Hackers Launched 8.1 Million React2Shell Attack Sessions Vulnerability
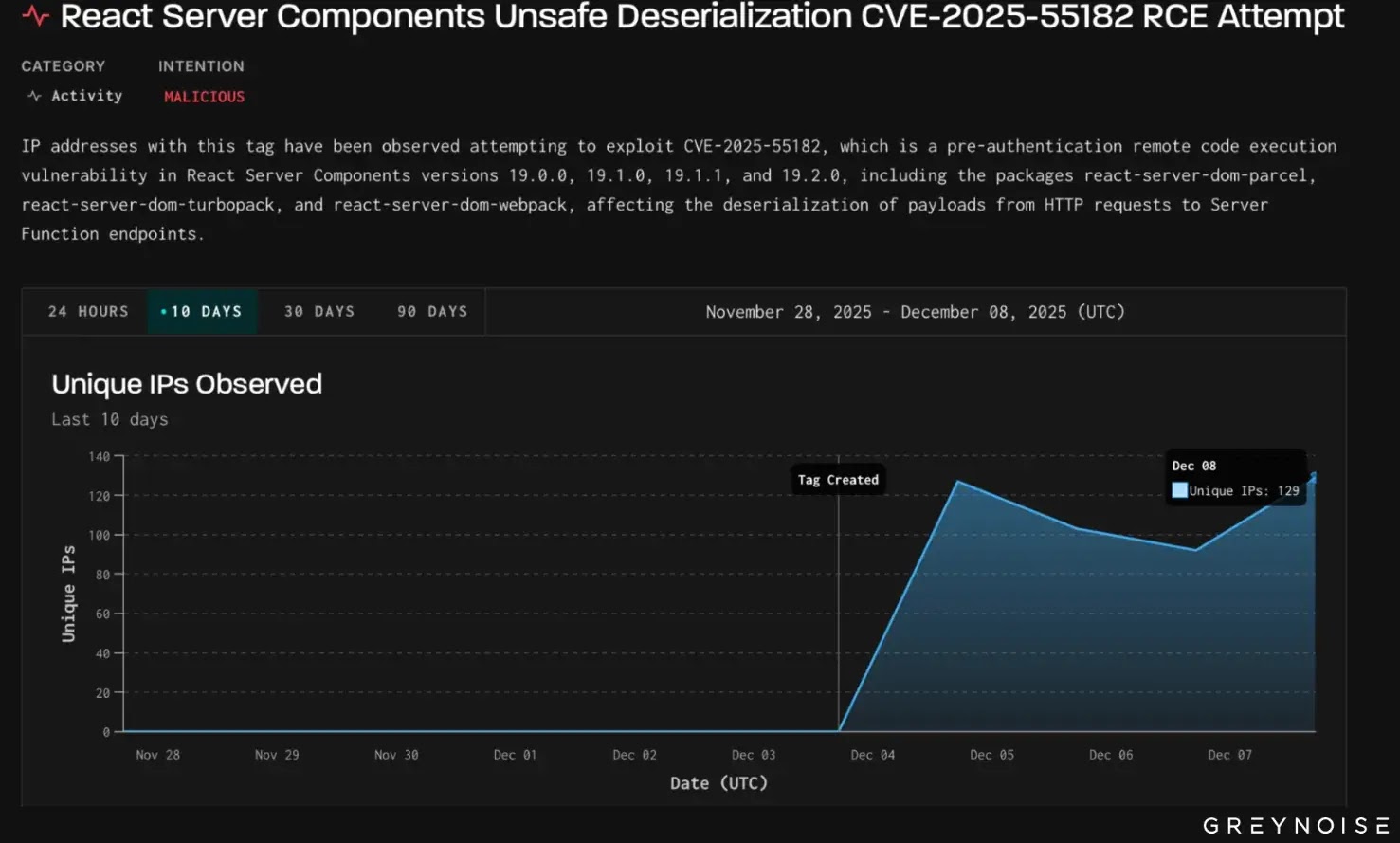
The React2Shell Attack Sessions Vulnerabilitytargeting the flaw since its initial disclosure. According to GreyNoise Observation Grid data, daily attack volumes have stabilized at 300,000–400,000...
The React2Shell Attack Sessions Vulnerabilitytargeting the flaw since its initial disclosure.
