Hackers Push CrystalX Malware-as-a-Service Through Telegram With
CrystalX, a potent new Malware-as-a-Service (MaaS) offering, is now openly marketed to cybercriminals via private Telegram channels. This dangerous malware, detailed in CrystalX did not appear out of...
CrystalX, a potent new Malware-as-a-Service (MaaS) offering, is now openly marketed to cybercriminals via private Telegram channels. This dangerous malware, detailed in
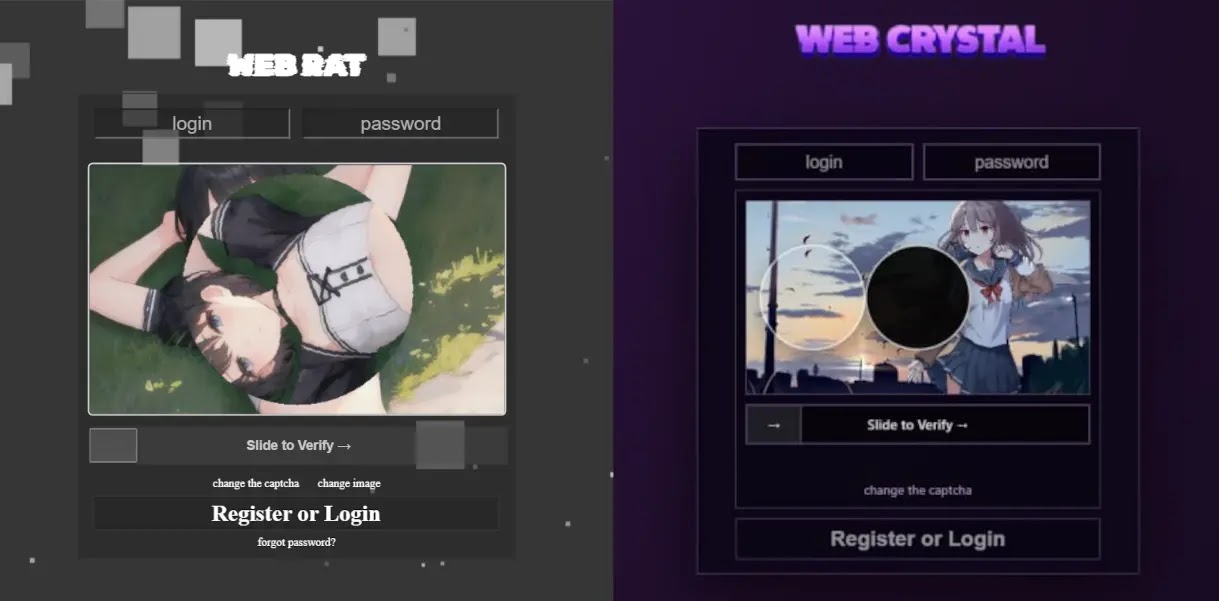
CrystalX did not appear out of nowhere. It traces its roots back to January 2026, when a malware author began promoting a tool called Webcrystal RAT inside a private Telegram group used by RAT developers.
Early observers noted that the control panel layout looked nearly identical to a previously known tool called WebRAT, also referred to as Salat Stealer.
Both were written in Go, and the bot used to sell access keys closely matched the WebRAT infrastructure.
After receiving criticism that the tool was simply a copy, the developer rebranded it as CrystalX RAT, opened a dedicated Telegram channel packed with marketing activity including access key draws and polls, and even launched a YouTube channel to showcase the malware’s growing feature list.
Securelist analysts identified the active campaign and carried out a detailed technical analysis of the malware, noting that its feature set goes well beyond what most commercial RATs offer.
