LockBit 5.0: New Affiliate Panel & Researchers Uncovered
Despite facing serious law enforcement actions, LockBit, one of the world’s most dangerous ransomware groups, has released its newest version. The group’s operations continue moving forward,...
Despite facing serious law enforcement actions, LockBit, one of the world’s most dangerous ransomware groups, has released its newest version.
The group’s operations continue moving forward, displaying fresh variants that target different computer systems and platforms.
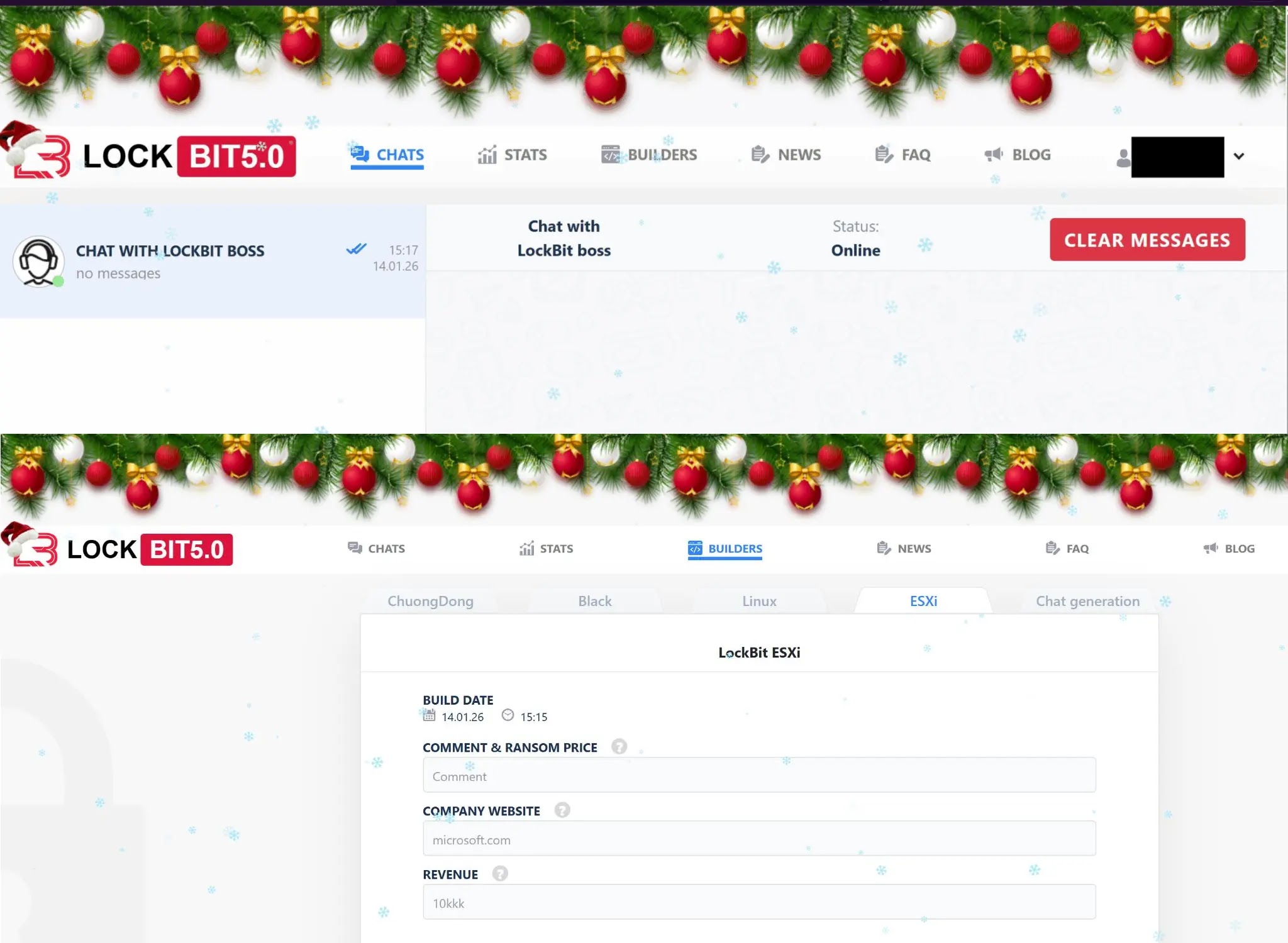
Recently, leaked materials and screenshots have provided security experts with a detailed look at how this criminal operation manages its attacks and coordinates with affiliates who help spread the malware across networks.
The latest version of LockBit remains largely unchanged in its core design and functionality following Operation Cronos, a significant disruption effort by law enforcement agencies.
However, security researchers have noticed minor cosmetic changes to the interface, including holiday-themed decorations that suggest the group continues operating without concern.
The group maintains a sophisticated infrastructure that allows them to manage victim negotiations and coordinate attacks across different sectors and industries worldwide.
Flare analysts identified that LockBit’s affiliate program continues recruiting new partners despite the group’s damaged reputation.
Many cybercriminals no longer want to work with the group, yet the organization proceeds as if law enforcement actions never happened.
