Hackers Abuse Scheduled Tasks for FrostyNeighbor Persistence
The state-aligned hacking group FrostyNeighbor has initiated a new series of cyberattacks against Ukrainian government organizations. These latest attacks employ a meticulously crafted infection...
The state-aligned hacking group FrostyNeighbor has initiated a new series of cyberattacks against Ukrainian government organizations. These latest attacks employ a meticulously crafted infection chain, making them exceptionally difficult to detect.
The group, active since at least 2016, has a long history of targeting countries neighboring Belarus, and its latest campaign shows just how far it has evolved.
The new activity, detected starting in March 2026, blends deceptive documents, layered malware scripts, and server-side victim filtering into a single coordinated operation.
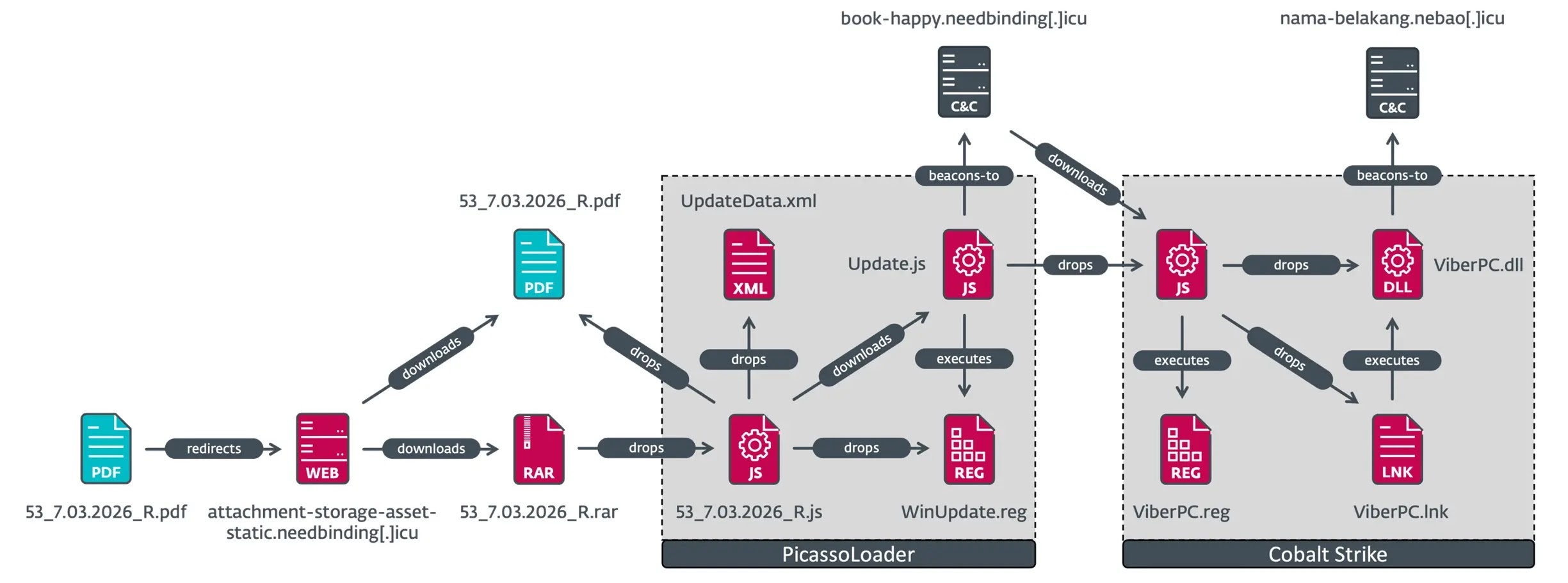
The attacks begin with spearphishing emails carrying malicious PDF files designed to look like legitimate government communications.
One lure document impersonated Ukrtelecom, a Ukrainian telecommunications company, and appeared to offer assurances about customer data protection.
When a recipient clicks the download button inside the PDF, they are directed to a server fully controlled by the attackers. What they receive next depends entirely on where they are connecting from.
ESET’s official threat research blog, WeLiveSecurity’s analysts identified and said in a report shared with Cyber Security News (CSN) that FrostyNeighbor, also tracked as Ghostwriter, UNC1151, TA445, PUSHCHA, and Storm-0257, is a long-running cyber espionage actor apparently aligned with the interests of Belarus.
ESET researchers noted that the group regularly updates its tools and methods specifically to avoid triggering security alerts.
FrostyNeighbor’s campaigns have historically focused on Ukraine, Poland, and Lithuania, with victims ranging from government and military bodies to industrial firms and healthcare organizations.
In its newest campaign, the group demonstrates both patience and precision, delivering the final payload only after manually confirming that a target is worth pursuing.
This selective approach makes the operation especially difficult to detect or replicate in a controlled environment.
The group has been under active surveillance for years, with past reports from CERT-UA, SentinelOne, HarfangLab, and StrikeReady all documenting its evolving tactics.
The latest findings reveal a newer delivery mechanism using JavaScript to stage the attack across multiple steps, pulling in tools cleverly disguised as ordinary image or web files.
