VoidLink: First AI-Driven Malware Threat Framework Emer
The cybersecurity landscape faces a dangerous new chapter: the discovery of VoidLink, the first documented advanced malware framework built almost entirely by artificial intelligence. Unlike earlier...
The cybersecurity landscape faces a dangerous new chapter: the discovery of VoidLink, the first documented advanced malware framework built almost entirely by artificial intelligence.
Unlike earlier attempts where inexperienced hackers used AI to create basic malicious tools, VoidLink represents a turning point where sophisticated threat actors can now use AI to develop complex attack systems at unprecedented speed.
Security professionals have long worried about AI becoming a weapon in the hands of cybercriminals. That theoretical concern became reality when Check Point researchers discovered VoidLink during routine monitoring activities.
The malware stood out immediately due to its mature architecture, efficient design, and advanced technical features.
What initially appeared to be the work of a well-funded team turned out to be the creation of likely a single developer using AI assistance, reaching a functional version in under one week.
Check Point analysts identified the malware after tracking its command-and-control infrastructure and discovering critical security mistakes made by its developer.
These operational security failures exposed the entire development process, revealing planning documents, source code, and internal communications.
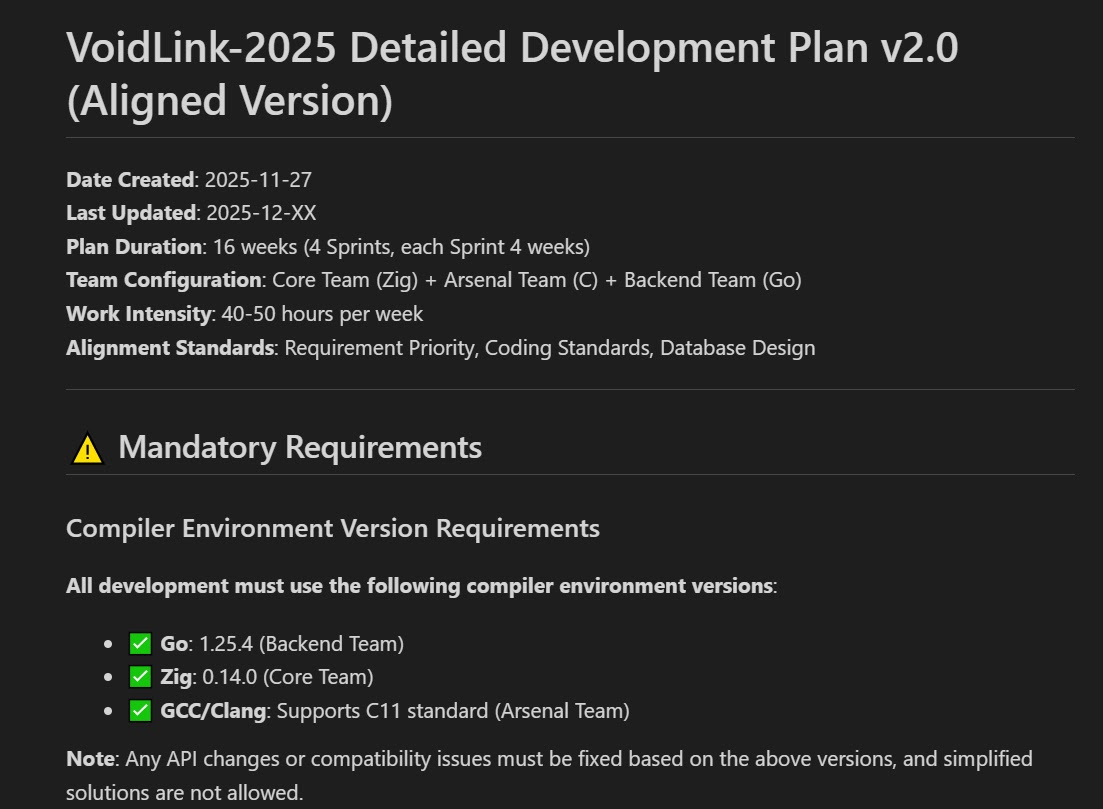
The leaked materials showed that an AI model called TRAE SOLO generated detailed project plans spanning 30 weeks across three simulated development teams, complete with sprint schedules and coding standards.
The discovery has alarming implications for the cybersecurity industry. VoidLink demonstrates that a single person with the right skills can now produce malware that previously required coordinated teams of experienced programmers.
The framework employs advanced techniques like eBPF and LKM rootkits for hiding its presence on infected systems, along with specialized modules designed to target cloud environments and container platforms.
What makes VoidLink particularly concerning is its development methodology. The creator used an approach called Spec Driven Development, where the AI first generated a comprehensive blueprint with technical specifications, then wrote the actual malicious code according to those plans.
By late November 2025, the developer had instructed the AI to design the framework, and by early December, VoidLink had grown to over 88,000 lines of functional code.
