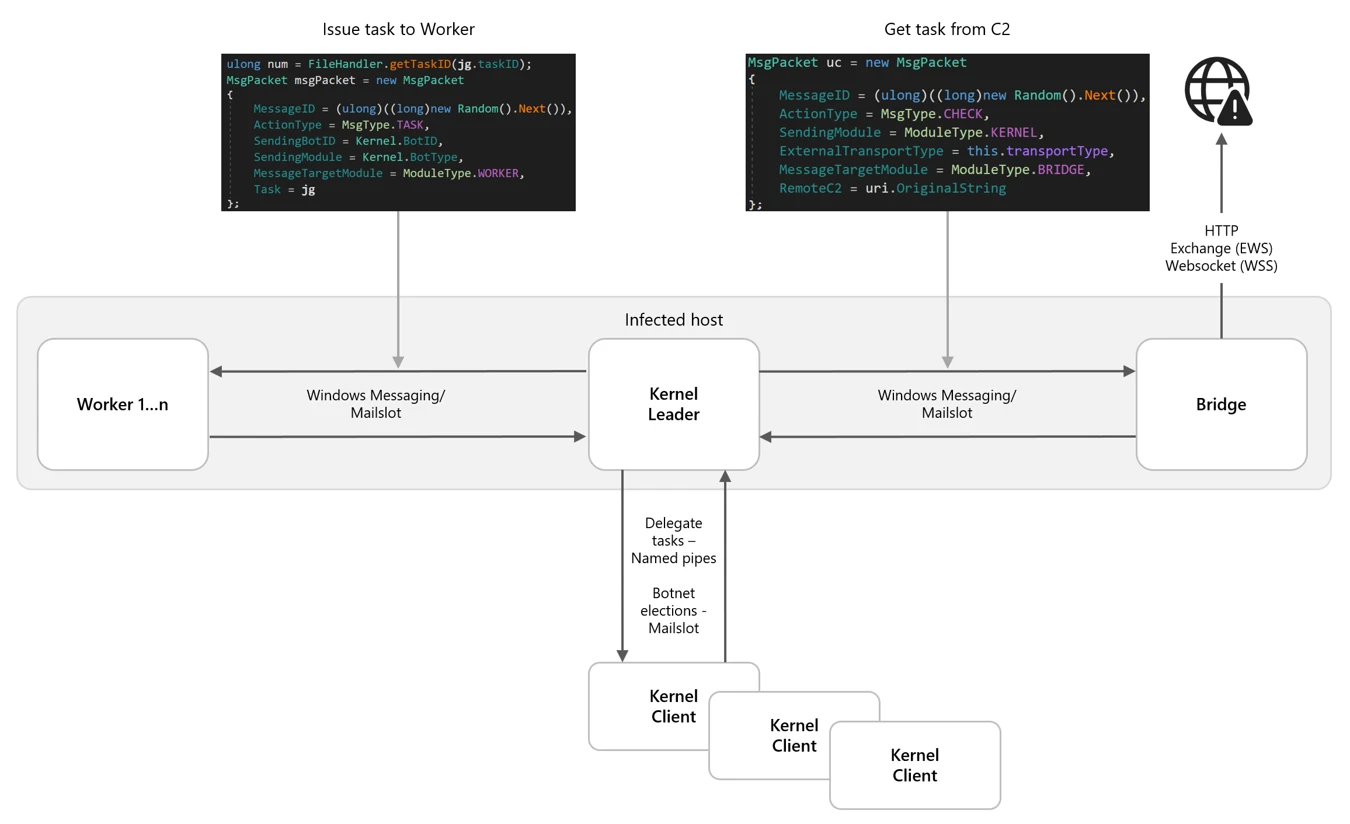
This approach drastically reduces the observable footprint and makes it significantly harder for security teams to detect or disrupt the full operation before serious damage has been done.
Kazuar supports over 150 configuration types, meaning attackers can change how it behaves at virtually any time. It can switch between HTTP, WebSocket, and even email-based communication through Exchange Web Services.
Security teams are advised to monitor for unusual named pipe activity, hidden windows registered by unknown processes, and encrypted files being written to local working directories, as these are key behavioral signals tied directly to Kazuar’s internal communication and data staging methods.
Indicators of Compromise (IoCs):-
| Type | Indicator | Description |
|---|---|---|
| SHA-256 | 69908f05b436bd97baae56296bf9b9e734486516f9bb9938c2b8752e152315d4 |
hpbprndiLOC.dll – Kazuar Loader |
| SHA-256 | c1f278f88275e07cc03bd390fe1cbeedd55933110c6fd16de4187f4c4aaf42b9 |
Decrypted Kernel Module |
| SHA-256 | 6eb31006ca318a21eb619d008226f08e287f753aec9042269203290462eaa00d |
Decrypted Bridge Module |
| SHA-256 | 436cfce71290c2fc2f2c362541db68ced6847c66a73b55487e5e5c73b0636c85 |
Decrypted Worker Module |
Note: IP addresses and domains are intentionally defanged (e.g., [.]) to prevent accidental resolution or hyperlinking. Re-fang only within controlled threat intelligence platforms such as MISP, VirusTotal, or your SIEM.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.







No Comment! Be the first one.