METATRON: Open-Source AI Pen Testing Assistant Penetration Brings
METATRON, a new open-source penetration testing framework, is drawing significant interest from security researchers due to its fully offline, AI-driven approach to vulnerability assessment. Built...
METATRON, a new open-source penetration testing framework, is drawing significant interest from security researchers due to its fully offline, AI-driven approach to vulnerability assessment.
Built for Parrot OS and other Debian-based Linux distributions, METATRON combines automated reconnaissance tooling with a locally hosted large language model (LLM), eliminating the need for cloud connectivity, API keys, or third-party subscriptions.
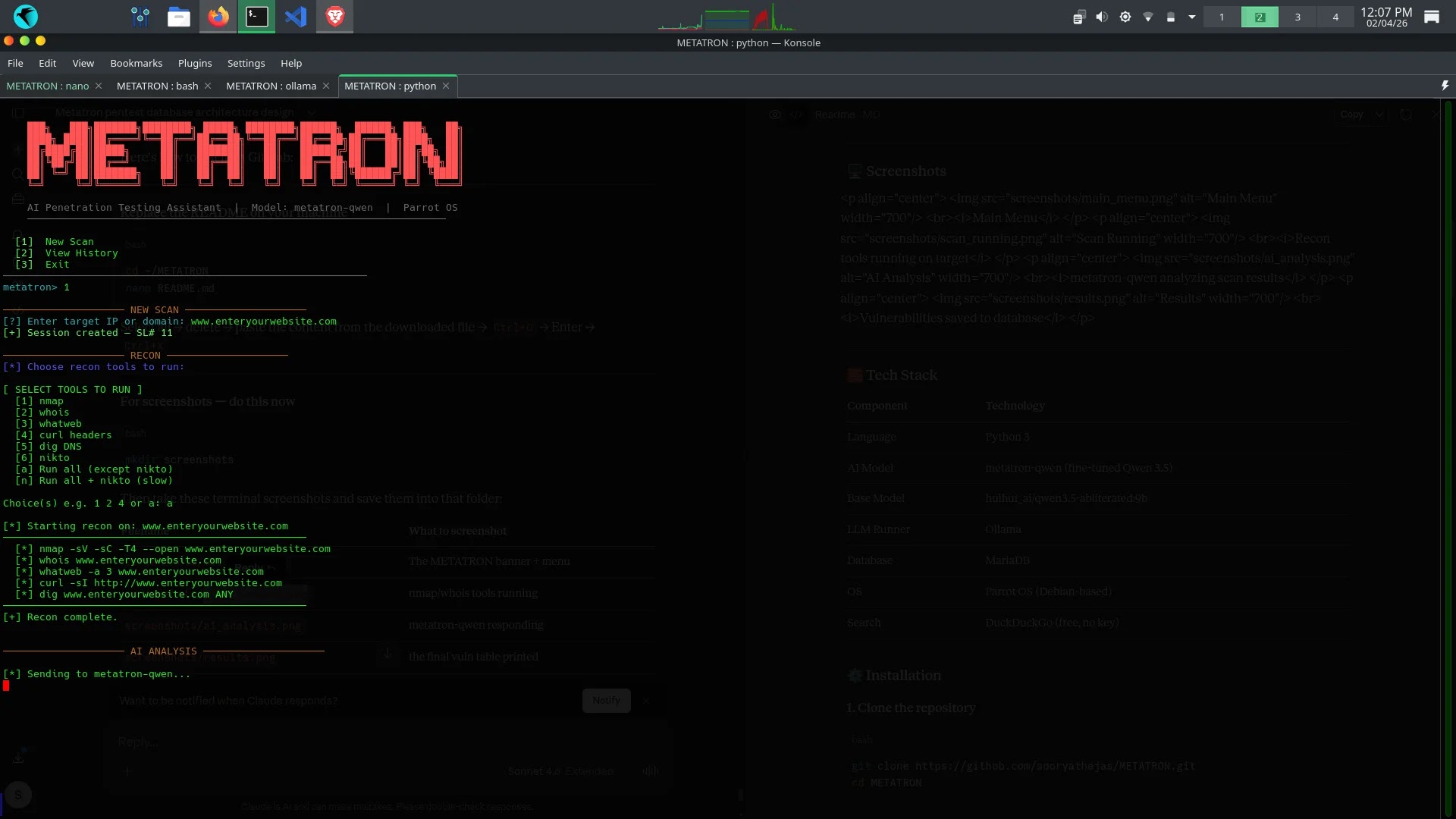
METATRON is a CLI-based penetration testing assistant written in Python 3 that accepts a target IP address or domain and autonomously orchestrates a suite of standard reconnaissance tools.
These include nmap for port scanning, nikto for web server vulnerability detection, whois and dig for DNS and registration data, whatweb for technology fingerprinting, and curl for HTTP header inspection.
