ResokerRAT Controls Infected Windows via Telegram Bot API
A newly identified Remote Access Trojan (RAT), dubbed ResokerRAT, targets Windows systems. It leverages Telegram’s widely adopted Bot API to establish command-and-control (C2) and exfiltrate...
A newly identified Remote Access Trojan (RAT), dubbed ResokerRAT, targets Windows systems. It leverages Telegram’s widely adopted Bot API to establish command-and-control (C2) and exfiltrate stolen data back to its operators.
Unlike traditional malware that relies on custom command-and-control servers, this threat routes all communications through a trusted messaging platform, making it far harder for security tools to detect and block.
The approach gives attackers a well-disguised line of communication that blends into everyday web traffic.
ResokerRAT carries a wide range of harmful capabilities, including screen capture, keylogging, privilege escalation, Task Manager blocking, and downloading additional malicious payloads onto the infected machine.
Once installed, the malware operates silently in the background, communicating through an encrypted HTTPS connection to Telegram’s API without showing any visible signs to the victim.
Since the connections to Telegram are generally trusted by corporate firewalls and network monitoring filters, this method of delivering commands is particularly effective at staying hidden for extended periods.
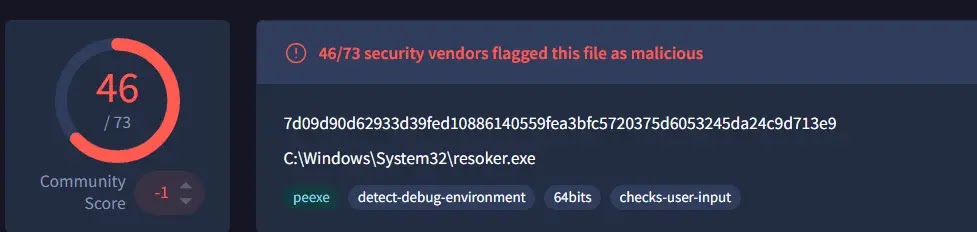
Analysts at K7 Security Labs identified and documented this malware, with researcher Priyadharshini publishing a detailed technical report on March 30, 2026.
Their investigation found that the malware executable, Resoker.exe, begins its attack chain immediately upon execution, running a series of pre-checks and evasion routines before making contact with the attacker’s Telegram bot.
The team noted that the malware combines Windows API calls with hidden PowerShell commands to carry out its tasks without drawing the user’s attention.
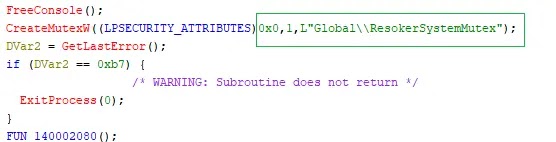
Once running, Resoker.exe creates a mutex named “GlobalResokerSystemMutex” to ensure only one instance of the malware runs at a time.
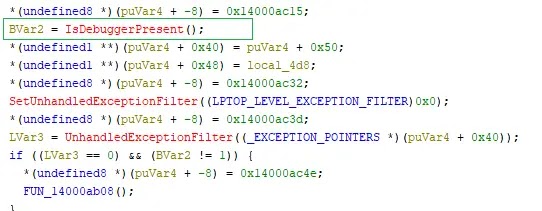
It then uses the IsDebuggerPresent API to check whether a debugger or analysis tool is currently attached, and if one is found, it triggers custom exception handling to disrupt the inspection.
The malware also attempts to restart itself with administrator rights using ShellExecuteExA with the “runas” option (Figure 4: Administrator Privilege Request), giving it complete control over the infected system.
To keep security researchers at bay, the malware actively scans running processes and terminates well-known analysis tools such as Taskmgr.exe, Procexp.exe, and ProcessHacker.exe.
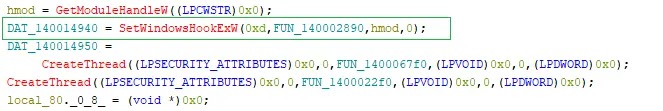
It also installs a global keyboard hook via SetWindowsHookExW, blocking common keyboard shortcuts such as ALT+TAB and CTRL+ALT+DEL, effectively trapping the user inside the infected session and preventing normal system interaction.
Command-and-Control via Telegram
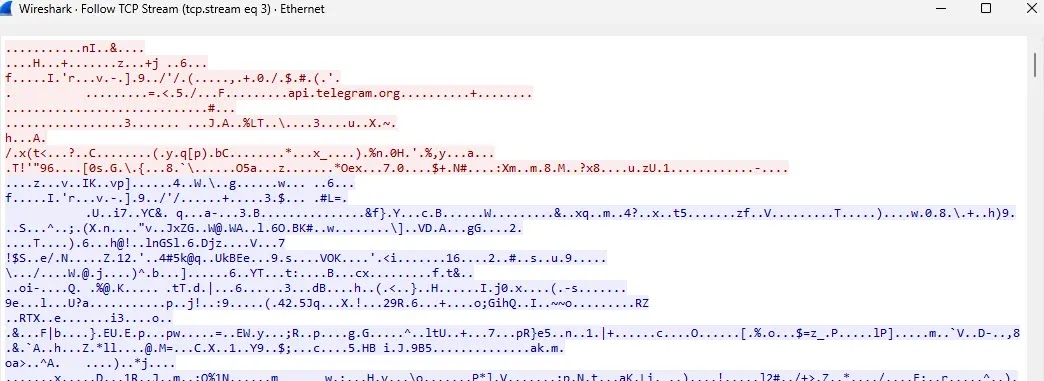
The most distinctive element of ResokerRAT is its use of the Telegram Bot API as a full command-and-control channel.
The malware constructs a URL with a hardcoded bot token and chat ID, then polls Telegram’s getUpdates endpoint for new instructions.
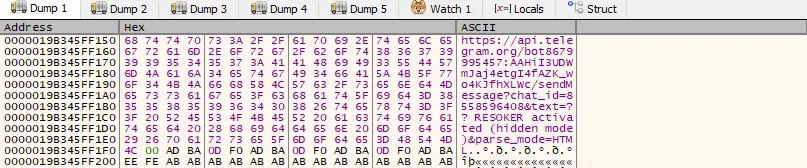
This traffic is nearly indistinguishable from regular Telegram use, as confirmed by network capture analysis.
From this channel, attackers can issue a range of commands. The /screenshot command runs a hidden PowerShell script to silently capture the screen and save it as a PNG file. The /startup command drops the malware’s path into the Windows Run registry key, ensuring it survives reboots.
The /download command fetches additional files from attacker-controlled URLs via a hidden PowerShell process.
The /uac-min command quietly weakens User Account Control by setting ConsentPromptBehaviorAdmin to 0, removing security prompts without the user’s knowledge.
All transmitted data is URL-encoded before delivery, and the malware keeps a local log of its own activity.
Users and organizations should avoid downloading executables from untrusted links or unknown sources. Keeping Windows and all security software up to date is critical, as patches help close the gaps that malware exploits.
Network administrators should monitor outbound connections to Telegram API endpoints for unusual or unexpected patterns.
Restricting PowerShell execution policies and enabling endpoint detection tools can help identify and stop this type of threat before it causes serious damage.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.