LastPass Warns: Fake Maintenance Message Steals Tracking Users
LastPass has issued a critical security alert regarding an active phishing campaign that began on January 19, 2026. Threat actors are impersonating LastPass support staff, sending fraudulent emails...
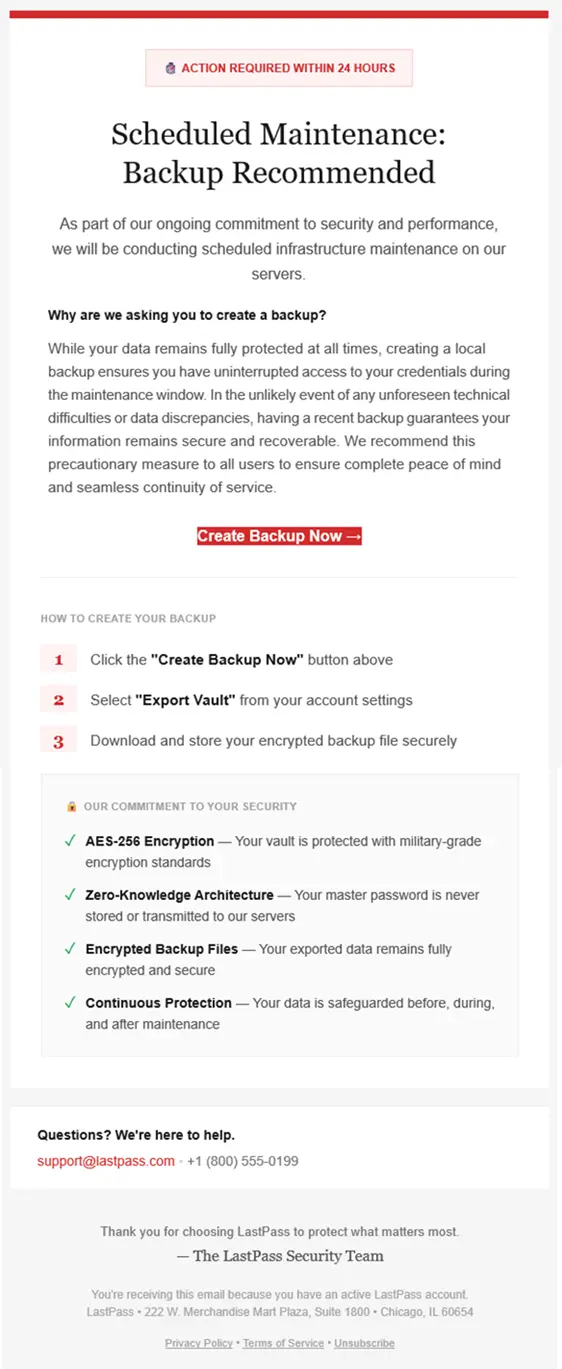
LastPass has issued a critical security alert regarding an active phishing campaign that began on January 19, 2026. Threat actors are impersonating LastPass support staff, sending fraudulent emails that claim urgent vault backup requirements. Their objective is to harvest master passwords from unsuspecting users.
The phishing emails employ social engineering tactics by creating artificial urgency, falsely claiming that LastPass maintenance requires customers to back up their vaults within 24 hours.
LastPass explicitly confirms it never requests customer master passwords or demands immediate vault backups via email.
The campaign strategically launched over the U.S. holiday weekend, a deliberate timing choice designed to exploit reduced security staffing and delayed incident response.
Threat actors commonly exploit such windows to maximize the success rate of compromise before detection.
The phishing infrastructure consists of two primary components: an initial redirect hosted on compromised AWS S3 infrastructure and a spoofed domain designed to mimic legitimate LastPass services.
Users should immediately delete any emails claiming to require LastPass maintenance.
LastPass confirms that Legitimate communications never request master passwords, vault backups, or urgent action via unsolicited emails.
Organizations should implement email security controls to block messages from the identified sender addresses and educate staff on phishing indicators, including artificially urgent language and requests for sensitive credentials.
LastPass is coordinating with third-party partners to take down the malicious infrastructure. Users who received these emails are encouraged to report them directly to [email protected] for analysis and tracking.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.