AI-Powered Development Process
The VoidLink creation process reveals how AI transforms malware development from a team effort into a one-person operation. The developer began by providing the TRAE AI assistant with basic requirements and a minimal code skeleton.
The AI then decomposed these requirements into detailed architecture plans, assigned tasks across three fictional teams working in different programming languages, and generated strict coding guidelines that the final malware would follow.
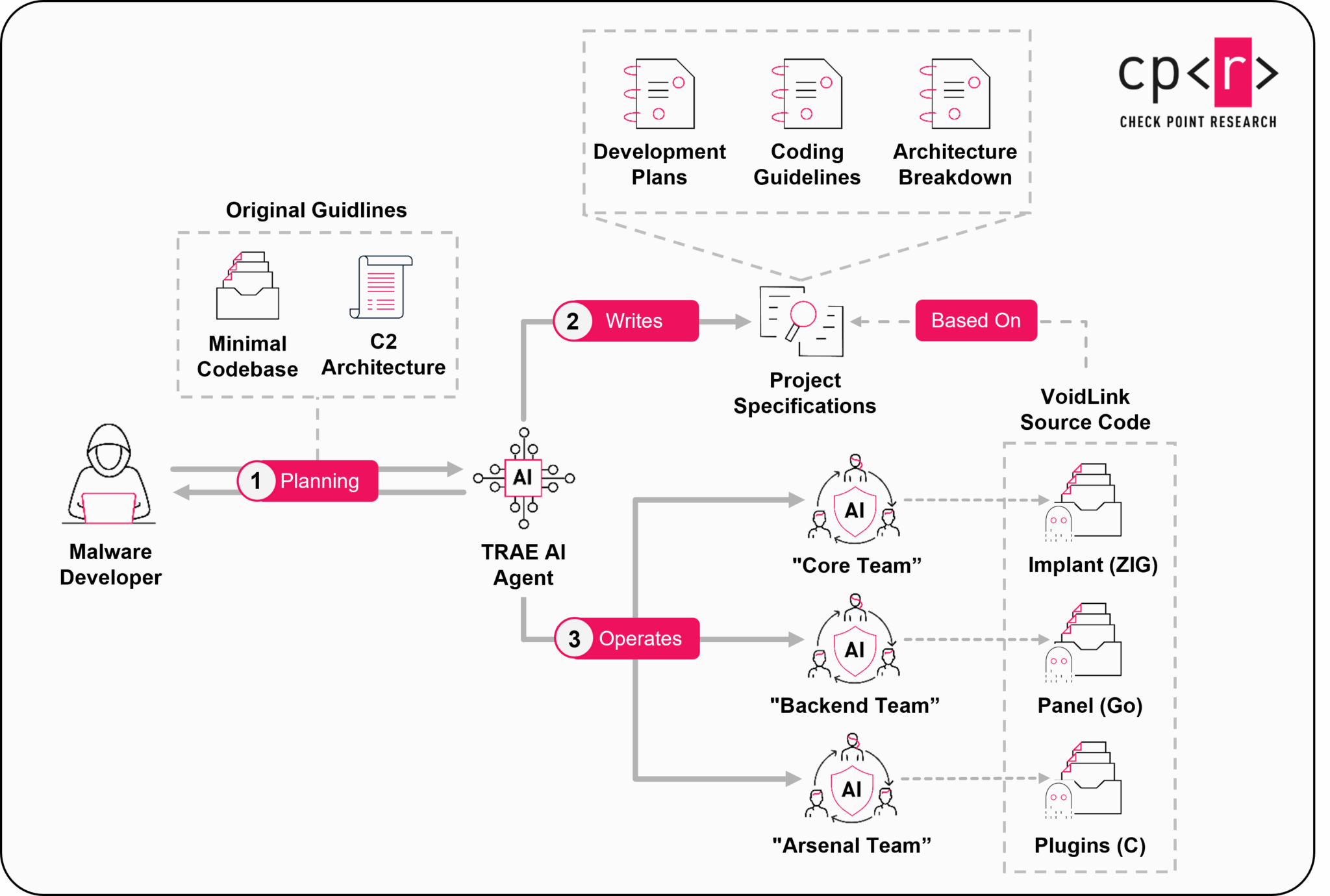
Recovered documents show the AI created elaborate sprint schedules with specific milestones, feature lists, and testing criteria. Each sprint produced working code that could be tested and refined before moving forward.
This approach allowed the developer to maintain quality control while letting AI handle the complex implementation work.
When Check Point researchers replicated the process using the same AI tools and documentation, they successfully recreated code that closely resembled the original VoidLink framework, confirming the AI-driven development theory.
The evidence leaves little doubt about how VoidLink came to exist, but it raises a troubling question: how many other sophisticated malware frameworks were built using similar AI methods without leaving discoverable traces?
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.