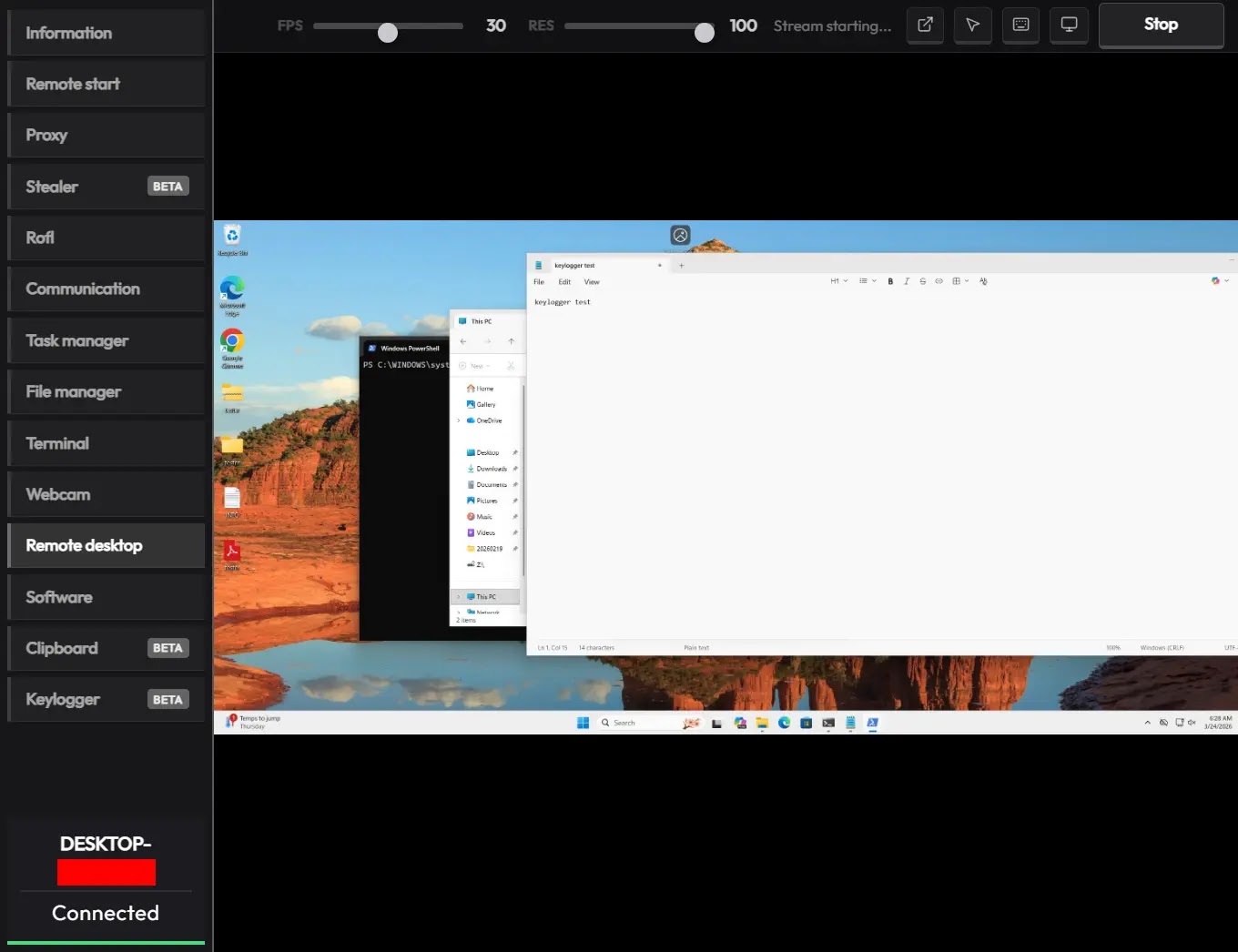
The tool is sold in three subscription tiers, giving buyers access to a web-based control panel filled with capabilities ranging from file exfiltration to live remote screen control.
What stands out most is the combination of serious espionage functions alongside an entire section of prank commands designed to harass and disrupt victims on demand. This unusual pairing makes CrystalX one of the more distinct threats seen in the MaaS space in recent months.
The malware’s reach is already growing. At the time of reporting, dozens of victims had been affected, with infection attempts recorded primarily in Russia.
CrystalX, however, carries no built-in geographic restrictions, meaning any subscriber can deploy it against targets anywhere in the world.
Kaspersky’s products detect this threat under multiple signatures, including Backdoor.Win64.CrystalX, Trojan.Win64.Agent, and Trojan.Win32.Agentb.gen.
Continued development of new implant versions signals that the malware is still being actively improved, and its subscriber base is likely to grow as the attacker ramps up promotional efforts.
Detection Evasion and Anti-Analysis Tactics
One of the more technically refined aspects of CrystalX is how it works to avoid detection.
Each implant is compressed using zlib and then encrypted with the ChaCha20 algorithm, using a hard-coded 32-byte key and a 12-byte nonce, which makes static analysis significantly harder.
The auto-builder provided with the control panel allows operators to configure anti-analysis features at the build stage, including selective geoblocking by country and custom executable icons.
During execution, CrystalX runs a series of checks to determine whether it is operating in an analysis environment.
It reads a Windows registry value to detect if a proxy tool such as Fiddler, Burp Suite, or mitmproxy is active, and blacklists their process names accordingly.
A separate virtual machine detection routine examines running processes, installed guest tools, and hardware characteristics to confirm it is indeed running on a real system.
An anti-attach loop continuously monitors the debug flag, debug port, hardware breakpoints, and program execution timing to catch any debugger attachment attempt.
Additionally, the malware patches critical Windows functions, including AmsiScanBuffer, EtwEventWrite, and MiniDumpWriteDump, disabling security instrumentation and memory dumping tools that analysts regularly rely on during investigations.
Once it clears these checks, CrystalX connects to its command-and-control server via a hard-coded WebSocket URL and begins collecting system data.
The known C2 domains are webcrystal.lol, webcrystal.sbs, and crystalxrat.top. Organizations should block these domains at the network perimeter, monitor for unusual outbound WebSocket connections, and investigate any executable displaying the anti-debug behaviors described above.
Keeping endpoint protection tools regularly updated remains one of the most practical steps to catch threats like CrystalX before they can establish a foothold.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.