Hackers Use Hidden Mailbox Rules to Intercept M3 Create Microsoft
Cybercriminals are exploiting a sophisticated method to infiltrate corporate email accounts, silently intercepting all incoming and outgoing communications without the account owner’s...
Cybercriminals are exploiting a sophisticated method to infiltrate corporate email accounts, silently intercepting all incoming and outgoing communications without the account owner’s knowledge. This technique involves creating
Mailbox rules are a standard productivity feature inside Microsoft 365 and Outlook that help users automatically sort, forward, or delete incoming messages.
But when attackers gain unauthorized access to an account, they turn these rules into a persistent surveillance tool.
Once active, a malicious rule runs quietly in the background and acts on every incoming email based on conditions the attacker has set — forwarding sensitive messages to external addresses, hiding password reset notifications, or burying security alerts in folders the victim never checks.
Proofpoint researchers Anna Akselevich, Pavel Asinovsky, and Yaniv Miron identified this technique as one of the most consistent post-exploitation behaviors observed across cloud-based account takeovers.
Their analysis found that approximately 40% of compromised Microsoft 365 accounts had at least one malicious mailbox rule created shortly after the initial breach.
The shortest recorded time between an account compromise and rule creation was just eight seconds, clearly showing how deliberate and automated this tactic has become.
In Microsoft 365 environments, attackers typically gain their first foothold through credential phishing, password spraying, or OAuth consent abuse.
Rather than deploying malware or standing up external infrastructure, they rely on the platform’s native features to maintain access and stay hidden.
This makes detection significantly harder because all malicious activity runs entirely inside Microsoft’s own environment, using legitimate built-in functionality rather than any suspicious external tools.
The impact stretches well beyond individual accounts. From Business Email Compromise fraud to large-scale spam operations targeting university networks, attackers use hidden mailbox rules to operate undetected inside organizations for weeks or even months.
The technique works across all sectors and exploits the simple fact that most users never review their mailbox rule settings.
How Hidden Rules Operate Inside Compromised Accounts
Once inside a compromised account, attackers follow a repeatable and methodical process. They create mailbox rules using short, generic, or nonsensical names — nothing a real user would set — so the rules stay invisible to casual review.
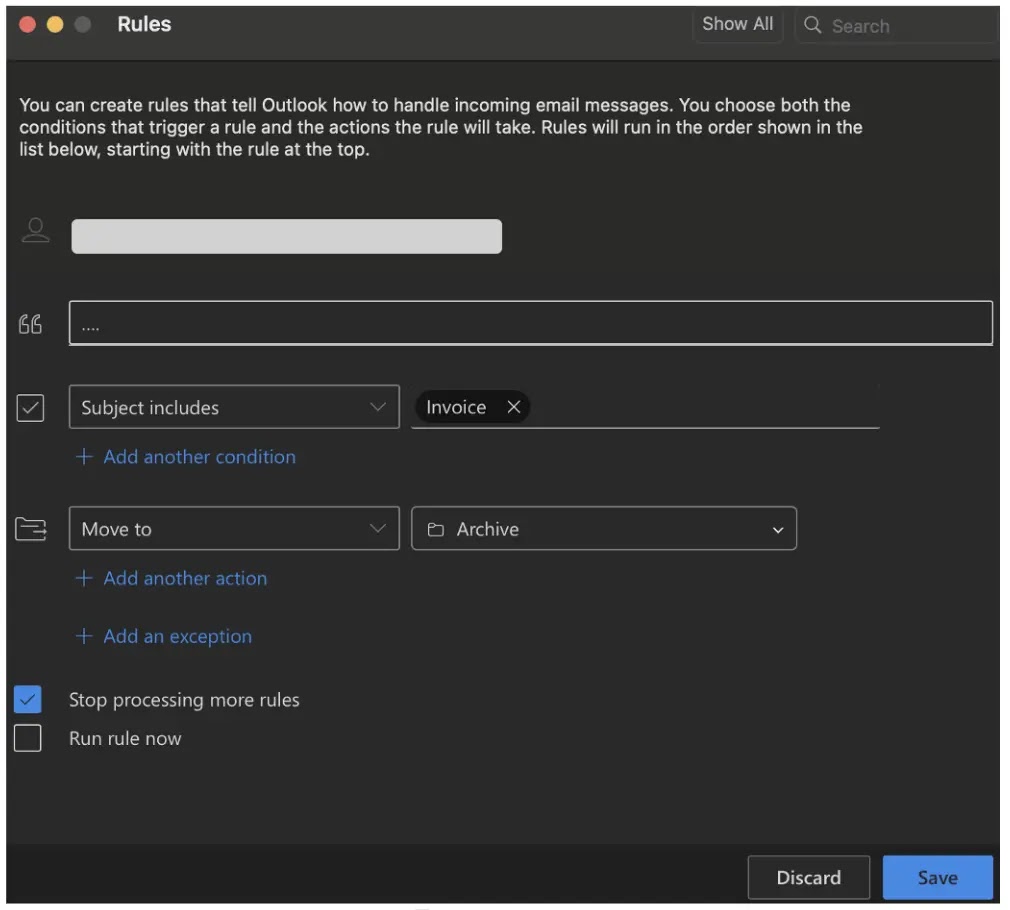
These rules achieve multiple goals at once. They silently forward emails containing financial keywords such as “invoice,” “wire,” or “contract” to attacker-controlled external addresses.
