Handala Hackers Compromise Israeli Officials’ Telegram
Handala Hackers Compromise Israeli Officials’ Telegram Accounts Remember December 2025? That’s when the Iranian-linked hacking group Handala made a pretty bold claim. They announced...
Handala Hackers Compromise Israeli Officials’ Telegram Accounts
Remember December 2025? That’s when the Iranian-linked hacking group Handala made a pretty bold claim. They announced they’d completely compromised the mobile devices of two prominent Israeli political figures.
However, detailed analysis by Kela cyber intelligence researchers revealed a more limited scope—the breaches targeted Telegram accounts specifically, not complete device access.
The group claimed to have breached former Prime Minister Naftali Bennett’s iPhone 13 during Operation Octopus, releasing contact lists, photos, videos, and approximately 1,900 chat conversations.
Shortly after, they claimed similar access to Tzachi Braverman’s device, the Israeli Chief of Staff. Despite these dramatic claims, the actual breach exposed critical gaps in account security rather than device-level compromise.
Kela analysts conducted forensic examination of the leaked materials and identified that most of the exposed conversations were empty contact cards automatically generated by Telegram during synchronization.
Only about 40 conversations contained actual messages, with even fewer showing substantial exchanges. All exposed contacts linked to active Telegram accounts, confirming the data originated from Telegram itself.
Kela researchers and analysts noted that the incident highlighted serious vulnerabilities in session management and account security practices, even on encrypted messaging platforms.
Understanding the infection and account takeover mechanism reveals how Handala compromised these accounts without full device access.
The group likely employed multiple attack vectors including SIM swapping, where attackers assume control of the victim’s phone number to receive login verification codes.
They could also exploit SS7 protocol weaknesses in telecommunications infrastructure to intercept SMS messages at the network level. Additionally, Handala may have utilized sophisticated phishing campaigns that captured one-time passwords through fake login pages or malicious QR codes.
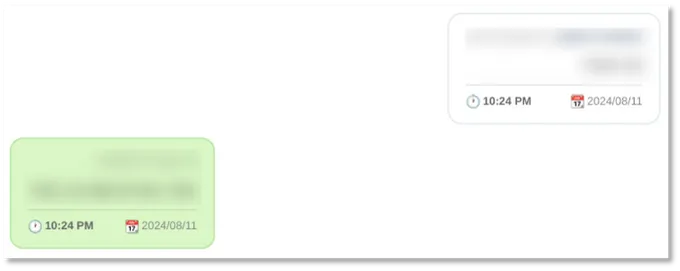
Session hijacking
Session hijacking represented another probable vector, where attackers copied the tdata folder from Telegram Desktop—the authentication file containing active session data that grants full account access when restored elsewhere, bypassing OTP and multi-factor authentication entirely.
The group’s operational approach also included harvesting OTP codes through multiple techniques: triggering verification via voice calls, extracting codes from voicemail by exploiting unchanged default PINs, or impersonating Telegram support to socially engineer staff into disclosing credentials.
Telegram’s default settings significantly amplified these risks. The cloud password feature remains optional and disabled by default, meaning possession of an OTP alone provides complete account access.
Standard chats lack end-to-end encryption, storing data on Telegram servers as cloud chats rather than locally, expanding the attack surface considerably.
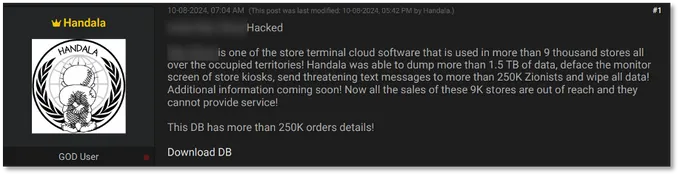
Handala first emerged in December 2023, establishing presence across multiple cybercrime forums and operating various Telegram channels and social media accounts.
Their operations primarily targeted Israeli companies and organizations, consistently demonstrating support for Iran and Palestinian causes throughout their campaigns, indicating state-sponsored or state-sympathetic motivations.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.