Magecart Attack Skims Payment Data Using Malicious
A new Magecart-style campaign has emerged, targeting online shoppers through malicious JavaScript code designed to steal payment information directly from ecommerce websites. The attack works by...
A new Magecart-style campaign has emerged, targeting online shoppers through malicious JavaScript code designed to steal payment information directly from ecommerce websites.
The attack works by injecting hidden scripts into compromised shopping sites, allowing attackers to intercept sensitive data when customers enter their credit card details during checkout.
Magecart attacks represent a significant threat to online retailers and their customers. These campaigns have evolved over several years, with cybercriminals continuously refining their methods to avoid detection.
The latest variant demonstrates sophisticated obfuscation techniques, making it harder for security teams to identify and block the malicious code before it damages customer trust and business operations.
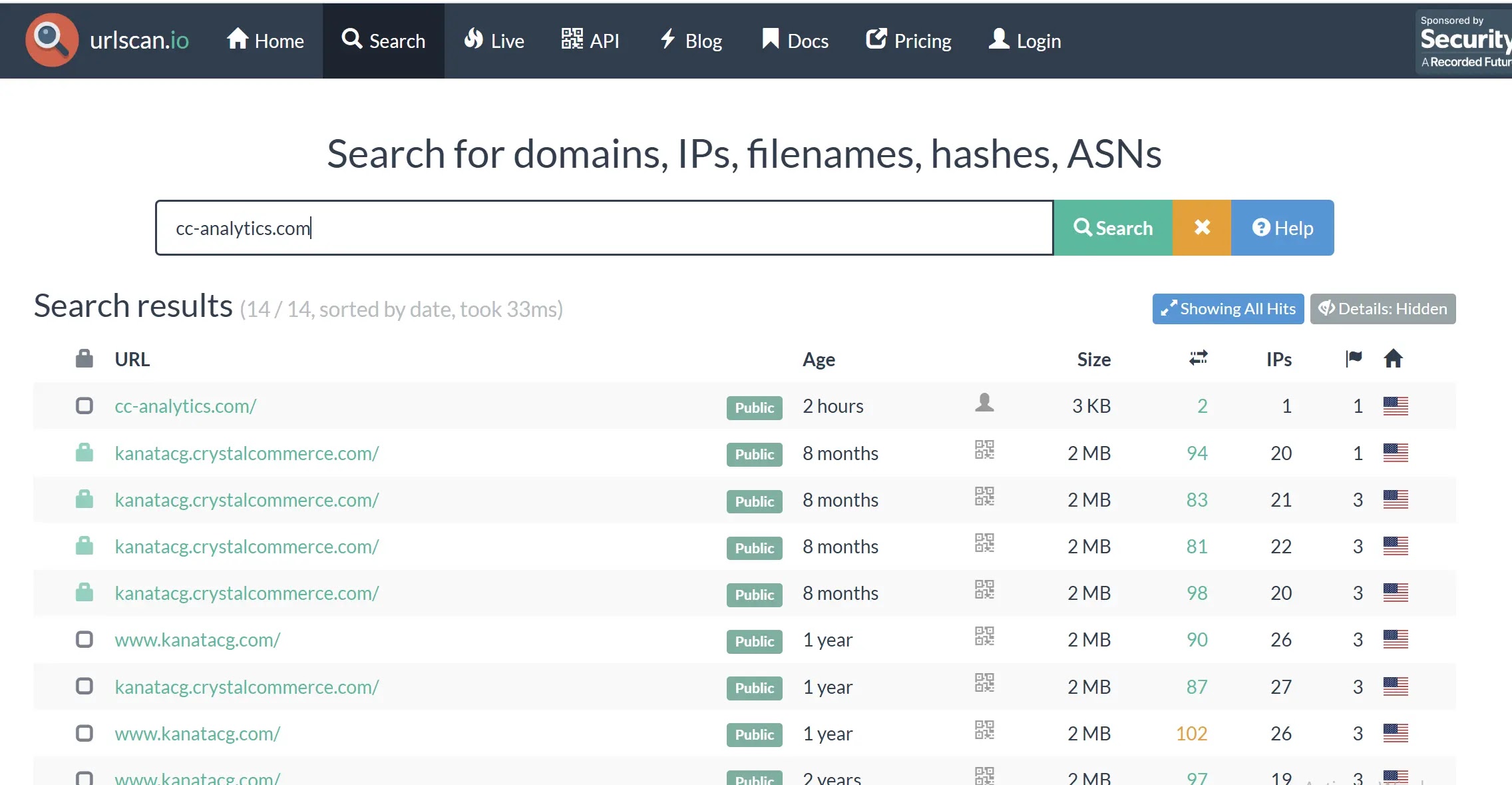
Security analyst Himanshu Anand identified this particular campaign through open-source threat intelligence. He traced the attack back to a primary domain, cc-analytics.com, which was hosting the malicious JavaScript file.
The discovery revealed a coordinated effort by threat actors to deploy similar payloads across multiple ecommerce platforms, suggesting a widespread campaign affecting numerous online businesses and their customers.
The stolen data gets sent to attacker-controlled servers where criminals harvest the payment information for resale or fraudulent use.
This campaign shows how attackers exploit trusted ecommerce environments to target customers at their most vulnerable moment—when making an online purchase.
How the Attack Infection Mechanism Works?
The malicious JavaScript operates through a multi-stage process that remains hidden from customers and website administrators.
When an unsuspecting shopper visits a compromised ecommerce site, the attacker’s code quietly loads in the background through a simple script tag injected into the webpage’s HTML code.
Once active, the script targets specific form fields where customers enter sensitive information. It hooks into checkout buttons and payment form elements, monitoring user activity for signs of payment data entry.
When a customer types their credit card number and billing address, the JavaScript captures this information in real-time before the legitimate payment gateway even receives it.
The theft happens instantly through an automated data exfiltration function. The captured payment details get bundled into a request and sent to attacker infrastructure, specifically to domains like pstatics.com.
By the time a customer completes their purchase, their credit card information has already been harvested and sent to the criminals behind the campaign.
What makes this attack particularly dangerous is its invisibility. The JavaScript runs silently without triggering browser security warnings or leaving obvious signs of compromise.
The obfuscation techniques used render the code unreadable to automated security tools, enabling it to persist on compromised websites for extended periods while continuously stealing data from unsuspecting customers.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.