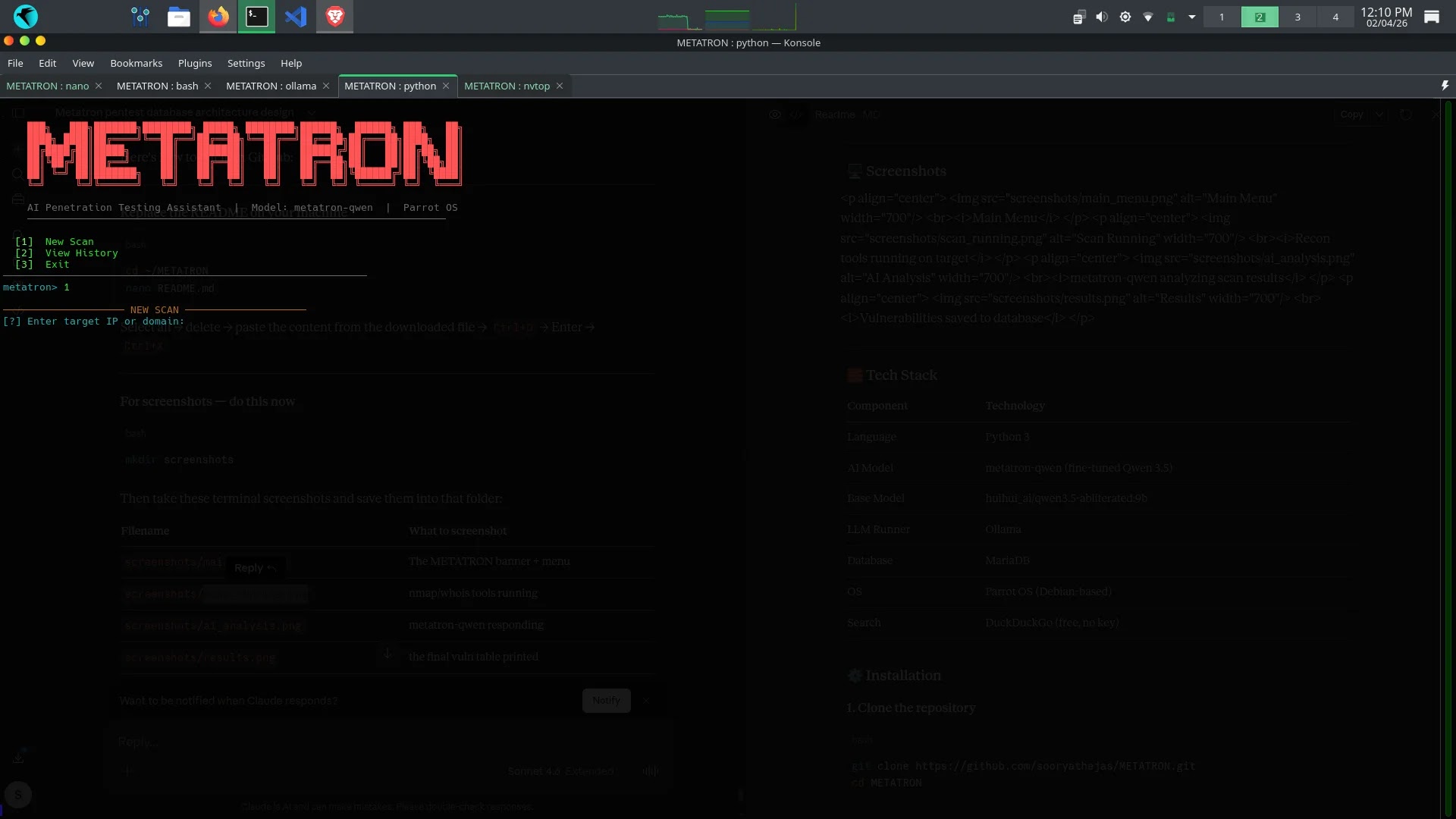
Once recon data is collected, all results are piped directly into a locally running AI model — metatron-qwen — a fine-tuned variant of the huihui_ai/qwen3.5-abliterated:9b base model, customized specifically for penetration testing analysis.
The model is served via Ollama, a local LLM runner, and is configured with a 16,384-token context window, a temperature of 0.7, top-k of 10, and top-p of 0.9 — parameters optimized for precise, technically grounded security analysis rather than creative generation.
Agentic Loop and CVE Integration
One of METATRON’s more technically notable features is its agentic loop: the AI model can autonomously request additional tool executions mid-analysis if it determines more data is needed before rendering a verdict. This enables a dynamic, iterative assessment workflow rather than a single static scan pass.
The framework also integrates DuckDuckGo-based web search and CVE lookups without requiring any API credentials, allowing the model to cross-reference discovered services and versions against known public vulnerability databases in real time.