They hide MFA alerts, password reset emails, and suspicious login warnings so victims never realize their accounts have been breached. And because these rules survive password resets, they maintain persistent access long after credentials are changed.
In one documented payroll fraud scenario, an attacker compromised an account and immediately created a rule to archive any email containing “Payment List” in the subject line.
The attacker then used a third-party email platform called Zoho to register a spoofed domain built with homoglyph characters — letters designed to look nearly identical to those in the legitimate company domain.
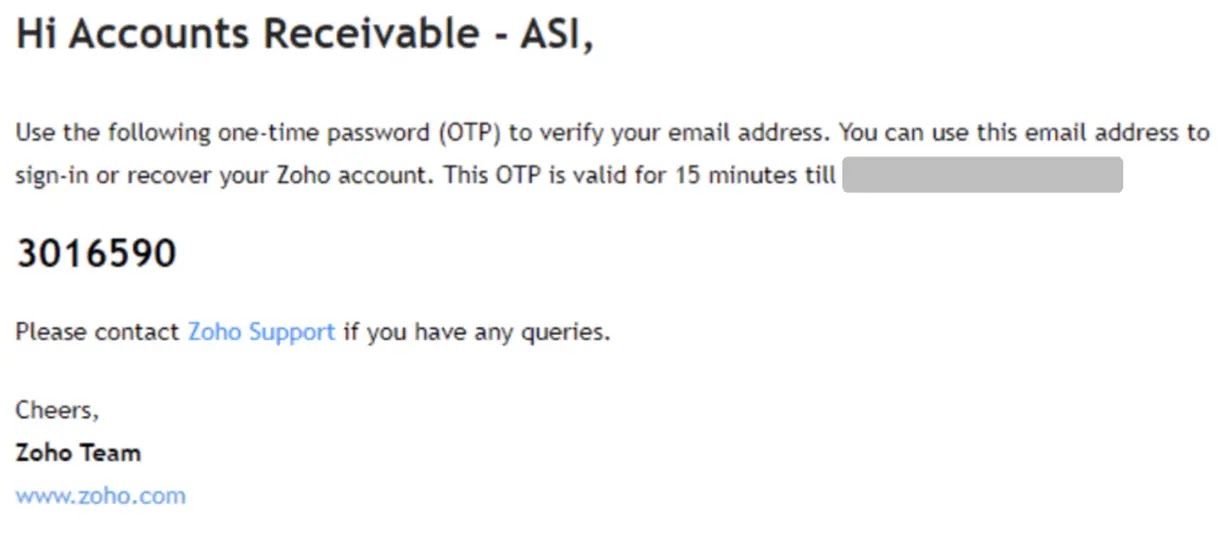
Since the mailbox rule was already active, every verification email from Zoho was automatically moved to a hidden folder, letting the attacker complete registration without the victim’s awareness.
From this external account, fraudulent messages were inserted into existing email threads to manipulate payment actions.
Security teams and organizations should take several steps to limit exposure.
Disabling automatic external forwarding in Exchange Online removes one of the most abused persistence paths. Enforcing multi-factor authentication with conditional access policies reduces the risk of initial account compromise.
Monitoring OAuth consent grants for suspicious application permissions, auditing mailbox rules on a regular schedule, revoking active sessions when a breach is detected, and reviewing Entra ID sign-in logs for unusual locations or risky authentication events are all critical actions for detecting and containing rule-based threats early.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.