Hackers Abuse Scheduled Tasks
Once a victim from Ukraine clicks the embedded link in the lure document, the attacker’s server delivers a RAR archive named 53_7.03.2026_R.rar.
Inside is a JavaScript file that drops a decoy PDF to keep the target occupied while quietly launching the next stage in the background.
This second-stage script, called PicassoLoader, is a downloader the group has used across multiple campaigns and in several different programming languages.
To lock in its presence on the victim’s machine, PicassoLoader downloads a scheduled task template from the command-and-control server, disguised as a JPEG image file.
The server actually delivers an XML configuration file, and the script fills in real execution parameters before registering the scheduled task on the system.
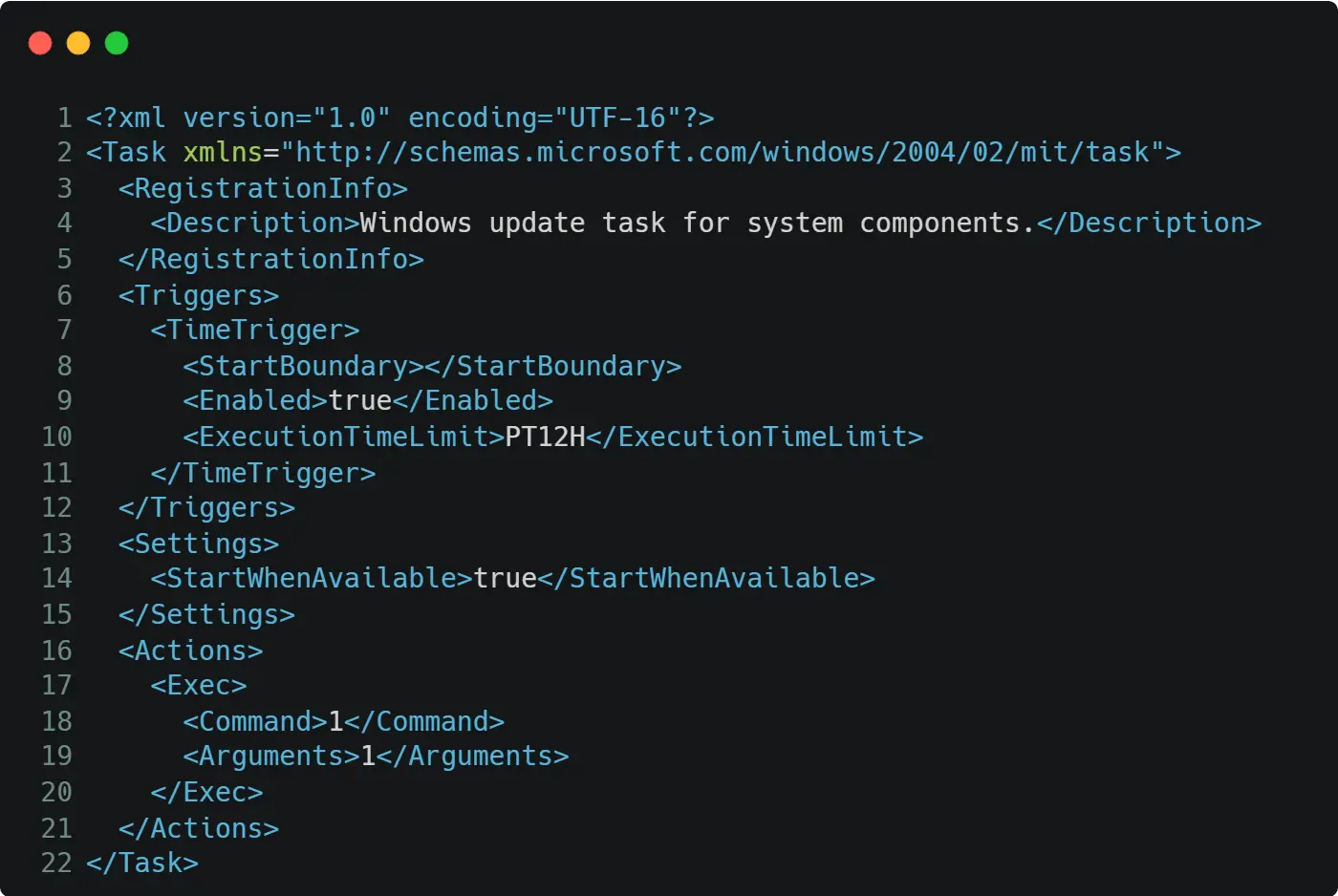
This ensures PicassoLoader runs automatically at every Windows startup, which is exactly how FrostyNeighbor maintains persistent access on compromised machines.
Cobalt Strike Deployed After Victim Validation
What makes this attack chain particularly sharp is the server-side validation step that occurs before any serious payload is delivered.
Every ten minutes, PicassoLoader sends a system fingerprint, including the username, computer name, operating system version, and list of running processes, to the command-and-control server.
A human operator then reviews this information and decides whether the target is worth the next move.
If the victim qualifies, the server responds with a third-stage JavaScript dropper. This script copies the legitimate Windows file rundll32.exe under a different name, likely to bypass security tools that flag unfamiliar executables.
