Luxshare Hit by Ransomware: Apple Manufacturer’s Data
A major electronics manufacturer has reportedly suffered a ransomware attack, leading to the exposure of confidential internal documents. The breach compromises the company’s critical role in Apple’s...
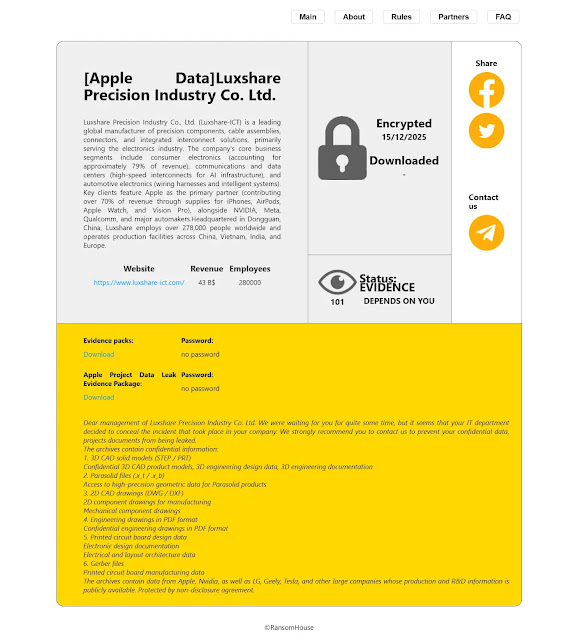
A major electronics manufacturer has reportedly suffered a ransomware attack, leading to the exposure of confidential internal documents.
The breach compromises the company’s critical role in Apple’s global supply chain, including AirPods manufacturing, iPhone production, and Vision Pro assembly.
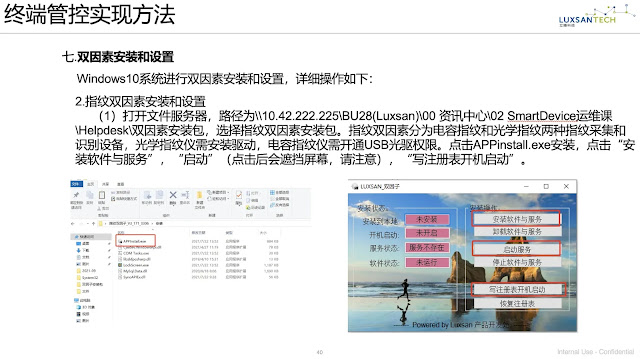
Threat actors have published internal documents revealing sensitive operational intelligence, including production workflows, security procedures, and supply chain protocols.
Luxshare manufactures approximately 30% of iPhone units and serves as the exclusive supplier for Apple’s Vision Pro headsets.
The company also maintains deep integration within Apple’s parts and repair supply chain, elevating the breach’s strategic significance.
The exposed data represents operational blueprints that could enable competitors or threat actors to understand production vulnerabilities, manufacturing capabilities, and security gaps embedded within Apple’s supplier ecosystem.
Security researchers are tracking the incident to identify the responsible threat group. Initial analysis suggests involvement of a sophisticated threat actor with capabilities to target large-scale electronics manufacturers.
The public disclosure of confidential documents follows typical ransomware extortion playbooks, combining encryption with data theft to maximize pressure to pay ransom.
Apple’s supply chain faces elevated risk exposure. Luxshare’s manufacturing responsibilities for signature products (AirPods, iPhones, Vision Pro) mean production delays could significantly impact revenue and market positioning.
The breach also raises questions about vendor security requirements and oversight within Apple’s supplier vetting process.
Regulatory bodies may investigate whether Apple maintained adequate security standards for critical supplier relationships.
GDPR, SEC disclosure requirements, and export control regulations could trigger compliance obligations.
Luxshare should conduct an immediate forensic investigation to determine the scope, timeline, and classification of the compromised data.
Apple must evaluate supply chain contingencies and accelerate alternative manufacturing partnerships.
Both entities should engage law enforcement and cybersecurity agencies to identify threat actors and provide guidance on potential ransom negotiations.
The incident underscores critical vulnerabilities in high-tech supply chains and the need for enhanced security maturity among tier-one manufacturers.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.