Critical NGINX Vulnerability Allows Remote Code Execution –
Public disclosure has revealed a critical heap buffer overflow vulnerability within NGINX’s source code, present since 2008. Complete with a working proof-of-concept exploit capable of delivering...
Public disclosure has revealed a critical heap buffer overflow vulnerability within NGINX’s source code, present since 2008.
Complete with a working proof-of-concept exploit capable of delivering unauthenticated remote code execution (RCE) against one of the world’s most widely deployed web servers.
Assigned a CVSS score of 9.2, CVE-2026-42945 resides in NGINX’s ngx_http_rewrite_module.
This engine powers URL rewriting and variable assignment in virtually every modern NGINX deployment.
The bug was first introduced in version 0.6.27, released in 2008, and remained undetected for 18 years across all versions up to 1.30.0.
18-Year-Old NGINX RCE Vulnerability
The flaw is triggered when a configuration uses both rewrite and set directives together, a common pattern in API gateway setups.
NGINX’s internal script engine processes these directives using a two-pass system: the first pass calculates memory length, and the second writes data into the allocated buffer.
The critical flaw lies in a state mismatch between the two passes. When a rewrite directive contains a question mark (?), it permanently sets an is_args = 1 flag on the main script engine.
However, during the first (length calculation) pass, a zeroed-out sub-engine is used, meaning is_args is effectively zero. The length is calculated without accounting for URI escaping.
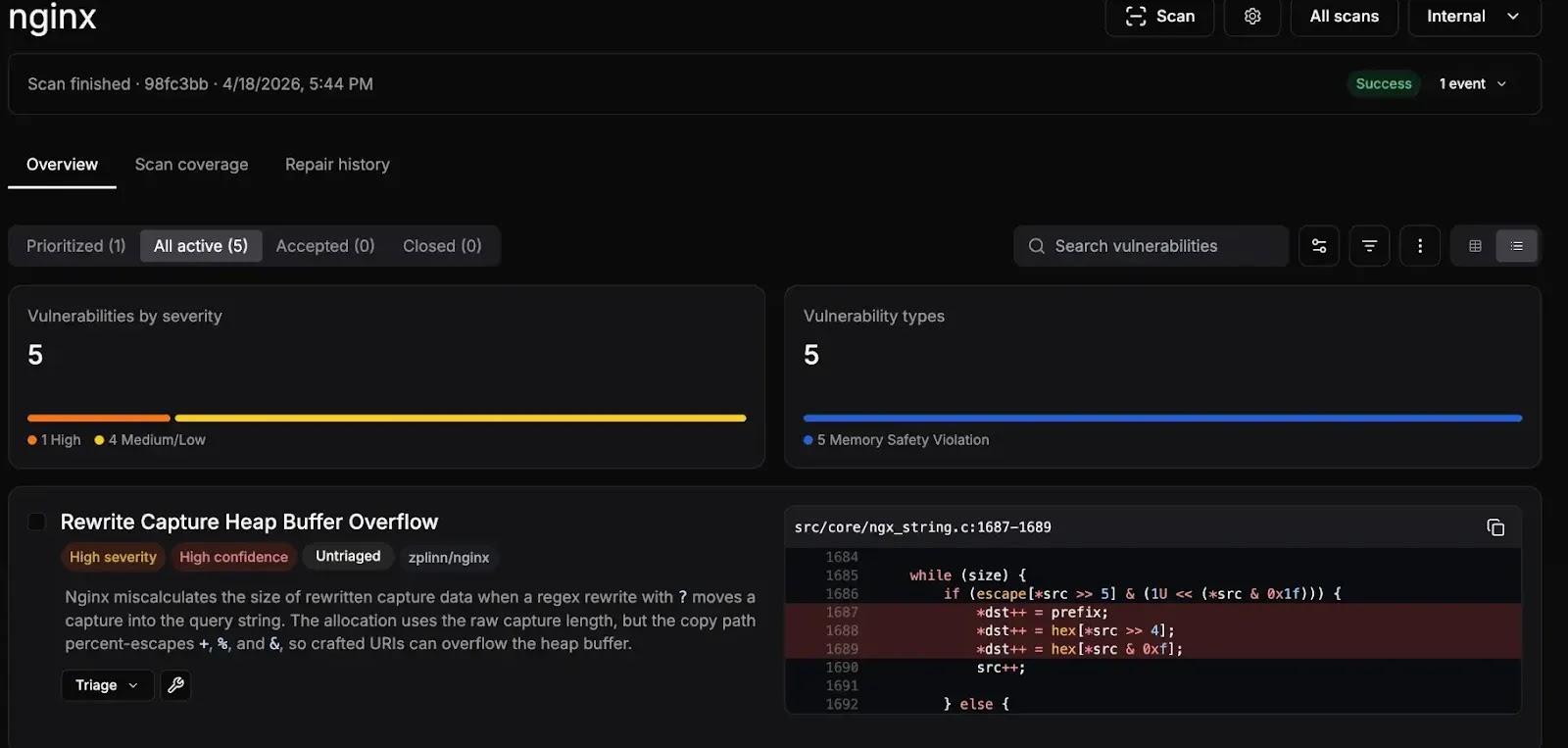
In the second (copy) pass, the main engine runs with is_args = 1, causing the ngx_escape_uri function to expand each escapable byte from 1 to 3 bytes.
The result: far more data is written to the buffer than was allocated, leading to a classic heap buffer overflow.
Researchers developed a working RCE exploit for systems with ASLR disabled.
The security research firm depthfirst autonomously discovered the vulnerability during an April 2026 code audit that also uncovered three additional memory corruption bugs.
The attack chains heap manipulation, fake cleanup structure spraying via POST bodies, and NGINX’s deterministic multi-process architecture to achieve reliable, repeatable code execution. A public PoC is now available on GitHub.
Three additional CVEs were confirmed alongside the critical flaw:
The vulnerability impacts a wide range of F5/NGINX products, including NGINX Open Source 0.6.27–1.30.0, NGINX Plus R32–R36, NGINX Instance Manager, NGINX App Protect WAF, NGINX Gateway Fabric, and NGINX Ingress Controller.
F5 released its official security advisory on May 13, 2026. Administrators should upgrade to NGINX 1.30.1 or 1.31.0 immediately.
Organizations that cannot patch right away should audit configurations for combined rewrite + set directive usage and consider restricting exposed NGINX deployments behind an additional WAF layer until patching is complete.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.







No Comment! Be the first one.