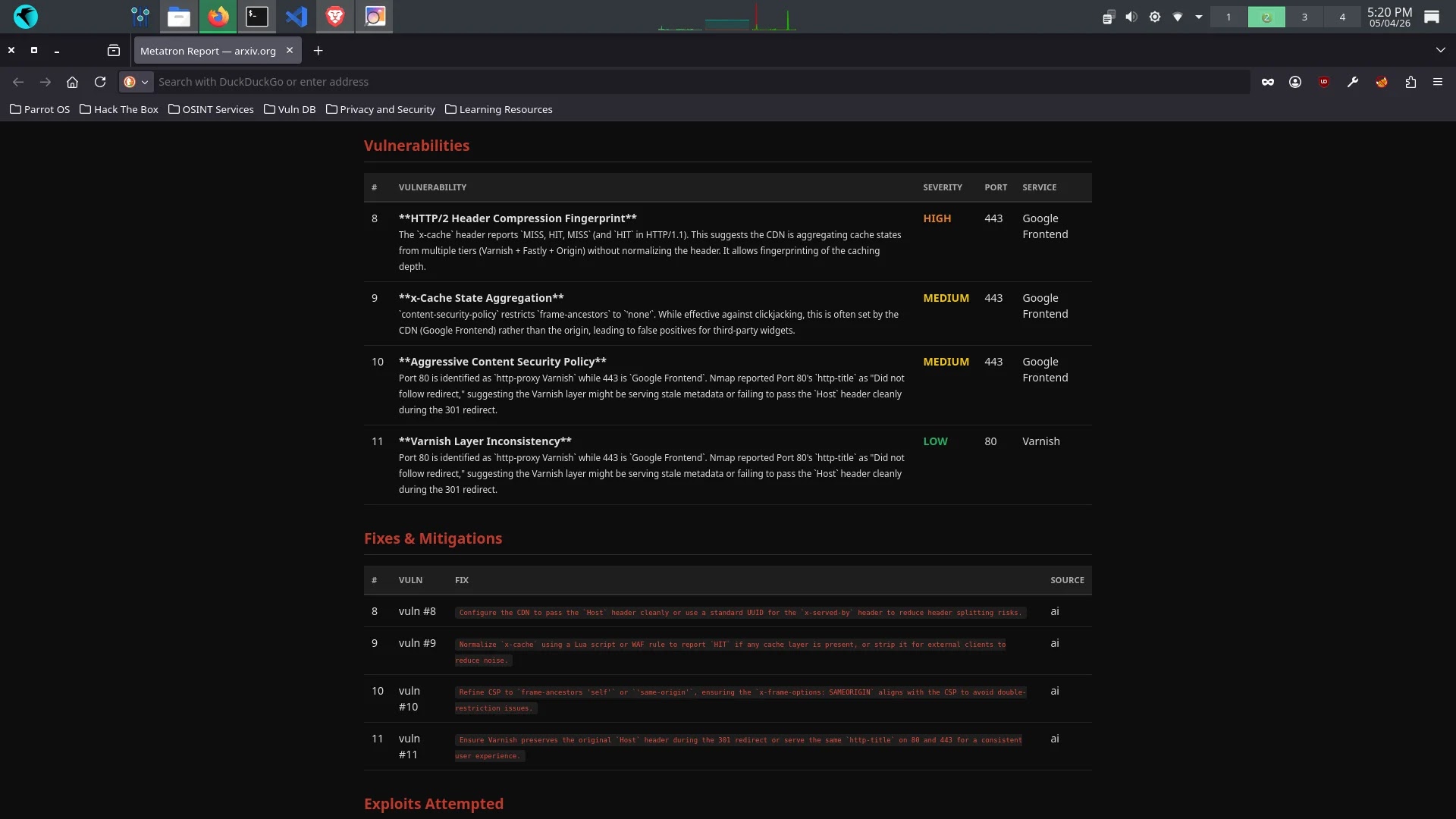
METATRON uses a five-table MariaDB schema to persist all scan data, structured around a central history table keyed by session number (sl_no). Linked tables store discovered vulnerabilities with severity ratings, recommended fixes sourced from AI analysis, attempted exploits with payloads and results, and a full summary table containing raw scan output alongside the complete AI analysis dump and overall risk level.
Users can edit or delete any saved record directly from the CLI, and export reports in PDF or HTML format for documentation or client delivery — a critical feature for professional penetration testers who need audit trails.
The project’s most significant differentiator in the current AI tooling landscape is its zero-exfiltration guarantee. All LLM inference happens on-device through Ollama, meaning sensitive target data, including internal IP ranges, banner information, and discovered vulnerabilities, never leaves the tester’s machine. This positions METATRON as a viable option for engagements with strict data handling requirements.
METATRON is available on GitHub under the MIT License at github.com/sooryathejas/METATRON, with minimum hardware requirements of 8.4 GB RAM for the 9b model variant.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.