This resilience demonstrates how quickly criminal operations can adapt and maintain their business model even after significant disruptions.
The group’s ability to recover quickly shows the ongoing challenge security teams face when combating organized ransomware operations.
LockBit 5.0’s Multi-Platform Attack Strategy
The most concerning aspect of LockBit 5.0 involves its expanded target scope across multiple operating systems and virtualization environments.
Recent malware samples obtained by security researchers reveal four distinct variants that were discovered on January fourteenth, two thousand twenty-six.
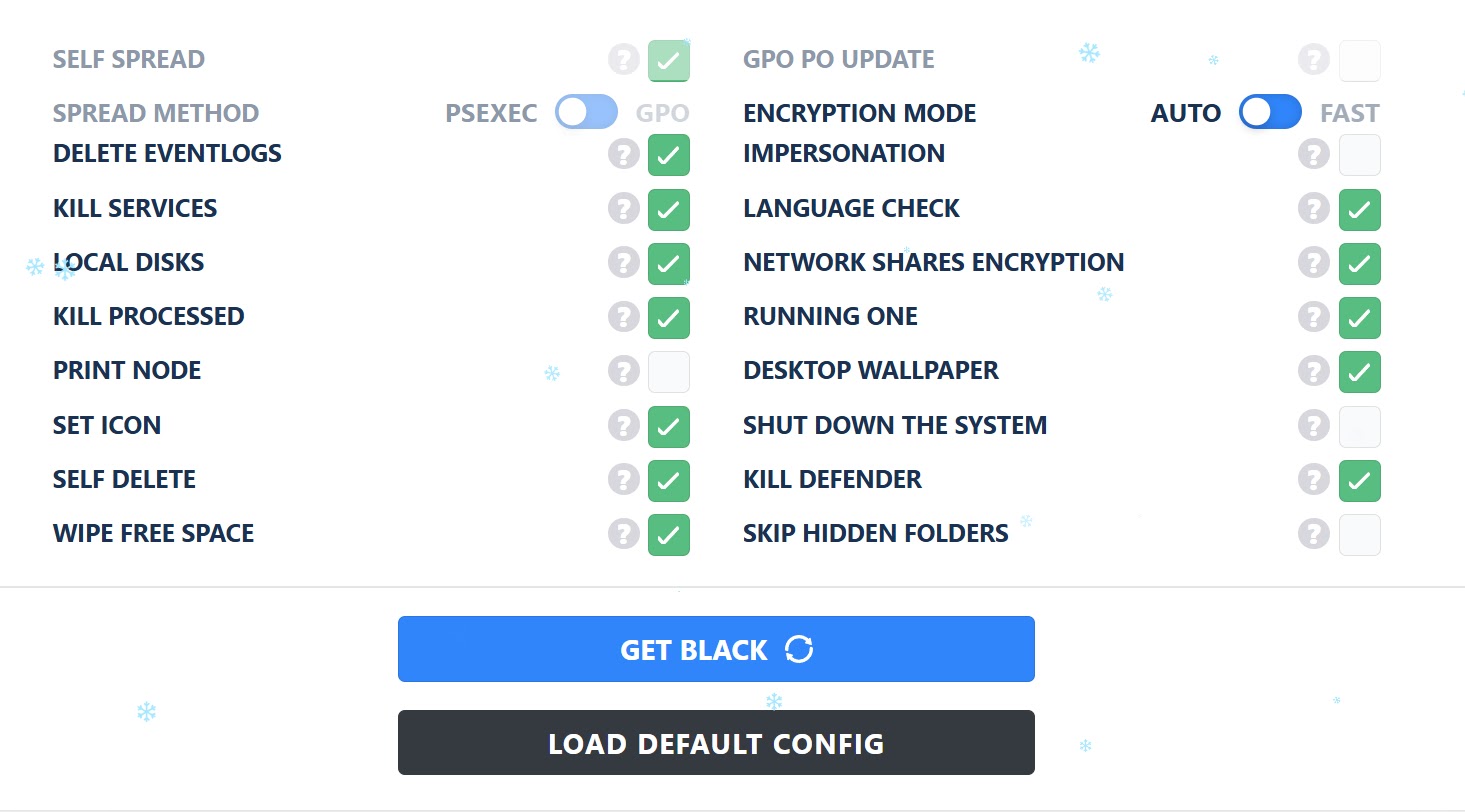
These include LB_Black designed for standard Windows systems, LB_Linux for Linux environments, LB_ESXi for virtual infrastructure, and LB_ChuongDong representing another variant.
This diversification represents a strategic shift toward enterprise environments where virtual machines and cloud infrastructure are common targets.
The availability of these updated samples provides security teams with current indicators of compromise needed for defensive measures.
Organizations can now use these technical details to identify if their networks have encountered LockBit 5.0. Understanding these variants helps cybersecurity professionals develop better detection rules and prevention strategies.
The leaked affiliate panel materials show exactly how the group manages payments, establishes rules for partners, and processes new recruits into their operation, offering unprecedented insights into ransomware-as-a-service business practices.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.