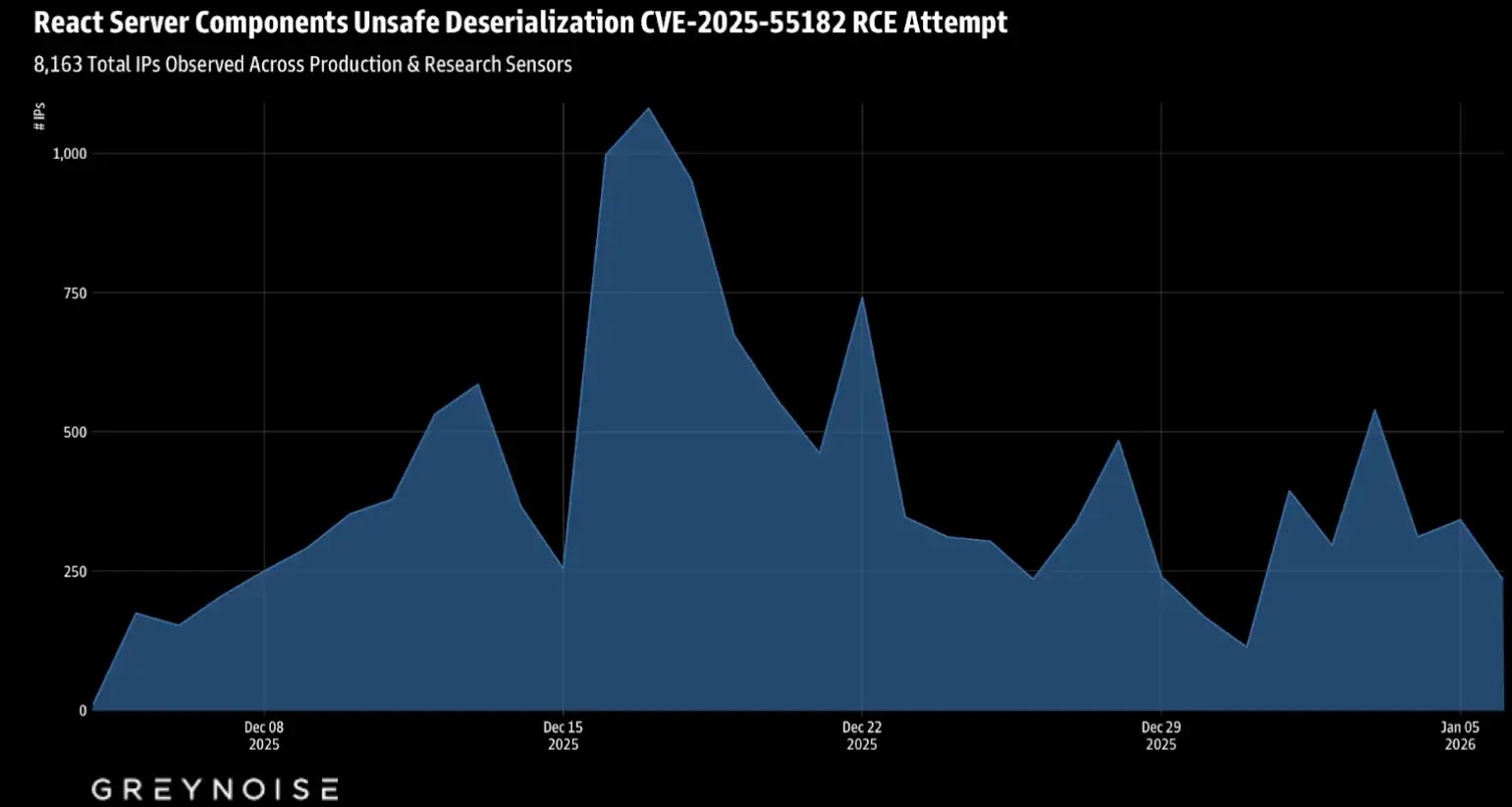
According to GreyNoise Observation Grid data, daily attack volumes have stabilized at 300,000–400,000 sessions since peaking above 430,000 in late December, indicating sustained, coordinated exploitation.
 Million React2Shell Attackhave been seen since the start.”>
Million React2Shell Attackhave been seen since the start.”>Scale of the Exploitation Campaign
The campaign’s infrastructure footprint reveals a sophisticated, distributed operation. Researchers have identified 8,163 unique source IP addresses spanning 1,071 autonomous systems (ASNs) across 101 countries.
This geographic dispersion underscores the vulnerability’s appeal across diverse threat actor ecosystems, from exploitative botnets to advanced persistent threat groups. AWS and other major cloud providers dominate the attack infrastructure.
Amazon Web Services alone accounts for over one-third of observed exploitation traffic, with the top 15 ASNs comprising approximately 60% of all source IPs.
This reflects attackers’ preference for leveraging legitimate cloud infrastructure to mask malicious activity. Attackers have created over 70,000 unique payloads, demonstrating continuous experimentation and refinement.
Network fingerprint analysis reveals 700 distinct JA4H hashes (HTTP client fingerprints) and 340 unique JA4T hashes (TCP stack fingerprints), indicating varied tooling and delivery mechanisms.
Payload Diversity and Attack Patterns
Exploitation follows a predictable two-stage approach. Initial reconnaissance probes validate command execution via simple PowerShell arithmetic operations before proceeding to deliver an encoded payload.
Stage-two exploits employ AMSI bypass techniques, enabling attackers to execute additional malicious scripts while evading antivirus detection.
Organizations remain exposed if unpatched. Nearly 50% of observed source IPs were first observed after July 2025, indicating a recent infrastructure allocation and rapid IP rotation.
Static IP blocklists are insufficient to address this campaign’s scale and velocity. Defenders should implement dynamic blocking through GreyNoise’s continuously updated threat intelligence feeds.
Endpoint monitoring should focus on detecting PowerShell execution patterns, encoded commands, and AMSI modifications via reflection.
Organizations managing exposed React Server Components should treat this as an active, ongoing threat requiring immediate patching and network-level protection.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.