A Cobalt Strike beacon is then written to disk, and a registry entry ensures it launches automatically on every startup, giving the attackers full and persistent remote control over the compromised machine.
Security researchers recommend continuous and close monitoring of the group’s infrastructure, toolset changes, and operational patterns as the most effective defense against future campaigns.
Organizations across Eastern Europe, especially those in government, defense, and critical sectors, should treat any unsolicited PDF attachment as a potential threat and remain on high alert.
Indicators of Compromise (IoCs):-
| Type | Indicator | Description |
|---|---|---|
| SHA-1 | 776A43E46C36A539C916ED426745EE96E2392B39 | 53_7.03.2026_R.rar — JS/TrojanDropper.FrostyNeighbor |
| SHA-1 | 8D1F2A6DF51C7783F2EAF1A0FC0FF8D032E5B57F | 53_7.03.2026_R.js — JS/TrojanDropper.FrostyNeighbor |
| SHA-1 | B65551D339AECE718EA1465BF3542C794C445EFC | Update.js — JS/TrojanDownloader.FrostyNeighbor |
| SHA-1 | E15ABEE1CFDE8BE7D87C7C0B510450BAD6BC0906 | Update.js — JS/TrojanDropper.FrostyNeighbor |
| SHA-1 | 43E30BE82D82B24A6496F6943ECB6877E83F88AB | ViberPC.dll — Win32/CobaltStrike.Beacon |
| SHA-1 | 4F2C1856325372B9B7769D00141DBC1A23BDDD14 | 53_7.03.2026_R.pdf — PDF/TrojanDownloader.FrostyNeighbor |
| SHA-1 | D89E5524E49199B1C3B66C524E7A63C3F0A0C199 | Certificate.pdf — PDF/TrojanDownloader.FrostyNeighbor |
| SHA-1 | 7E537D8E91668580A482BD77A5A4CABA26D6BDAC | certificate.js — JS/TrojanDownloader.FrostyNeighbor |
| SHA-1 | FA6882672AD3654800987613310D7C3FBADE027E | certificate.js — JS/TrojanDownloader.FrostyNeighbor |
| SHA-1 | 3FA7D1B13542F1A9EB054111F9B69C250AF68643 | СетифікатCAF.rar — JS/TrojanDropper.FrostyNeighbor |
| SHA-1 | 4E52C92709A918383E90534052AAA257ACE2780C | СетифікатCAF.js — JS/TrojanDropper.FrostyNeighbor |
| SHA-1 | 6FDED427A16D5314BA3E1EB9AFD120DC84449769 | EdgeTaskMachine.js — JS/TrojanDropper.FrostyNeighbor |
| SHA-1 | 27FA11F6A1D653779974B6FB54DE4AF47F211232 | EdgeSystemConfig.dll — Win32/CobaltStrike.Beacon |
| Domain | attachment-storage-asset-static.needbinding[.]icu | C&C server — PicassoLoader delivery |
| Domain | book-happy.needbinding[.]icu | C&C server — scheduled task template and fingerprint collection |
| Domain | nama-belakang.nebao[.]icu | C&C server — Cobalt Strike beacon C&C |
| Domain | easiestnewsfromourpointofview.algsat[.]icu | C&C infrastructure |
| Domain | mickeymousegamesdealer.al[.]icu | C&C infrastructure |
| Domain | exavegas[.]icu | C&C infrastructure |
| Domain | hinesafar.sardk[.]icu | C&C infrastructure |
| Domain | shinesafar.sardk[.]icu | C&C infrastructure |
| Domain | best-seller.lavanille[.]buzz | C&C infrastructure |
| URL | https://book-happy.needbinding[.]icu/wp-content/uploads/2023/10/1GreenAM.jpg | Scheduled task template delivery URL |
| URL | https://book-happy.needbinding[.]icu/employment/documents-and-resources | PicassoLoader fingerprint POST endpoint |
| URL | https://nama-belakang.nebao[.]icu/statistics/discover.txt | Cobalt Strike beacon C&C endpoint |
| Filename | 53_7.03.2026_R.rar | First-stage RAR archive lure |
| Filename | 53_7.03.2026_R.js | First-stage JavaScript dropper |
| Filename | 53_7.03.2026_R.pdf | Decoy PDF lure document |
| Filename | Update.js | PicassoLoader second-stage downloader |
| Filename | WinUpdate.reg | Registry file dropped by first-stage script |
| Filename | ViberPC.exe | Renamed copy of rundll32.exe |
| Filename | ViberPC.dll | Cobalt Strike beacon payload |
| Filename | ViberPC.reg | Registry file for Cobalt Strike persistence |
| Filename | ViberPC.lnk | Shortcut file for Cobalt Strike execution |
| Filename | EdgeTaskMachine.js | Additional FrostyNeighbor dropper |
| Filename | EdgeSystemConfig.dll | Additional Cobalt Strike beacon |
Note: IP addresses and domains are intentionally defanged (e.g., [.]) to prevent accidental resolution or hyperlinking. Re-fang only within controlled threat intelligence platforms such as MISP, VirusTotal, or your SIEM.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.